Every time a client hands over their passport scan, driver’s licence, or financial details for identity verification, they’re trusting your business with something irreplaceable. The importance of data encryption sits at the centre of that trust, it’s the mechanism that turns readable sensitive information into unreadable code, keeping it safe from unauthorised access during storage and transit.
For regulated businesses running KYC/AML checks and client onboarding, encryption isn’t optional, it’s foundational. Compliance frameworks like AUSTRAC’s AML/CTF obligations expect businesses to protect personally identifiable information (PII) at every stage. A single breach doesn’t just cost money; it costs client confidence and can trigger serious regulatory consequences.
This is exactly why we built StackGo’s Privacy Layer, to ensure PII from identity checks never sits exposed in your CRM, and remains accessible only through MFA-authenticated admin controls. Encryption underpins how that protection works.
This article breaks down what data encryption actually does, why it matters for security and compliance, and how it protects the sensitive information your business handles every day. Whether you’re an accounting firm, financial services provider, or any regulated professional, this one’s worth understanding properly.
How data encryption works
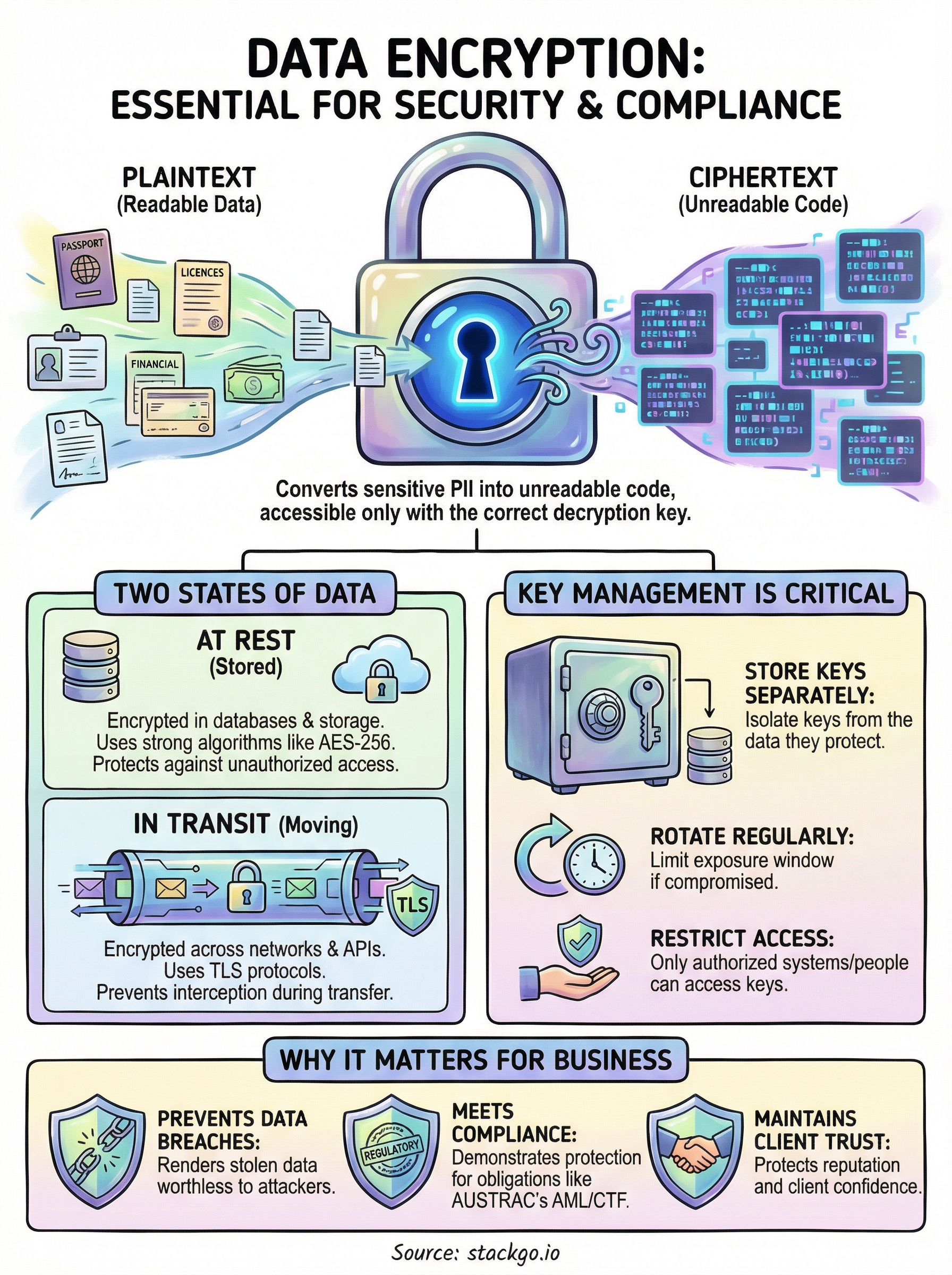
At its core, encryption takes plaintext (readable data) and runs it through a mathematical algorithm that scrambles it into ciphertext (unreadable data). Only someone with the correct decryption key can reverse the process. Think of it like a combination lock: the data is locked inside, and only the right combination opens it. Without the key, the scrambled output is useless to anyone who intercepts it.
Encryption algorithms and keys
The algorithm defines the rules for scrambling, and the encryption key is the unique value that controls the output. Modern encryption standards like AES-256 (Advanced Encryption Standard) use keys that are 256 bits long, producing combinations so vast that a brute-force attack would take longer than the age of the universe to crack. When you’re handling identity documents, financial records, or KYC data, the strength of the algorithm directly determines how well that data is protected.
Understanding the importance of data encryption starts here: weak or outdated algorithms leave sensitive data exposed regardless of your other security controls. For regulated businesses in Australia, that exposure can mean AUSTRAC penalties, data breach notification obligations, and lasting damage to client trust.
The strength of your encryption is only as good as the algorithm and key length you choose; modern standards are the baseline, not the ceiling.
Symmetric vs asymmetric encryption
There are two main encryption types your business will encounter. Symmetric encryption uses a single key for both encrypting and decrypting data, making it fast and efficient for large volumes stored at rest. Asymmetric encryption uses a key pair: a public key to encrypt and a private key to decrypt, which is what secures data moving across networks.
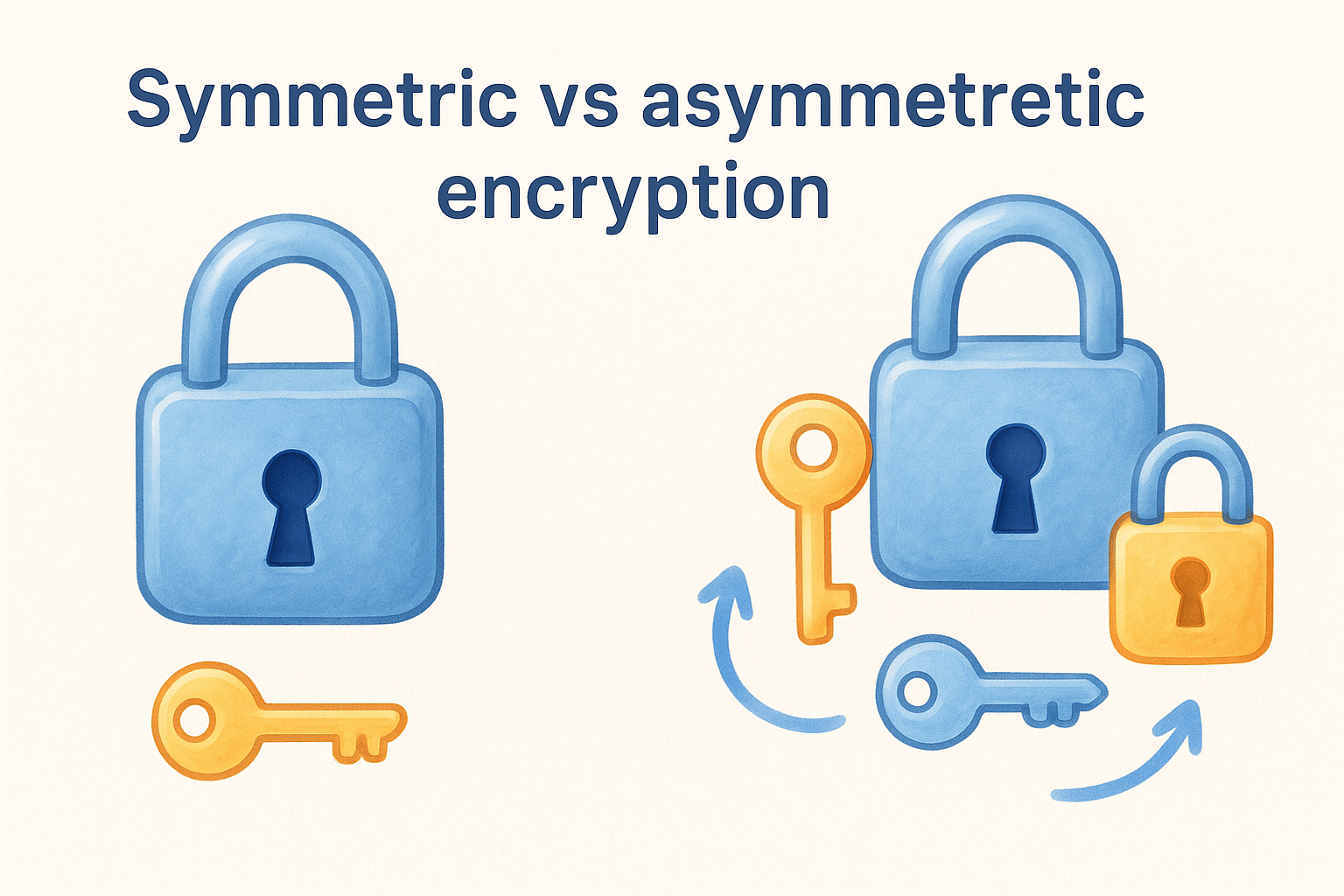
Most regulated businesses rely on both types working together. TLS (Transport Layer Security), for example, uses asymmetric encryption to establish a secure connection, then switches to symmetric encryption for the actual data transfer. Knowing how these mechanisms interact helps you ask the right questions when evaluating any identity verification or compliance platform.
Why data encryption matters for security and privacy
Data breaches happen to businesses of every size, and regulated industries face the sharpest consequences. When client PII like passport scans, tax file numbers, or financial records falls into the wrong hands, the damage goes well beyond the immediate incident. You face regulatory penalties, mandatory breach notifications, and clients who no longer trust you with their sensitive information.
Encryption doesn’t prevent every attack, but it renders stolen data worthless to whoever takes it.
Protecting sensitive client data
The practical importance of data encryption becomes clear when you consider what attackers actually want: usable data. Encrypted records offer nothing without the decryption key, so even a successful breach returns unreadable noise rather than actionable client details.
For businesses running KYC or AML checks, this protection matters most because identity documents, tax file numbers, and financial records are exactly what identity thieves target. Encryption turns your most sensitive data into a dead end for anyone who accesses it without authorisation.
Meeting compliance obligations
Australian businesses under AUSTRAC’s AML/CTF framework or the Privacy Act 1988 carry a legal duty to protect client information at every stage of its lifecycle. Regulators expect you to store and transmit data securely, not just collect it carefully. Encryption gives you a clear, demonstrable control that proves your compliance posture is active and proportionate. That matters when regulators audit your practices or when a breach triggers a formal investigation. The obligations encryption helps you meet include:
- Protecting PII from unauthorised access during storage and transfer
- Demonstrating proportionate technical controls under the Privacy Act 1988
- Supporting AML/CTF compliance obligations for client data security
Encryption at rest vs encryption in transit
Understanding where your data sits at any given moment shapes the encryption controls you need. Data exists in two states: at rest (stored in databases, file systems, or cloud storage) and in transit (moving across networks, APIs, or between services). Each state carries different risks, and the importance of data encryption requires you to address both, not just one or the other.
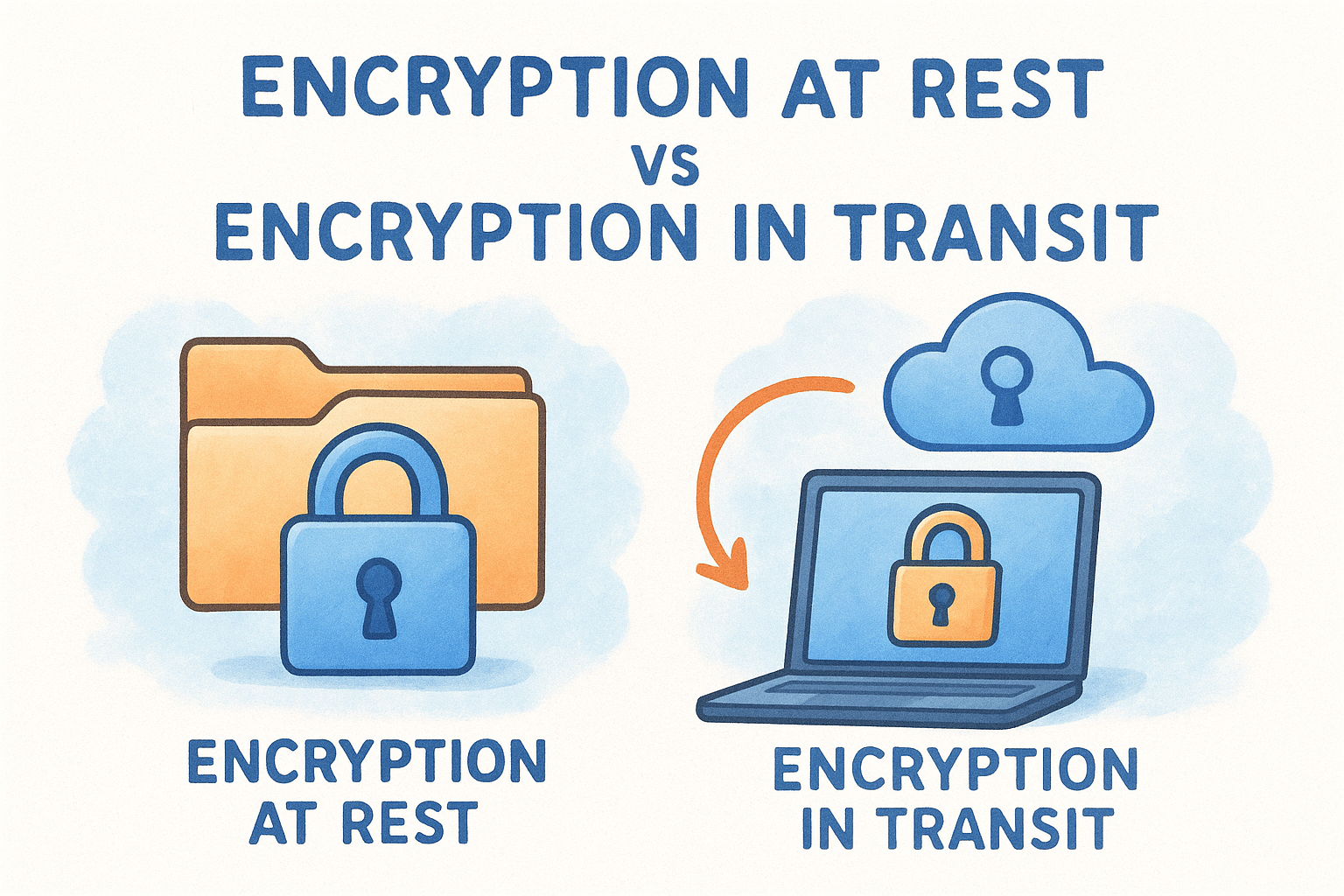
Encryption at rest
Data at rest covers everything you store: client identity documents, KYC records, financial information, and audit logs. When this data sits unencrypted, anyone with access to your storage system, whether through a breach, misconfiguration, or an insider threat, can read it directly. AES-256 is the standard for encrypting stored data and is what reputable compliance platforms apply to any PII they hold on your behalf.
Encrypting stored data means a compromised database returns nothing useful to an attacker without the corresponding decryption key.
Encryption in transit
Every piece of data in transit is vulnerable the moment it leaves one system and travels to another. TLS (Transport Layer Security) protects this movement by encrypting the connection between your browser, your platform, and any third-party identity verification service. Without it, data crossing a network is readable to anyone positioned along that path.
For businesses running identity checks through integrated platforms, you need confirmation that every API call and data transfer uses TLS 1.2 or higher. Anything less leaves your client data exposed during the most active stage of the verification process.
Key management and common encryption pitfalls
Encryption only protects your data when the keys that control it are properly managed. You can apply industry-standard algorithms across every system and still face a breach if keys are stored next to the data they encrypt, never rotated, or accessible to too many people. The importance of data encryption hinges as much on key discipline as it does on algorithm strength.
Storing keys separately from data
When encryption keys sit alongside the data they protect, they defeat the entire purpose of encryption. Attackers who access your database should find keys stored nowhere near it. Dedicated key management services from major cloud providers isolate keys behind their own access controls, keeping them auditable and separate from anything they secure.
Good key storage practice includes:
- Isolating keys in a dedicated KMS, not in application config files
- Restricting key access by role, not by convenience
- Logging every key access event for audit purposes
Treating key storage as an afterthought is the fastest way to render strong encryption worthless.
Rotation, access control, and outdated algorithms
Rotating encryption keys on a defined schedule limits the exposure window if a key is ever compromised. Alongside rotation, you need to restrict key access strictly to the systems and people that genuinely require it, not the entire organisation by default.
Retiring outdated algorithms like MD5 or SHA-1 matters equally. These standards no longer satisfy modern security requirements, and relying on them leaves your data vulnerable regardless of how carefully you manage the keys themselves.
How to apply encryption in real businesses
Knowing the importance of data encryption is one thing; applying it across your actual operations is another. Most regulated businesses don’t build encryption from scratch; they choose platforms and infrastructure that implement it correctly by default, then verify those implementations are active and current.
The fastest way to apply strong encryption is to select compliant vendors and confirm their standards in writing before you share a single piece of client data.
Start with a data inventory
Before you configure anything, map where your sensitive data actually lives. Identity documents, KYC records, and financial details often sit across multiple systems: your CRM, a document storage service, a verification platform. You cannot encrypt what you haven’t located. For each data store, confirm whether encryption at rest using AES-256 is enabled and whether TLS protects every connection that touches it.
Choose platforms built with encryption by design
When you run identity checks through an integrated compliance platform, the encryption controls are already built into the product, not bolted on later. Platforms like StackGo’s IdentityCheck read contact data from your CRM, verify it, and write back only the outcome, meaning raw PII never sits exposed inside your systems. Look for vendors who can confirm their encryption standards in their security documentation and who apply MFA-controlled access for any admin who can reach sensitive records.
Applying encryption in practice means selecting the right tools, confirming their security standards upfront, and building a clear record of those controls for compliance and audit purposes.
Final takeaways
The importance of data encryption comes down to a straightforward reality: sensitive client data is a target, and encryption is what makes that target useless to anyone who reaches it without authorisation. Applying AES-256 for stored records and TLS for data in transit, managing your keys properly, and choosing platforms that build encryption in by default covers the core of what regulated businesses need to get right.
Accounting firms, financial services providers, and any business running KYC or AML checks carry a legal and ethical duty to protect client PII at every stage. Encryption is the control that proves your obligations are being met, not just acknowledged.
If your business runs identity verification checks and you want to confirm your compliance controls are solid, explore how IdentityCheck handles AUSTRAC Tranche 2 AML/CTF obligations to see how encryption and privacy protection work inside your existing systems.









