People often use "privacy" and "protection" interchangeably when talking about data. On the surface, that seems harmless, but the distinction between data privacy vs data protection actually matters, especially if your business handles client information for compliance purposes. Getting the two confused can lead to gaps in your processes that regulators won’t overlook.
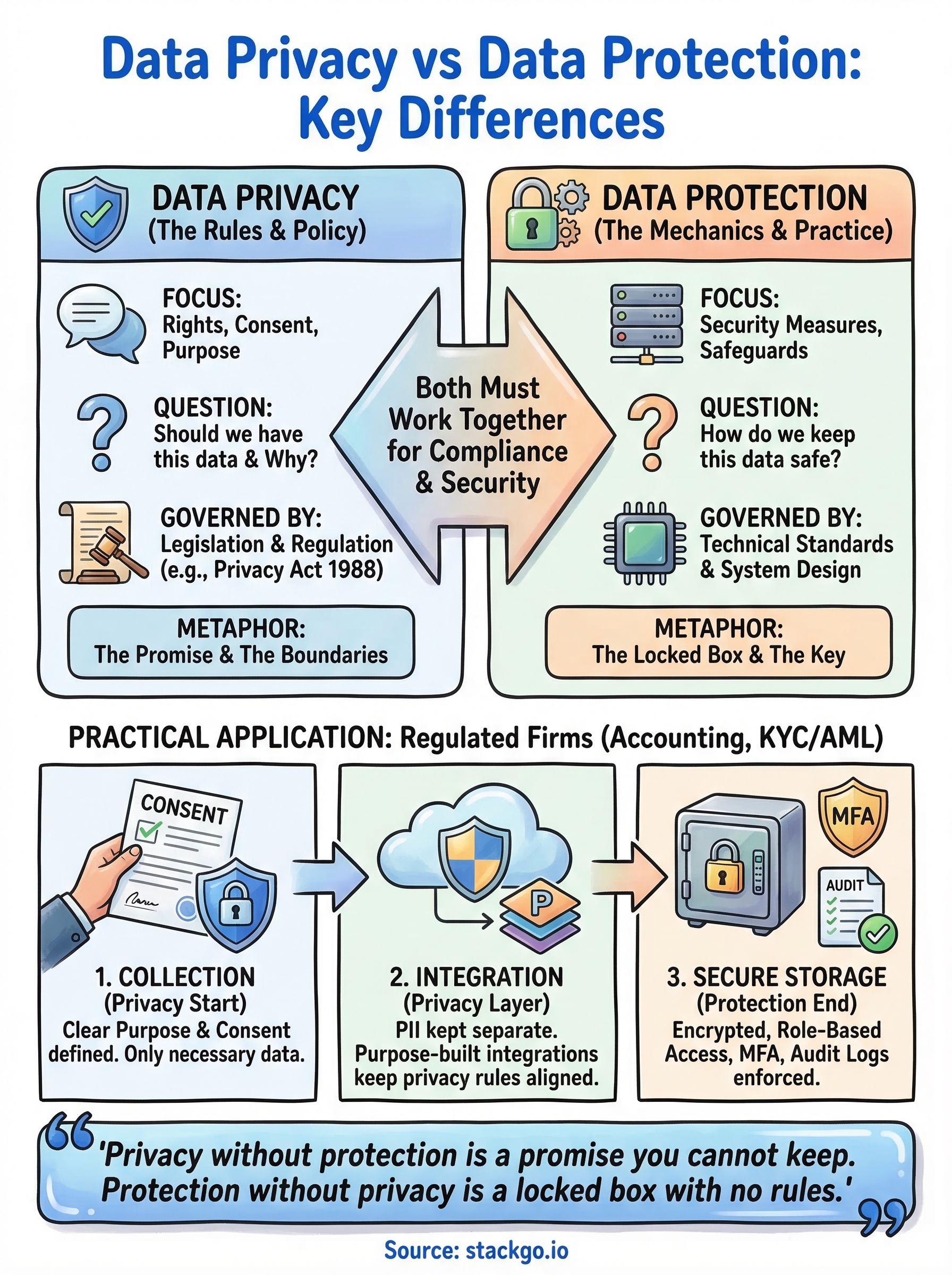
Data privacy is about the rules: who can access personal information, what they’re allowed to do with it, and why they have it in the first place. Data protection is about the mechanics: encryption, access controls, and safeguards that stop unauthorised parties from getting to that information. One defines the boundaries; the other enforces them. You need both working together, not just one.
For regulated businesses, accountants, financial services, legal firms, this isn’t an academic exercise. If you’re running identity verification or KYC/AML checks, you’re collecting sensitive personal data every day. At StackGo, we built our integration platform (including IdentityCheck) with a Privacy Layer specifically designed to keep personally identifiable information out of your CRM, accessible only to MFA-authenticated admins. It’s one practical example of privacy and protection principles working side by side.
This article breaks down the key differences between data privacy and data protection, explains where each one applies, and helps you understand how they work together to keep your business compliant and your clients’ data secure.
Data privacy vs data protection at a glance
The simplest way to separate these two concepts is to think of privacy as the policy and protection as the practice. Privacy sets the rules around what data you can collect, why you collect it, and who is allowed to use it. Protection handles the mechanisms that keep that data safe once you have it. Both are necessary, but they operate at different levels of your compliance framework.
Privacy without protection is a promise you cannot keep. Protection without privacy is a locked box with no rules about who holds the key.
What data privacy covers
Data privacy focuses on the rights of the individual and the obligations your business takes on when you collect personal information. It answers the core question: should you have this data, and what are you permitted to do with it? In Australia, this falls under frameworks like the Privacy Act 1988, which sets out how personal information must be handled, used, and disclosed.
At a practical level, privacy governs:
- Consent: whether your client has agreed to you collecting their information
- Purpose: what you told them you would use it for
- Retention: how long you are allowed to keep it
- Disclosure: who else you can share it with
What data protection covers
Protection is the technical and organisational side of the equation. It covers the specific measures you put in place to stop unauthorised access, accidental loss, or misuse of the personal data you already hold. Think encryption, multi-factor authentication, access controls, and audit logs. These are the tools that make your privacy commitments enforceable in practice.
Your protection measures need to match the sensitivity of the data you hold. An accounting firm collecting client tax file numbers and identity documents carries a higher risk exposure than a business holding only email addresses, which means stronger controls and tighter access restrictions are necessary.
How they compare side by side
Seeing data privacy vs data protection in one place makes the distinction easier to apply in your own business.
| Data Privacy | Data Protection | |
|---|---|---|
| Focus | Rights, consent, and purpose | Security measures and safeguards |
| Key question | Should we have this data, and why? | How do we keep this data safe? |
| Governed by | Legislation and regulation | Technical standards and system design |
| Who owns it | Legal, compliance, management | IT, operations, software vendors |
Neither one works without the other. Strong privacy rules mean nothing if your systems get breached, and robust technical controls cannot help you if you were never authorised to collect the data in the first place.
Data privacy: who can use data and why
Data privacy defines the boundaries around personal information before you ever collect it. It answers the foundational questions: are you allowed to have this data, what did you tell the person you would use it for, and who inside or outside your business can access it? When you look at data privacy vs data protection, privacy is always the starting point because it shapes every decision that follows.
The legal foundation in Australia
In Australia, the Privacy Act 1988 is the primary legislation governing how businesses handle personal information. It applies to most private sector organisations with an annual turnover above $3 million, as well as health service providers and certain others regardless of size. Accounting firms managing client tax records, legal practices holding sensitive financial data, and financial services businesses running KYC/AML checks all fall squarely within its scope.
The Act sets out 13 Australian Privacy Principles (APPs) that cover the full lifecycle of personal data. The key principles your business needs to understand are:
- Collection: only collect information that is reasonably necessary
- Notification: tell individuals why you are collecting it at the time of collection
- Use and disclosure: only use data for the purpose you originally stated
- Data quality: keep the information accurate and up to date
- Access and correction: give individuals the right to access and correct their own data
Why purpose matters more than you think
Collecting data without a clearly defined purpose is the fastest way to breach privacy obligations, even if your security controls are perfect.
Purpose limitation is the principle that ties privacy to accountability. If you collect a client’s identity documents for AML verification, you cannot then use that data for marketing without separate, explicit consent. Regulators look at what you collected, what you said you would do with it, and whether your actions matched that statement.
Data protection: how you keep data safe
Where data privacy vs data protection differs most clearly is at the implementation level. Privacy defines what you are permitted to do with data; protection determines whether you can actually stop others from accessing what they should not. Data protection is the set of technical and organisational controls you build to prevent unauthorised access, accidental loss, or deliberate misuse of personal information you hold.

Weak protection controls are not a minor oversight. They create direct liability under Australian privacy law if a breach causes serious harm to individuals.
Technical controls that matter
The technical side covers the tools and systems that restrict how data is accessed and transmitted. Encryption ensures that even if someone intercepts data in transit, they cannot read it. Multi-factor authentication (MFA) stops unauthorised users from accessing accounts even with a stolen password, and role-based access controls limit which staff members can view specific data sets.
Your technical controls should cover:
- Encryption of data in transit and at rest
- MFA on all systems holding personal information
- Role-based access permissions
- Audit logs that record who accessed what and when
Organisational measures you cannot skip
Technical tools only work when policies and procedures support them. Staff training, clear data handling rules, and regular audits are organisational measures that sit alongside your technical setup. If your team does not know how to respond to a data breach, your encryption software cannot cover that gap.
Documented processes also protect you during regulatory reviews. Regulators want evidence that your controls are actively managed, not just installed and forgotten.
Common examples in regulated Australian firms
Regulated businesses in Australia deal with data privacy vs data protection challenges every day, not just when a regulator comes knocking. The examples below show how these two concepts play out in real workflows across the industries most exposed to compliance obligations.
Accounting firms running KYC/AML checks
An accounting firm onboarding a new client will typically collect identity documents, tax file numbers, and proof of address as part of their KYC obligations. Privacy rules determine what the firm is allowed to collect and require that clients are told exactly why that data is needed. Protection controls then determine how that information is stored and who inside the practice can access it.
Without both in place, a firm risks either collecting data it has no legal basis to hold, or exposing sensitive client records to staff who have no business seeing them.
A common gap is storing scanned identity documents directly inside a CRM where all users have visibility. That is a protection failure, but it often starts as a privacy misstep when no one defined access rules at the point of setup.
Legal practices and financial services firms
Legal practices face the same core tension. They hold highly sensitive financial and personal information across client matters, and that data often sits in case management systems that were never designed with granular access controls in mind. Financial services firms running AML checks on new clients add another layer: verification results and screening records must be retained for regulatory purposes, but access must stay tightly controlled.
Both industries benefit from integrations that write verification outcomes back into existing systems without storing raw PII where it does not belong, keeping privacy obligations and protection controls aligned from the start.
A practical checklist to align privacy and protection
Understanding data privacy vs data protection as separate concepts is useful, but the real work happens when you bring them together in practice. Many regulated firms in Australia treat them as separate workstreams owned by different teams, and that split creates gaps. Use the checklist below to evaluate whether your privacy and protection controls are actually aligned.
Privacy checks to complete before collecting data
Before you collect a single piece of personal information from a client, your legal and compliance obligations need to be clear. These questions help you confirm you have the right basis to collect and use the data you are about to gather.
- Have you defined the specific purpose for collecting each data type?
- Have you prepared a privacy notice that tells clients what you will collect and why?
- Do you have a process to record client consent where required?
- Have you confirmed data retention limits and built a schedule to delete records when those limits are reached?
Protection checks to complete once data is in your systems
Once data is in your systems, your technical and organisational controls need to match the sensitivity of what you hold. Run through these checks to confirm your protection measures are actually working.
- Are identity documents and PII stored separately from general CRM records, with restricted access?
- Do all systems holding personal data require MFA for login?
- Have you set role-based access controls so staff only see data relevant to their role?
- Do you maintain audit logs that record who accessed or modified personal records?
- Has your team completed data breach response training in the last 12 months?
Running these checks together, rather than in isolation, is what turns a compliance policy into a working compliance programme.
Key takeaways and what to do next
Data privacy vs data protection are not the same thing, and treating them as interchangeable leaves real gaps in your compliance framework. Privacy defines the rules around what you collect, why you collect it, and who can use it. Protection covers the technical and organisational controls that keep that data safe once it is in your systems. You need both, and they need to work together.
For regulated Australian businesses, particularly accounting firms and financial services practices, these obligations are growing. AUSTRAC’s Tranche 2 AML/CTF reforms are bringing more businesses into scope, which means your identity verification workflows need to meet both privacy and protection standards from the point of collection through to storage and deletion. Getting your processes right now is far easier than fixing them after a breach or regulatory review.
If you want to see how purpose-built integrations handle this in practice, explore how IdentityCheck supports AUSTRAC Tranche 2 compliance inside your existing software stack.









