Australian reporting entities face increasing pressure to demonstrate robust AML risk assessment methodology as part of their compliance obligations. Whether you’re preparing for AUSTRAC’s expanded AML/CTF regime or strengthening your existing framework, understanding how to properly assess money laundering and terrorism financing risks is no longer optional, it’s foundational to your compliance program.
A well-structured risk assessment does more than tick a regulatory box. It shapes your entire approach to customer due diligence, transaction monitoring, and ongoing compliance activities. Get it right, and you’ll allocate resources effectively while meeting your legal obligations. Get it wrong, and you’re exposed to regulatory penalties, reputational damage, and potential criminal liability.
This guide breaks down the complete risk assessment process into actionable steps. You’ll learn how to identify inherent risks, evaluate your control environment, and document your findings in a way that satisfies regulators. At StackGo, we help regulated businesses streamline their identity verification and KYC processes through integrated compliance tools, but effective verification starts with understanding your risk profile. Let’s walk through exactly how to build that foundation.
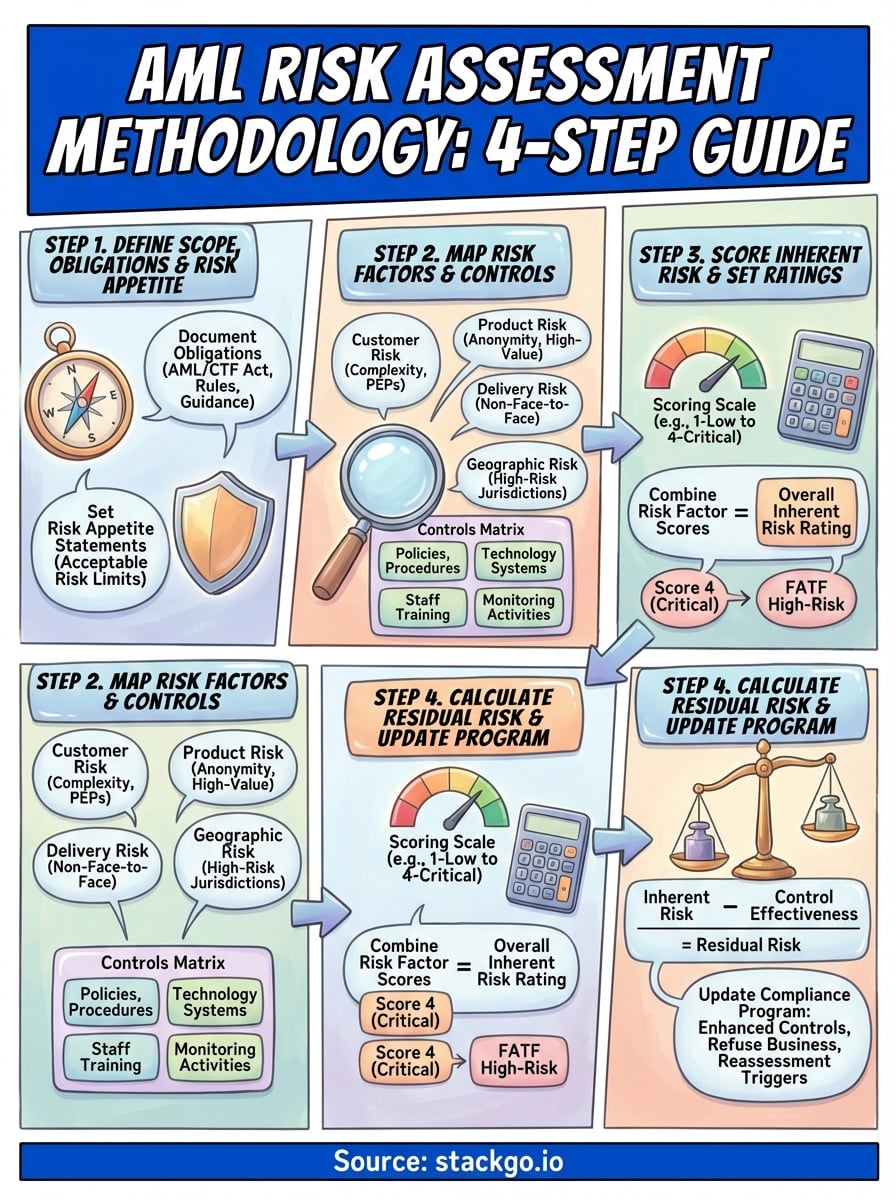
What an AML risk assessment methodology covers
Your AML risk assessment methodology forms the blueprint for how you identify, evaluate, and manage money laundering and terrorism financing risks across your business. This isn’t a static document you file away after completion. It’s a living framework that dictates which customers require enhanced due diligence, what transaction patterns trigger alerts, and where you allocate compliance resources. Australian reporting entities must demonstrate this methodology meets AUSTRAC’s expectations while reflecting the specific risks your business faces.
Core components of your risk assessment
The methodology itself consists of several interconnected elements that work together to produce a complete risk picture. You’ll document how you classify customers based on risk factors, how you weight different risk categories, and what thresholds trigger escalation. Your methodology also covers the frequency of assessments, both for initial onboarding and ongoing reviews. This includes defining when you’ll conduct simplified due diligence versus enhanced due diligence, and what specific information you’ll collect at each level.
A documented methodology shows regulators you’re taking a systematic, repeatable approach rather than making ad hoc decisions about customer risk.
Your methodology must also address how you’ll maintain and update risk ratings as circumstances change. This means establishing triggers for reassessment, such as significant transaction pattern changes, adverse media hits, or shifts in a customer’s business activities. You’re building an operational playbook that staff can follow consistently, regardless of who’s conducting the assessment.
Risk factors you must evaluate
Every AML risk assessment methodology requires you to examine four fundamental risk categories: customer risk, product or service risk, delivery channel risk, and geographic risk. Within each category, you’ll identify specific factors that increase or decrease your exposure to money laundering and terrorism financing threats.

Customer risk factors include the nature of the customer’s business, ownership structure, source of wealth, and whether they’re a politically exposed person. Product risk covers the services you offer, such as high-value transactions, international transfers, or bearer instruments. Delivery channel risk examines whether you conduct face-to-face verification or rely on non-face-to-face methods. Geographic risk assesses whether customers operate in or transact with high-risk jurisdictions identified by FATF or Australian authorities.
Your methodology defines how you’ll collect information about each risk factor, where that data comes from, and how you’ll weight different factors in your overall risk calculation. You’re not just listing risks, you’re creating a scoring system that produces consistent, defensible outcomes.
Step 1. Define scope, obligations, and risk appetite
Your first task in building an AML risk assessment methodology is establishing exactly what you’re assessing and why. This means documenting which parts of your business fall under AML/CTF obligations, what your specific regulatory requirements are, and how much risk you’re willing to accept. You can’t evaluate risks effectively without these boundaries in place. Australian reporting entities must start here because your scope determines everything from which customers require assessment to what data you need to collect.
Document your regulatory obligations
Begin by identifying every regulatory obligation that applies to your business operations. Review the AML/CTF Act 2006, the AML/CTF Rules, and any AUSTRAC guidance relevant to your sector. Create a simple table listing each obligation, the specific rule reference, and what it requires you to do. For example, if you’re required to conduct enhanced customer due diligence for politically exposed persons under Rule 4.3.3, document that specifically.
Your methodology can’t demonstrate compliance if you haven’t first documented what you’re complying with.
Next, identify which business activities, customer types, and transaction types trigger reporting obligations. This shapes your assessment scope. If you offer both domestic and international wire transfers, your scope includes both services but with different risk weightings. Don’t assume all business units carry equal AML obligations.
Set clear risk appetite statements
Your risk appetite defines the maximum level of risk you’ll accept before refusing a customer relationship or implementing additional controls. Write specific statements for each risk category. For example: "We will not onboard customers from FATF high-risk jurisdictions without board approval and ongoing enhanced monitoring." This isn’t about taking zero risk, it’s about knowing your limits and documenting them clearly for staff and regulators alike.
Step 2. Map your risk factors and controls
Once you’ve defined your scope, you need to create a comprehensive inventory of every risk factor your business faces and every control measure you’ve implemented. This mapping exercise forms the backbone of your AML risk assessment methodology. You’re building a matrix that shows exactly where risks exist in your operations and what you’re doing to mitigate them. Australian reporting entities must demonstrate they’ve considered all relevant risk categories systematically, not just the obvious ones.
Identify and categorise your risk factors
Start by listing every risk factor within the four mandatory categories: customer, product, delivery channel, and geographic. Under customer risk, document factors like business complexity, beneficial ownership structures, cash-intensive industries, and PEP status. For product risk, list each service you offer and note characteristics that create ML/TF exposure, such as anonymity potential, transaction speed, or cross-border capabilities.
Create a table that captures each risk factor with its category, description, and where it appears in your business. Here’s a practical structure:
| Risk Category | Risk Factor | Business Area | Potential ML/TF Threat |
|---|---|---|---|
| Customer | Complex ownership structures | Corporate accounts | Beneficial owner concealment |
| Product | International wire transfers | All branches | Cross-border layering |
| Delivery | Non-face-to-face onboarding | Digital channel | Identity fraud |
| Geographic | Transactions with high-risk jurisdictions | Wire transfer service | Sanctions evasion |
Your risk map isn’t complete until you’ve documented every point where money or information enters, moves through, or exits your business.
Document existing controls against each risk
Now list every control measure you’ve implemented to address each risk factor. Controls include policies, procedures, technology systems, staff training, and monitoring activities. Map each control directly to the risks it’s designed to mitigate. For example, if you’ve identified non-face-to-face onboarding as a delivery channel risk, your controls might include biometric verification, document authentication technology, and enhanced monitoring for the first 90 days of the relationship.
Step 3. Score inherent risk and set ratings
Now that you’ve mapped your risk factors and controls, you need to assign numerical values to each risk and calculate an overall inherent risk rating. Inherent risk represents the level of ML/TF exposure your business would face without any controls in place. This scoring step transforms your qualitative risk observations into quantifiable measures that you can track, compare, and report to regulators. Your AML risk assessment methodology requires a consistent scoring framework that produces defensible outcomes every time you assess a customer or transaction type.

Assign numerical scores to each risk factor
Create a scoring scale for each risk category that reflects the severity of ML/TF exposure. Most reporting entities use a 1-4 or 1-5 scale where higher numbers indicate greater risk. For each risk factor you’ve identified, assign a score based on documented criteria. For example, customers from FATF high-risk jurisdictions might score 4, while customers from low-risk jurisdictions score 1. Transaction types that allow anonymity score higher than transparent payment methods.
Document your scoring criteria in a reference table that staff can apply consistently:
| Risk Factor | Score 1 (Low) | Score 2 (Medium) | Score 3 (High) | Score 4 (Critical) |
|---|---|---|---|---|
| Geographic | Australia, NZ | EU countries | Non-FATF members | FATF high-risk jurisdictions |
| Customer type | Individual, verified income | Small business | Complex structure | Cash-intensive business |
| Transaction value | Under $5,000 | $5,000-$50,000 | $50,000-$500,000 | Over $500,000 |
Calculate your inherent risk rating
Combine individual risk factor scores to produce an overall inherent risk rating for each customer or business relationship. The simplest method multiplies or adds scores across categories, then applies thresholds to assign Low, Medium, High, or Critical ratings. For example, if customer risk scores 3, product risk scores 2, delivery channel scores 1, and geographic risk scores 4, your total might be 10, which maps to a High inherent risk rating.
Your scoring system must be reproducible, meaning different staff members should reach the same inherent risk conclusion when assessing identical circumstances.
Step 4. Calculate residual risk and update your program
After scoring inherent risk, you apply your control measures to calculate residual risk, which represents the ML/TF exposure that remains after all your safeguards are in place. This step determines whether your current controls adequately reduce risk to an acceptable level or whether you need stronger measures. Your AML risk assessment methodology must demonstrate that residual risk falls within your documented risk appetite. If it doesn’t, you’re required to implement additional controls or decline the business relationship entirely.
Apply controls to reduce inherent risk
Review each control measure you mapped in Step 2 and assign an effectiveness rating to show how well it mitigates the corresponding inherent risk. Use a consistent scale such as 1-4, where 4 represents highly effective controls and 1 indicates weak or unreliable controls. For example, automated transaction monitoring systems with proven detection rates might score 4, while manual quarterly reviews might score 2. Calculate residual risk by subtracting your control effectiveness from your inherent risk score.
Here’s a practical calculation example:
| Risk Category | Inherent Risk Score | Control Effectiveness | Residual Risk |
|---|---|---|---|
| Customer | 4 | 3 | 1 (Low) |
| Product | 3 | 2 | 1 (Low) |
| Geographic | 4 | 3 | 1 (Low) |
| Delivery | 2 | 3 | 0 (Minimal) |
If your residual risk exceeds your risk appetite, you must either strengthen controls or refuse the business relationship.
Update your compliance program based on findings
Your assessment findings drive specific changes to your compliance program. Where residual risk remains high, document exactly what additional controls you’ll implement, who’s responsible, and by what date. This might include enhanced monitoring frequencies, additional verification requirements, or senior management approval for ongoing relationships. Update your policies, procedures, and staff training materials to reflect these changes. Schedule your next assessment date based on the residual risk rating, with higher-risk relationships requiring more frequent reassessment.
Next steps for a defensible risk assessment
Your AML risk assessment methodology needs to move from documentation into operational practice. Start by training every staff member who conducts customer assessments on your scoring system and escalation procedures. Create a review calendar that schedules reassessments based on residual risk ratings, with high-risk customers reviewed at least quarterly. Assign clear ownership for each component of your methodology, from data collection to final approval.
Test your methodology with real customer scenarios before full implementation. Run your scoring system against existing customer relationships to verify it produces sensible outcomes. Adjust weighting factors if you spot obvious misalignments between calculated risk and actual ML/TF exposure. Build audit trails that capture who assessed each customer, when, and what information they used.
Australian reporting entities face stricter verification requirements under AUSTRAC’s Tranche 2 reforms. Your risk assessment determines which customers need enhanced due diligence, making accurate verification crucial. Document every assessment decision, maintain version control on your methodology, and prepare to demonstrate your framework to regulators when required.









