Every employee who touches client data is a potential point of failure, or a line of defence. For regulated businesses in Australia, particularly accounting and financial services firms, data privacy training for employees isn’t optional. It’s a direct requirement under the Australian Privacy Act 1988, and with upcoming AUSTRAC AML/CTF obligations tightening the screws further, the stakes are only getting higher.
Yet most firms treat privacy training as a tick-box exercise. A yearly slide deck, a signature on a policy document, and back to business as usual. That approach leaves gaps, gaps that lead to data breaches, regulatory penalties, and broken client trust. A proper training program goes beyond awareness. It builds habits, clarifies responsibilities, and gives your team the practical knowledge they need to handle personal information correctly, every single day.
This guide walks you through how to build a data privacy training program that actually works for your team. We cover what to include, how to deliver it, and how to keep it current as regulations evolve. We also look at how the tools your team already uses matter just as much as the training itself, which is exactly why we built StackGo’s integrations with a dedicated Privacy Layer, ensuring PII stays protected and never lingers in your CRM where untrained eyes might access it. Good training and good systems work hand in hand.
What good data privacy training covers in Australia
Before you build a single training module, you need a clear picture of what effective data privacy training for employees looks like in an Australian context. The foundation is the Australian Privacy Act 1988 and its 13 Australian Privacy Principles (APPs), which govern how organisations collect, store, use, and disclose personal information. If your firm handles personal information, and virtually every business in Australia does, these principles are not background reading. They are the legal baseline your team must understand and apply.
The Australian Privacy Principles in plain terms
The 13 APPs cover everything from how you notify individuals when you collect their data to how you handle cross-border data transfers and respond to access requests. Most employees will never read the legislation directly, which is why your training needs to translate legal obligations into plain-language expectations tied to each person’s actual role. An accounts receivable officer needs to understand APP 1 (transparency) and APP 11 (data security). A client-facing consultant needs to understand APP 5 (collection notices) and APP 12 (access and correction).
Your training program fails if employees can recite the APPs but cannot apply them to a real client interaction.
For accounting firms specifically, the Tax Practitioners Board (TPB) requires that practitioners maintain appropriate data security practices as a condition of registration. On top of that, AUSTRAC’s expanding AML/CTF obligations will require many firms to implement formal customer due diligence and record-keeping processes. Both carry training implications that go well beyond a generic privacy awareness session.
Core topics every employee must cover
Good training does not try to teach everyone everything at once. Instead, it ensures all staff share a common foundation, then layers in role-specific detail on top. Here are the core topics that belong in any Australian workplace privacy program:
- Personal information defined: What counts as personal information under the Privacy Act, including sensitive categories like health records, financial details, and biometric data
- Collection and consent: When you can collect personal information, what notice you must provide, and when explicit consent is required
- Data minimisation: Only collecting what you genuinely need for a stated purpose, nothing more
- Storage and access controls: How personal information must be stored, who can access it, and what access logs should exist
- Breach identification and response: How to recognise a notifiable data breach and the steps to take within the first 24 hours under the Notifiable Data Breaches scheme
- Third-party sharing: When it is lawful to share data with partners, contractors, or offshore processors
- Individual rights: How to handle access requests, correction requests, and formal complaints
What regulated industries need beyond the basics
If your business operates in a regulated sector, such as accounting, financial services, legal, or commercial real estate, your training requirements go beyond standard Privacy Act obligations. AUSTRAC-regulated firms need staff who understand KYC and AML verification processes, including how to verify client identity correctly, when to file a suspicious matter report, and how long to retain identity records under the law.
Your training also needs to address the systems your team uses every day. If client data sits in a CRM like HubSpot or Salesforce, employees need to understand what information should and should not be stored there, who holds access rights, and what happens when a staff member leaves the organisation. Covering the legal framework without covering the tools that actually hold the data leaves a significant gap in your program.
Step 1. Set your scope and risk profile
The most common mistake firms make is building a training program before they know who it is for or what risks it needs to address. Setting your scope first saves you from producing generic content that nobody applies, and it ensures your data privacy training for employees is proportionate to the actual risk your business carries. Before you write a single learning objective, answer two questions: who handles personal information in your organisation, and what categories of data do they touch?

Define who is in scope
Not everyone in your organisation carries the same privacy risk. A client-facing accountant who collects tax file numbers and financial records sits at a very different risk level than an internal IT administrator who manages system access. Your first task is to list every role in the business and assign it a privacy exposure level: high, medium, or low.
Use this framework to get started:
| Role type | Typical exposure | Example roles |
|---|---|---|
| High | Direct access to client PII, financial data, or identity documents | Client managers, compliance officers, bookkeepers |
| Medium | Indirect access or occasional handling of personal data | Admin staff, project coordinators |
| Low | Minimal or no access to personal information | Internal marketing, operations support |
This role mapping becomes the backbone of your training structure in Step 4, so take the time to get it right before you move forward.
Identify which regulations apply
Once you know who is in scope, you need to confirm which legal obligations govern your business. All Australian businesses covered by the Privacy Act 1988 must comply with the 13 Australian Privacy Principles. However, if your firm is also regulated by the Tax Practitioners Board or falls under AUSTRAC’s AML/CTF framework, your obligations extend further and require specific, documented training processes.
If your firm is onboarding regulated entities as clients, your training program needs to reflect that, not just the base Privacy Act requirements.
Write down every regulator that has oversight of your business and the specific training requirements attached to each one. This list becomes your compliance checklist and sits at the top of your program design document before you move to any content creation.
Step 2. Map personal information flows
Once you know your scope and risk profile, the next step is to trace exactly where personal information enters your business, how it moves through your systems, and where it eventually leaves or gets deleted. A personal information flow map gives your training program a concrete foundation. Without it, you are training people on abstract principles rather than on the real-world data journeys that happen inside your organisation every single day.
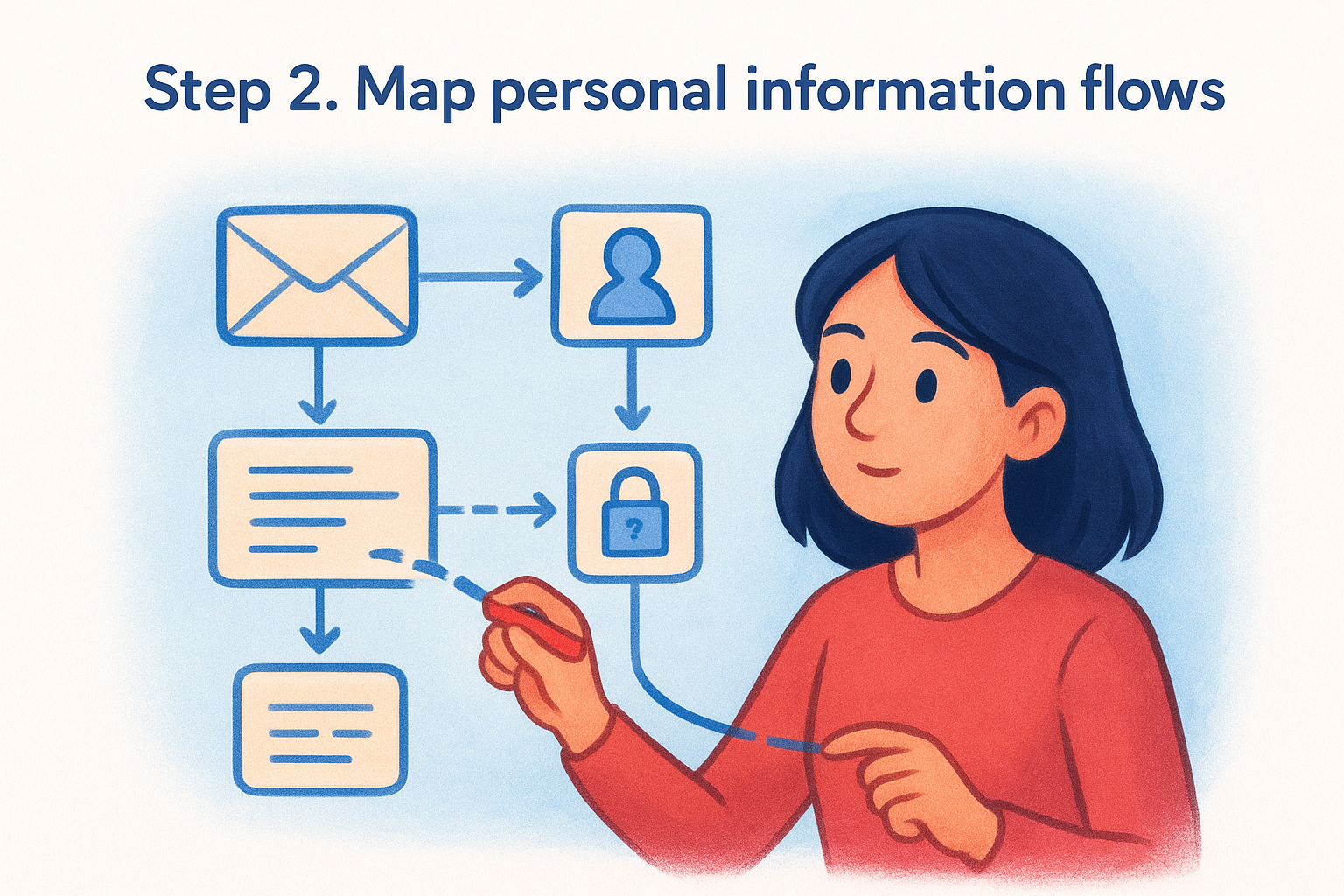
Trace every point of entry
Personal information enters your business through more channels than most firms realise. Client onboarding forms, email correspondence, identity verification checks, payroll systems, and third-party software integrations all bring personal information into your environment. Your job at this stage is to list every channel and then follow the data forward from there.
For each entry point, record:
- What data is collected (name, TFN, date of birth, identity document numbers)
- Who collects it and in what system it first lands
- Why it is collected and the legal basis under the Privacy Act for doing so
If you cannot state a clear legal basis for collecting a piece of information, that is a gap your training program needs to address before it becomes a compliance problem.
Document storage, access, and disposal
After mapping entry points, you need to capture where data lives, who can access it, and how long it is retained. This is where most firms find their biggest surprises. Data collected for one purpose quietly accumulates in a CRM, a shared drive, or an email thread with no clear owner or deletion schedule.
Use this template as a starting point for your flow map:
| Data type | Entry point | System stored | Who has access | Retention period | Disposal method |
|---|---|---|---|---|---|
| Client TFN | Onboarding form | CRM / accounting software | Client manager, compliance officer | 7 years (ATO requirement) | Secure deletion |
| Identity documents | KYC verification | Identity verification tool | Compliance officer only | 7 years (AUSTRAC) | Secure deletion |
| Employee payroll data | HR onboarding | Payroll system | HR manager, payroll admin | 7 years | Secure deletion |
Once this map exists, your data privacy training for employees becomes significantly more targeted. Rather than teaching everyone the same generic lessons, you can point each team member to the specific data flows relevant to their role and show them exactly where the risks sit.
Step 3. Write clear policies and playbooks
A personal information flow map tells you where your risks sit. Clear policies and playbooks translate that knowledge into written rules your team can actually follow. Without documented procedures, your data privacy training for employees relies on memory and good intentions, and that is not a compliance strategy. Your policies become the reference point employees return to when they face a real decision about data, and your playbooks walk them through exactly what to do when something goes wrong.
Build a privacy policy employees actually read
Most workplace privacy policies are written by lawyers for lawyers. Your staff will not read them, and if they do, they will not retain anything useful. Rewrite your internal privacy policy in plain language, organised around the tasks your team actually performs. Aim for a maximum of two pages for the core document, with linked annexures for role-specific detail.
A policy that sits in a shared drive and never gets opened provides no legal or practical protection.
Each section of your policy should answer one clear question: what should I do when [situation]? Cover the following at minimum:
- How to collect personal information and what notice to provide to the client
- Which systems are approved for storing PII and which are not
- Who is authorised to access specific categories of data
- How long to retain records and the correct method for secure disposal
- What to do immediately if you suspect a data breach has occurred
Create incident response playbooks
Policies set the rules; playbooks provide the steps. An incident response playbook removes the guesswork when your team encounters a potential data breach. Every minute of delay in a breach response increases your regulatory exposure under the Notifiable Data Breaches scheme, so your playbook needs to be specific and fast to execute. Distribute it separately from your main policy document so staff can locate it instantly under pressure.
Use this template as your starting point:
| Step | Action | Owner | Timeframe |
|---|---|---|---|
| 1 | Contain the breach (revoke access, isolate affected systems) | IT / Operations | Immediate |
| 2 | Assess what data was affected and how many individuals | Compliance officer | Within 1 hour |
| 3 | Notify the Privacy Officer or senior decision-maker | All staff | Within 2 hours |
| 4 | Determine if the breach is notifiable under the NDB scheme | Compliance officer | Within 24 hours |
| 5 | Notify the OAIC and affected individuals if required | Privacy Officer | Within 30 days |
Step 4. Build role-based training modules
Your role mapping from Step 1 and your flow map from Step 2 now give you everything you need to build targeted training modules rather than a single generic program everyone sits through once. Role-based data privacy training for employees is significantly more effective because it connects legal obligations to the actual tasks each person performs every day. A bookkeeper who understands exactly how to handle a client’s tax file number during data entry is far better prepared than one who has memorised the APPs in the abstract.
Define a core module every employee completes
Start with a single foundation module that every person in the business completes, regardless of role. This module covers the non-negotiable basics: what personal information is under the Privacy Act, how the Notifiable Data Breaches scheme works, and how to recognise and report a suspected breach. Keep it to 30 minutes or less. If your foundation module runs longer, you are including role-specific content that belongs elsewhere.
The foundation module is not a compliance certificate. It is a shared language that ensures every employee understands their minimum responsibilities before they handle a single piece of client data.
Use this structure for your foundation module:
| Module section | Content | Estimated time |
|---|---|---|
| What is personal information | Definitions, examples, sensitive categories | 5 minutes |
| The Privacy Act and your obligations | APPs in plain language, TPB and AUSTRAC context | 10 minutes |
| Recognising and reporting a breach | NDB scheme, internal escalation process | 10 minutes |
| Knowledge check | 5-question scenario-based quiz | 5 minutes |
Build role-specific modules on top
Once every employee completes the foundation module, add a second layer of training tied directly to each role’s exposure level from your Step 1 risk mapping. High-exposure roles need the most detailed modules. A client manager at an accounting firm, for example, needs specific instruction on collecting TFNs, conducting identity verification under AUSTRAC requirements, handling client access requests, and managing data inside the CRM.
Assign modules using this structure:
- High exposure roles: Foundation module + KYC/AML verification process + CRM data handling + breach response drill
- Medium exposure roles: Foundation module + data minimisation practices + third-party sharing rules
- Low exposure roles: Foundation module only, with annual refresher
Each module should include at least one scenario-based question that places the employee in a realistic situation rather than asking them to recall a definition. Scenarios produce better retention and give you a clearer picture of whether the training is actually landing.
Step 5. Deliver training and track completion
Building modules is only half the job. How you deliver data privacy training for employees and how you prove completion to a regulator are equally important. The Office of the Australian Information Commissioner expects organisations to demonstrate that staff have received documented, role-appropriate training, not just that a program exists somewhere on a shared drive.
Choose your delivery method
Your delivery method should match the size and structure of your team. Small firms with under 20 staff can run live sessions facilitated by a compliance officer or external consultant, which gives employees a chance to ask questions in context. Larger teams benefit from a Learning Management System (LMS), which lets you assign modules by role, set completion deadlines, and pull completion reports automatically.
Choose a delivery method you can actually sustain. A live session you run once is worse than a short recorded module your team completes annually.
If you use an LMS, platforms like Microsoft SharePoint or purpose-built compliance tools allow you to host recorded modules, attach policy documents, and capture quiz scores in one place. For firms without a dedicated LMS, a structured Google Workspace folder with recorded videos, policy PDFs, and a linked Google Form quiz can serve the same function at minimal cost. The format matters less than the consistency of delivery and the records you retain.
Track completion and keep records
Regulators and auditors will ask for evidence of training completion, not a verbal assurance that it happened. Build a simple tracking record from day one and update it every time a module is completed or a new employee is onboarded. Store this record in a location that survives staff turnover, not in someone’s personal inbox.
Use this tracking template as your baseline:
| Employee name | Role | Foundation module | Role module | Completion date | Quiz score | Refresher due |
|---|---|---|---|---|---|---|
| Jane Smith | Client manager | Complete | Complete | 2026-02-14 | 90% | 2027-02-14 |
| Tom Nguyen | Admin | Complete | N/A | 2026-02-14 | 80% | 2027-02-14 |
Record the date, the module completed, and the score for every employee. For AUSTRAC-regulated firms, retention of training records for at least seven years is consistent with broader AML/CTF record-keeping obligations, so build that requirement into your file management process from the start.
Step 6. Test, refresh, and respond to incidents
A training program that never gets tested is a program you cannot trust. Completion certificates and quiz scores tell you whether employees sat through the material, not whether they can apply it when a real situation arises. This final step closes the loop by building in regular testing, scheduled refreshes, and structured incident response practice that keep your data privacy training for employees sharp over time.
Run scenario-based tests
The most reliable way to check whether training has landed is to put employees in a simulated situation and observe what they do. Scenario tests do not need to be elaborate. A short written scenario sent via email, asking the employee to explain what action they would take, tells you far more than a multiple-choice quiz built around definitions.
If employees consistently fail the same scenario, that is a signal to rework the module, not just re-run it.
Use this testing template once per quarter for high-exposure roles:
| Scenario | What you are testing | Pass criteria |
|---|---|---|
| A client emails their TFN in plain text | Data minimisation and secure storage | Employee flags it and moves data to an approved system |
| A staff member finds an unlocked screen with client data visible | Physical access controls | Employee locks the screen and reports to the compliance officer |
| An unknown third party requests client records by phone | Third-party sharing rules | Employee declines and escalates to the compliance officer |
Schedule annual refreshes
Privacy regulations change, and so do the systems your team uses every day. Build a fixed annual review date into your program calendar from the outset. Each year, revisit your personal information flow map from Step 2, check whether new tools or integrations have been introduced, and update modules to reflect regulatory changes such as AUSTRAC guideline updates or amendments to the Privacy Act.
Refreshes do not require rebuilding from scratch. A short 15-minute updated module covering what has changed, followed by a revised scenario test, is enough to keep your team current without cutting into their client workload.
Practice your incident response
Reading a breach response playbook and executing one under pressure are two very different skills. Once per year, run a tabletop exercise where you walk your compliance officer and relevant staff through a simulated breach from detection to notification. Assign roles, set a timer, and debrief on where the response stalled or slowed down. Your playbook from Step 3 becomes the script for this exercise.
This practice builds genuine confidence in your team and surfaces gaps in your documented procedures before a real breach forces you to find them.
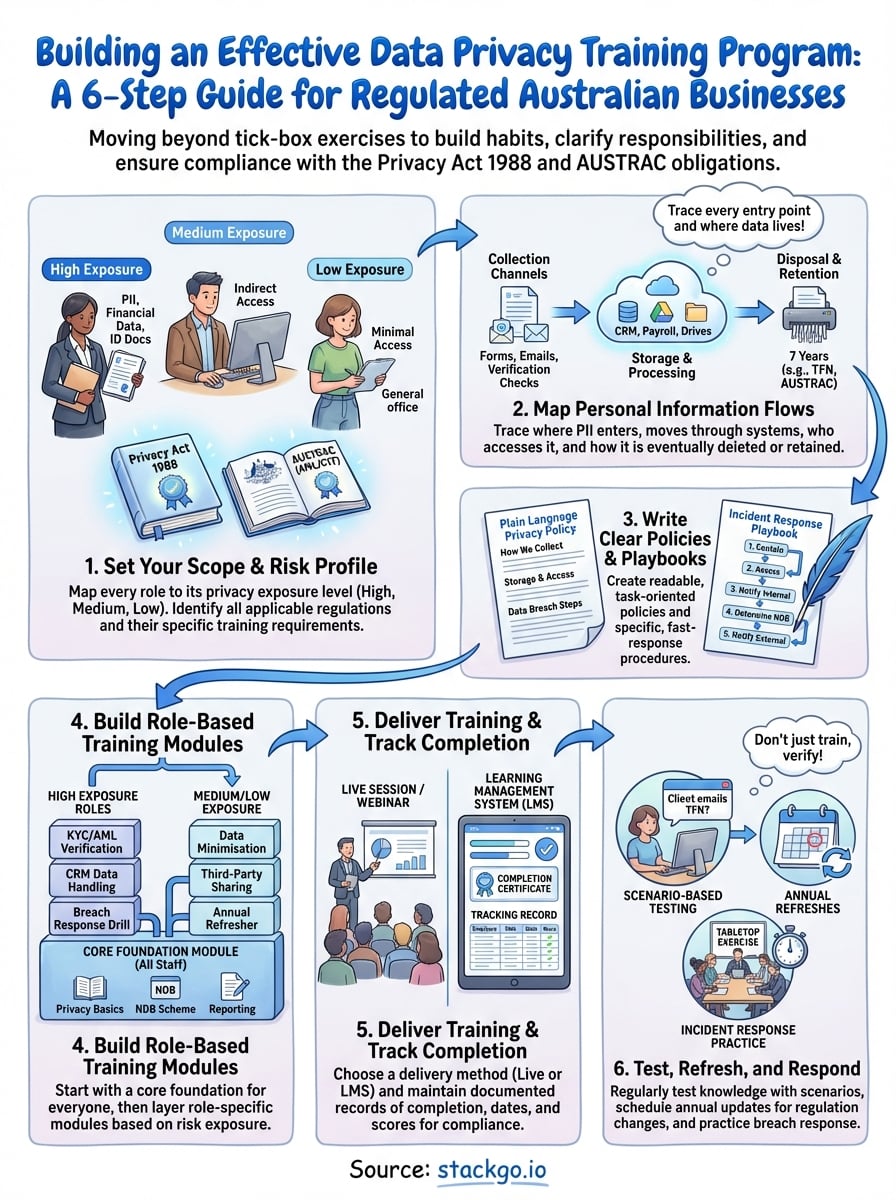
Finish with a program you can run
Data privacy training for employees is not a project you complete once and archive. It is a repeating cycle of scoping, mapping, documenting, training, testing, and refreshing. The six steps in this guide give you a structured path from nothing to a documented, role-based program that holds up under regulatory scrutiny and actually changes how your team handles personal information day to day.
Training your people is one half of the equation. The systems they use every day are the other half. If personal information sits unsecured inside your CRM after a verification check, your training investment is working against a leaky process. StackGo’s IdentityCheck solves this directly, running identity verification inside your existing software with a built-in Privacy Layer that keeps PII out of your CRM entirely. See how IdentityCheck handles AUSTRAC Tranche 2 compliance inside the tools your team already uses.









