When a client submits their details through your onboarding form, how do you know they are who they claim to be? This question sits at the heart of identity verification definition discussions across regulated industries. For accountants, lawyers, and financial services professionals, verifying a person’s identity isn’t optional, it’s a legal requirement under frameworks like the Tax Practitioners Board regulations and the upcoming AUSTRAC AML/CTF obligations.
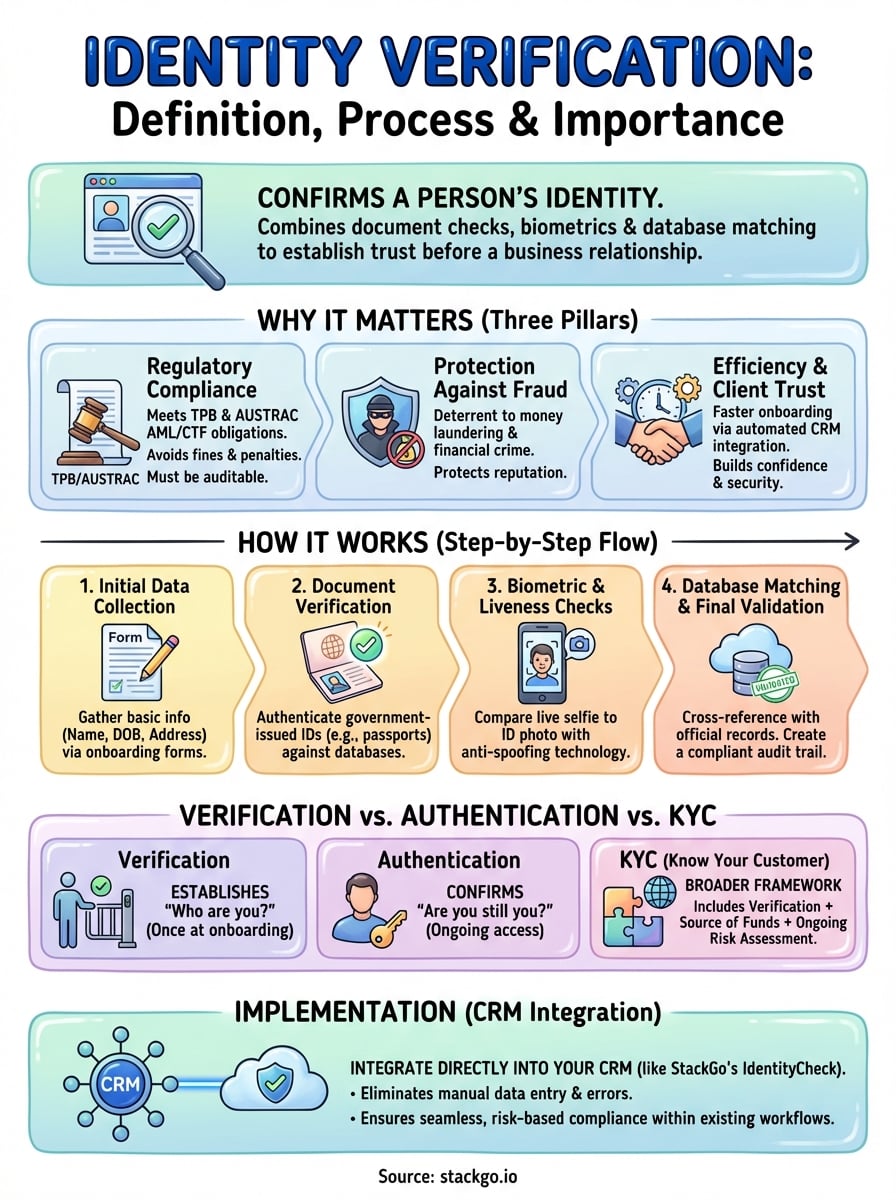
Identity verification is the process of confirming that an individual is genuinely who they present themselves to be. It combines document checks, biometric analysis, and database matching to establish trust before a business relationship begins. Getting this right protects your practice from fraud, money laundering, and regulatory penalties.
At StackGo, we build integration tools like IdentityCheck that bring verification directly into your existing CRM, no separate systems, no manual data entry. This article explains what identity verification means, how the process works, and why it matters for your compliance obligations.
Why identity verification matters for businesses
Your practice handles sensitive client information every day, and a single verification failure can expose you to regulatory penalties or reputational damage. Understanding the identity verification definition in practical terms means recognising its role as the first line of defence against fraud, compliance breaches, and operational inefficiencies. For Australian accounting firms and professional services, verification isn’t just a technical requirement, it’s the foundation of client trust and business continuity.
Regulatory compliance and legal obligations
You face strict obligations under frameworks like the Tax Practitioners Board (TPB) regulations and the upcoming AUSTRAC AML/CTF requirements. These rules mandate that you verify client identities before establishing business relationships, with specific documentation standards and record-keeping periods. Failing to meet these standards can result in fines up to $222,000 per breach, suspension of your licence, or criminal charges in severe cases. Your verification process must be auditable, consistent, and capable of demonstrating compliance during reviews.
Beyond penalties, regulators expect you to maintain ongoing vigilance throughout the client relationship. This means updating records when clients change details, monitoring for suspicious activity, and escalating concerns through proper channels. Manual processes make these obligations difficult to sustain at scale, particularly when client volumes increase or staff turnover disrupts institutional knowledge.
Regulatory frameworks hold businesses accountable for knowing their clients, making robust verification systems a legal necessity, not a technical preference.
Protection against fraud and financial crime
Identity verification stops fraudsters before they can exploit your services for money laundering or tax evasion schemes. When you accept clients without proper checks, you become a potential conduit for illegal activity, exposing your practice to both criminal investigation and civil liability. Criminals actively target professional services because they provide access to financial systems, trust accounts, and legitimate business structures that can obscure illicit funds.
Financial crime creates direct costs through regulatory fines, legal fees, and remediation expenses, but the indirect costs often prove more damaging. Your professional reputation takes years to build and moments to destroy, clients leave when they associate your practice with fraud scandals, and insurers may increase premiums or deny coverage altogether. Effective verification acts as a deterrent mechanism that signals to bad actors that your practice maintains high standards.
Operational efficiency and client trust
Automated verification integrated into your existing CRM eliminates manual document handling, reduces processing time from days to minutes, and removes the risk of human error in data entry. You free up staff to focus on advisory work rather than administrative checks, improving both productivity and job satisfaction. Clients experience faster onboarding with fewer follow-up requests for additional documentation.
When clients see that you take verification seriously, they recognise your commitment to security and professionalism. This builds confidence in your ability to protect their sensitive information and handle their affairs responsibly, strengthening long-term client relationships and increasing referral rates.
How identity verification works step by step
Understanding the identity verification definition requires seeing how the actual process unfolds in practice. Your verification workflow follows a systematic sequence that builds confidence with each stage, transforming raw client information into verified identity records that meet regulatory standards. Each step validates different aspects of identity, creating multiple layers of protection against fraud and impersonation.
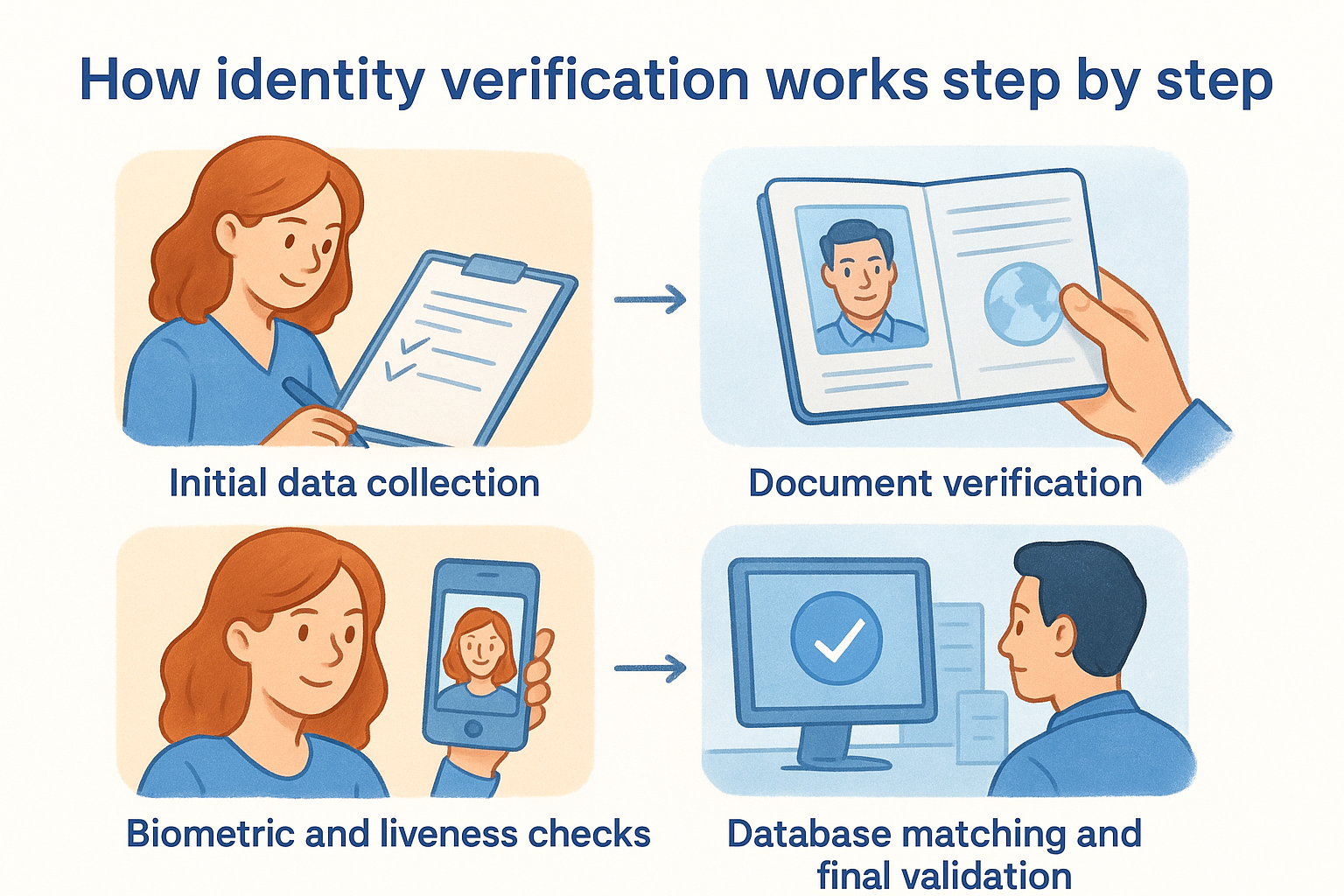
Initial data collection
You begin by gathering basic identifying information from your client, including their full name, date of birth, residential address, and contact details. This data forms the foundation for all subsequent checks and typically comes through your onboarding forms or CRM intake process. The information must match what appears on official documents, so accuracy at this stage prevents delays later.
Document verification
Your system examines government-issued identity documents like passports, driver’s licences, or national ID cards to confirm their authenticity and validity. Modern verification tools check for security features such as holograms, watermarks, and microprinting while comparing document formats against databases of known genuine documents. The system extracts data from these documents and cross-references it against the information your client provided in the initial stage.
Document verification acts as a critical checkpoint that catches forged or expired credentials before they enter your client records.
Biometric and liveness checks
Biometric verification compares a live selfie or video capture from your client against the photo on their identity document. Liveness detection ensures the person isn’t using a static photo or deepfake video to circumvent the check. This step confirms that the individual presenting the document is its rightful owner.
Database matching and final validation
Your verification system queries government databases and third-party records to confirm the client’s identity information matches official sources. This final validation creates an auditable record showing when, how, and by whom the verification occurred, meeting your compliance obligations under TPB and AUSTRAC frameworks.
Common identity verification methods and checks
When you implement verification, you’ll encounter several distinct approaches that work together to establish identity confidence. Each method serves specific purposes within your overall compliance framework, and understanding when to apply them helps you build a proportionate response to different client risk profiles. The methods you choose depend on your regulatory obligations, the sensitivity of your services, and the level of assurance you need before onboarding a client.
Document-based verification
You verify identity by examining government-issued credentials like passports, driver’s licences, Medicare cards, or proof-of-age cards. Your verification system extracts information from these documents and checks for security features such as holograms, UV markings, and microprinting that indicate authenticity. This method works well for remote onboarding because clients can photograph their documents using a smartphone, eliminating the need for in-person meetings.
Biometric verification
Biometric checks compare physical characteristics like facial features, fingerprints, or voice patterns against reference data stored on identity documents or in government databases. You typically use facial recognition combined with liveness detection to confirm the person presenting credentials is their legitimate owner. This method prevents someone from using stolen or borrowed documents to impersonate another individual.
Combining biometric checks with document verification creates a layered defence that addresses both credential fraud and identity theft simultaneously.
Database and knowledge-based checks
Your system queries authoritative databases like electoral rolls, credit bureaus, or government records to confirm the client’s information matches official sources. Knowledge-based authentication asks clients to answer questions derived from their personal history, such as previous addresses or financial transactions, that only the genuine individual would know. These checks validate that the person exists in legitimate systems and possesses detailed knowledge about their own identity history.
Identity verification vs authentication and KYC
You’ll often encounter these terms used interchangeably, but they describe distinct processes that serve different purposes in your security and compliance framework. Understanding where the identity verification definition sits alongside authentication and Know Your Customer (KYC) procedures helps you build accurate workflows that address the right risks at appropriate stages of your client relationship. Each process answers a different question about your client’s identity and access rights.
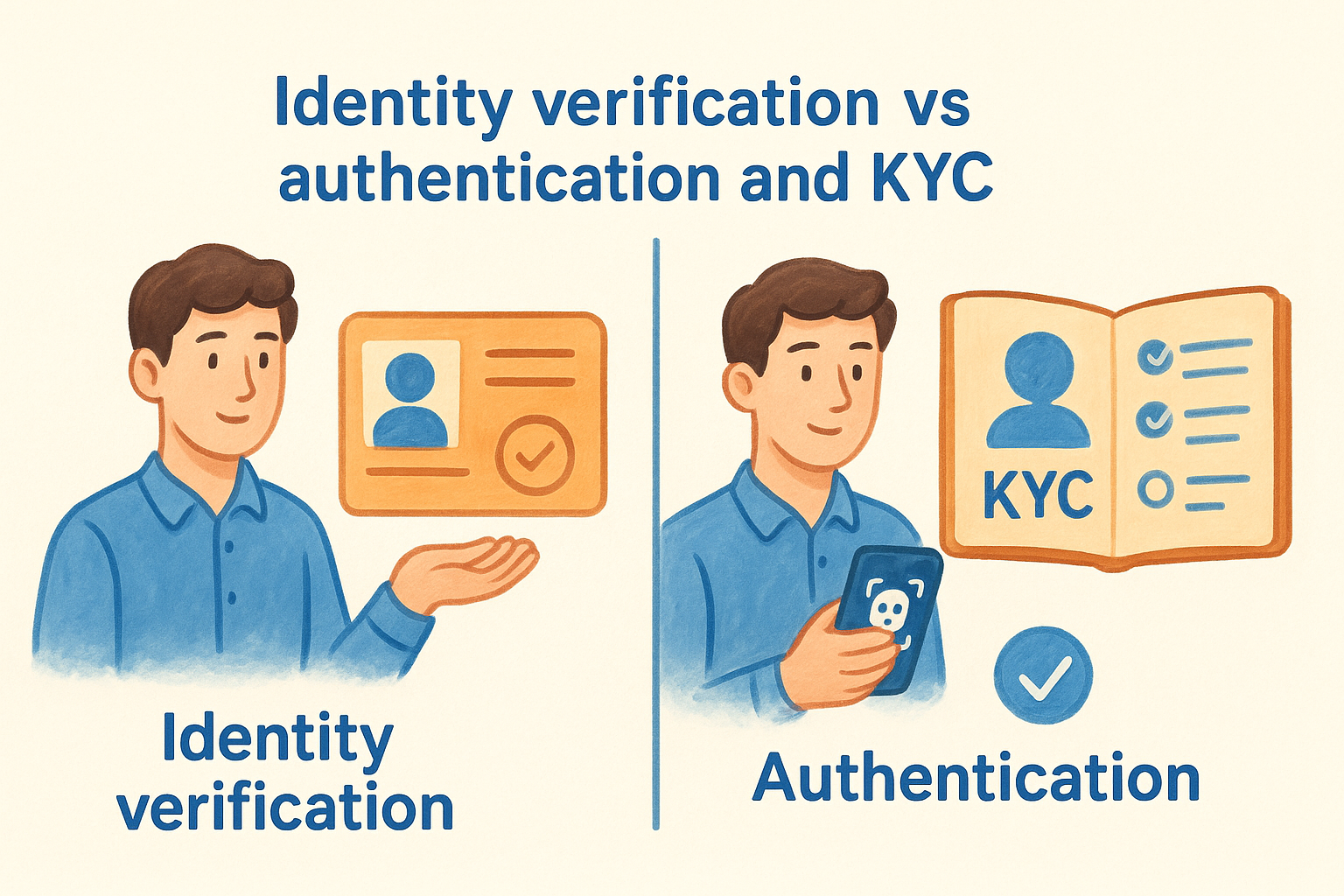
Identity verification vs authentication
Identity verification establishes who someone is when they first interact with your business, while authentication confirms they remain that same person during subsequent interactions. You verify identity once during onboarding by checking documents and biometric data, creating a baseline record of the client’s true identity. Authentication happens repeatedly throughout the relationship when clients log into your portal or request services, using passwords, biometric scans, or multi-factor authentication to prove they’re the authorised account holder.
Verification answers "who are you?" at the start of a relationship, while authentication answers "are you still you?" every time someone accesses your systems.
Identity verification vs KYC
Know Your Customer (KYC) represents the broader compliance framework that includes identity verification as its foundational component. Your KYC procedures encompass identity verification plus additional checks like source of funds, beneficial ownership determination, ongoing transaction monitoring, and risk assessment. You might verify a client’s identity successfully but still fail KYC requirements if you can’t establish where their assets originated or identify ultimate beneficial owners in complex corporate structures. Identity verification provides the starting point for KYC, but meeting your full regulatory obligations under AUSTRAC AML/CTF requires the complete KYC process.
How to implement identity verification in your workflow
You can’t bolt identity verification onto your practice without considering how it fits your existing systems and compliance obligations. Implementation success depends on choosing tools that work with your current technology rather than forcing staff to adopt standalone platforms. For accounting firms using CRMs like HubSpot or Salesforce, native integrations eliminate the manual data transfer that creates errors and delays.
Choose an integration approach
Your verification system should read client information directly from your CRM, perform checks, and write results back without requiring staff to switch between applications. StackGo’s IdentityCheck exemplifies this native integration model, operating entirely within your existing software environment. This approach reduces training time, prevents data entry mistakes, and ensures verification happens at the right stage in your onboarding workflow.
Integration within your existing systems removes friction from compliance tasks, making verification a natural part of your client intake process rather than an additional burden.
Map your verification requirements
You need to determine which clients require standard checks versus enhanced due diligence based on risk assessment criteria and regulatory thresholds. Consider factors like transaction values, jurisdiction complexity, and beneficial ownership structures when defining verification levels. Document these requirements clearly so staff apply consistent standards across all client relationships, meeting your obligations under TPB and AUSTRAC frameworks.
Test and deploy within your CRM
Run verification processes on test records before activating them in production to confirm data flows correctly through each stage. Monitor the first 20-30 real verifications closely, checking that results populate the correct CRM fields and trigger appropriate follow-up actions. Adjust field mappings or workflow rules as needed based on initial results, then scale the process across your entire client intake operation.
Key takeaways
The identity verification definition extends beyond simple document checks to encompass a complete compliance framework that protects your practice from fraud, regulatory penalties, and operational inefficiencies. You need verification systems that integrate directly into your existing CRM rather than forcing staff to adopt separate platforms that create data entry errors and workflow disruptions.
Australian accounting firms face mounting pressure under TPB regulations and the upcoming AUSTRAC AML/CTF requirements, making automated verification essential for sustainable compliance at scale. StackGo’s IdentityCheck handles these obligations within your current software environment, eliminating manual processes while maintaining the audit trails regulators demand during reviews. Your verification workflow should operate where your client data already lives, reducing training time and ensuring consistent application of compliance standards across all client relationships. See how IdentityCheck handles AUSTRAC Tranche 2 compliance inside your existing systems, or create a free account to test the solution for your practice.









