If your business collects personal information from clients, and almost every business does, then the Australian Privacy Principles explained clearly should be high on your reading list. These 13 principles, set out under the Privacy Act 1988, govern how organisations handle personal data from the moment it’s collected to the moment it’s destroyed. Getting them wrong can mean regulatory action, reputational damage, and lost client trust.
For accounting firms, financial service providers, and other regulated businesses, these principles aren’t abstract legal theory. They directly shape how you onboard new clients, verify identities, store sensitive documents, and share information with third parties. Every KYC check, every AML screening, every piece of personally identifiable information (PII) sitting in your CRM, all of it falls under the APPs.
At StackGo, we build integration tools like IdentityCheck that help businesses run compliant identity verification directly from their existing software stack, with a dedicated privacy layer that keeps PII out of your CRM. Understanding the APPs is the foundation; having the right systems to uphold them is what follows. This guide breaks down all 13 Australian Privacy Principles, what each one requires, and what it means for your day-to-day operations.
What the Australian Privacy Principles are
The Australian Privacy Principles (APPs) are the legal foundation of privacy regulation in Australia, forming Schedule 1 of the Privacy Act 1988. They replaced the former National Privacy Principles and Information Privacy Principles in March 2014, following amendments introduced by the Privacy Amendment (Enhancing Privacy Protection) Act 2012. In plain terms, they set out the rules that APP entities must follow when they collect, hold, use, and disclose personal information about individuals. These are not voluntary guidelines. They carry the force of law, and non-compliance can trigger formal investigations, financial penalties, and orders to change how your business operates.
Where the APPs come from
The APPs were developed under the oversight of the Office of the Australian Information Commissioner (OAIC), the independent regulator responsible for enforcing privacy law across the country. The Privacy Act 1988 itself has roots in Australia’s commitments to international frameworks, including the OECD Guidelines on the Protection of Privacy and Transborder Flows of Personal Data, which laid the groundwork for modern privacy regulation across member nations. Recognising this international context helps you understand why the APPs follow a logical structure: they reflect globally recognised principles about how personal data should be treated, adapted for the Australian legal environment.
The OAIC continues to refine its guidance as technology, business models, and community expectations shift. Several significant reforms to the Privacy Act have been proposed and partially implemented in recent years, largely in response to major data breaches affecting millions of Australians. OAIC guidance documents are publicly available and regularly updated, which means this is not a static rulebook you read once. Keeping pace with those updates is part of your ongoing compliance responsibility.
What the 13 principles cover
To have the Australian privacy principles explained in a way that is actually useful, it helps to see the 13 APPs as a lifecycle framework. They follow personal information from the moment your organisation first considers collecting it, through how you store, use, and share it, to the point where you are required to destroy or de-identify it. They do not operate as isolated rules; each principle connects to and supports the others.
Together, the 13 APPs create an end-to-end framework that governs personal information from collection to destruction, leaving no stage of the data lifecycle unaddressed.
The 13 APPs can be grouped into five broad areas:
- Open and transparent management of personal information, including maintaining a clear privacy policy (APP 1)
- Anonymity and pseudonymity, giving individuals the option to interact without identifying themselves where practicable (APP 2)
- Collection rules covering both solicited and unsolicited personal information, and notification requirements (APPs 3, 4, 5)
- Handling personal information, including rules on use, disclosure, direct marketing, cross-border transfers, and government identifiers (APPs 6, 7, 8, 9)
- Integrity and access, covering the accuracy of records, their security, and an individual’s right to access and correct their own information (APPs 10, 11, 12, 13)
Each of these areas places specific and enforceable obligations on your business. Whether you run an accounting firm conducting KYC checks on new clients, or a financial services provider managing sensitive transaction records, every stage of your data handling sits within this framework. Knowing how the principles interconnect is what turns legal compliance from a checkbox exercise into a genuine operating standard.
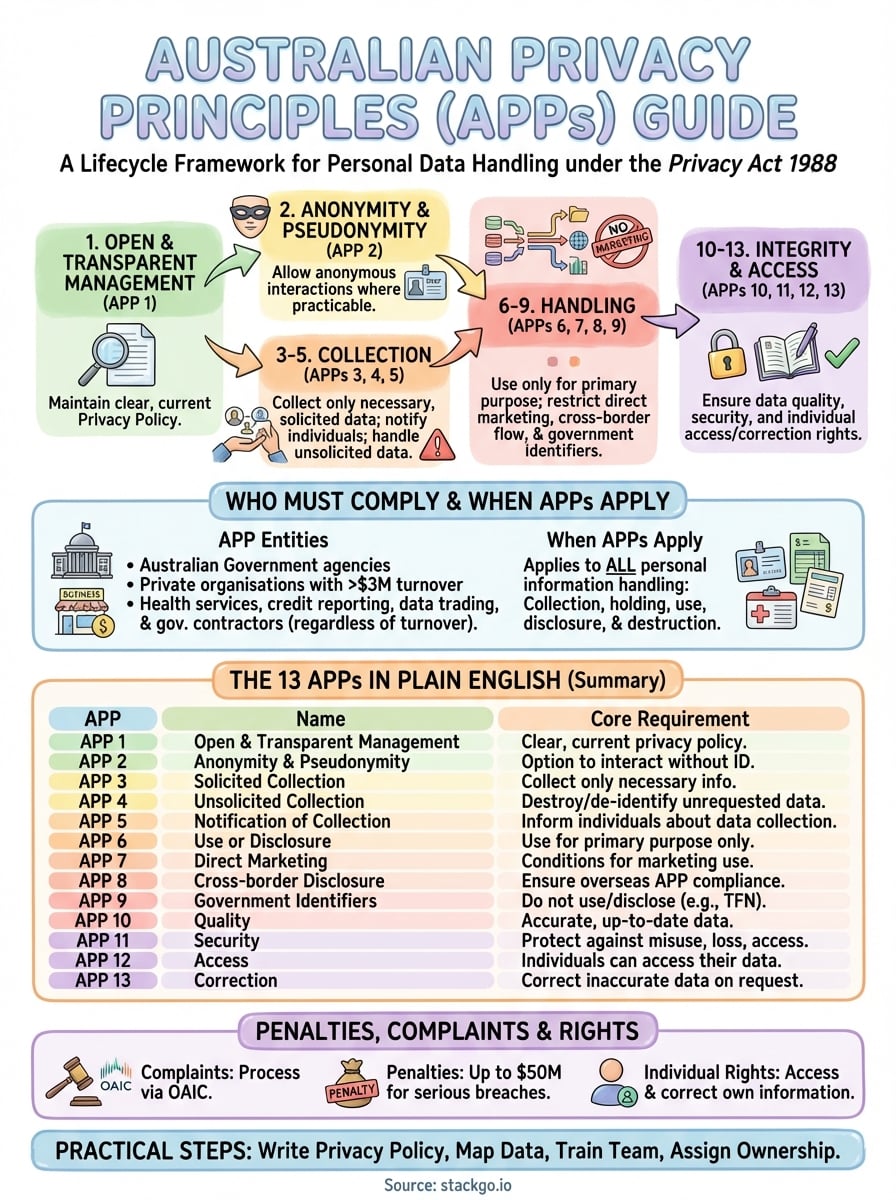
Who must comply and when APPs apply
Not every business in Australia falls under the APPs automatically, but more do than you might expect. The Privacy Act 1988 applies to what it calls APP entities, a category that includes Australian Government agencies and private sector organisations that meet certain thresholds. If your business processes personal information and sits within scope, compliance is not optional.
APP entities defined
An APP entity is either a government agency or a private sector organisation covered by the Privacy Act. For private businesses, the primary threshold is annual turnover: organisations with a turnover above $3 million per year are automatically covered. Below that threshold, a number of exceptions still bring you into scope. If your business provides health services, trades in personal information, is a contracted service provider to the Australian Government, or operates as a credit reporting body, the APPs apply regardless of revenue.
If you handle health information, government contracts, or trade in personal data, your turnover is irrelevant – the APPs apply to you.
Small businesses that sit below the $3 million threshold and fall outside the exceptions can still be covered voluntarily if they opt in, or find themselves captured by state and territory legislation that runs alongside the federal Privacy Act.
When the APPs apply to your data handling
The APPs apply at every stage of your engagement with personal information, which is any information or opinion about an identified individual or someone who is reasonably identifiable. This includes obvious data points like names, addresses, and identity documents, but also financial records, employment details, health information, and communications you hold about clients or staff.
For accounting firms and regulated businesses running KYC or AML checks, this is particularly relevant. The moment you collect a client’s name and tax file number to verify their identity, the APPs are in play. They govern how you collect that data, where you store it, who can access it, and how long you keep it. Having the Australian privacy principles explained in this context makes it clear that compliance starts at the point of collection, not after onboarding is complete.
The 13 APPs explained in plain English
Having the Australian privacy principles explained in plain terms gives you a working map of your obligations rather than a wall of legal text. Each of the 13 APPs targets a specific stage of how you handle personal information, and together they leave no part of the data lifecycle unaddressed. The table below gives you a direct summary of every principle.
| APP | Name | Core requirement |
|---|---|---|
| 1 | Open and transparent management | Maintain a clear, current privacy policy and manage personal information openly |
| 2 | Anonymity and pseudonymity | Allow individuals to interact without identifying themselves where practicable |
| 3 | Collection of solicited personal information | Only collect personal information that is reasonably necessary for your functions |
| 4 | Unsolicited personal information | Destroy or de-identify data you did not request and could not have collected lawfully |
| 5 | Notification of collection | Tell individuals why you are collecting their data and how you intend to use it |
| 6 | Use or disclosure | Only use or disclose personal information for the primary purpose it was collected |
| 7 | Direct marketing | Do not use personal information for direct marketing unless specific conditions are met |
| 8 | Cross-border disclosure | Take reasonable steps to ensure overseas recipients comply with the APPs |
| 9 | Government-related identifiers | Do not adopt or disclose government identifiers such as tax file numbers as your own |
| 10 | Quality | Keep personal information accurate, up-to-date, and complete |
| 11 | Security | Protect personal information from misuse, loss, and unauthorised access |
| 12 | Access | Give individuals access to their own personal information on request |
| 13 | Correction | Correct personal information that is inaccurate or out of date when asked |
What the collection principles mean for onboarding
When you collect a new client’s identity documents and financial details during onboarding, APPs 3, 4, and 5 all activate at the same time. You need a lawful reason to collect the data, a clear process for handling any information that arrives unsolicited, and a timely notification to the client about what you are collecting and why.
Your APP 5 notification must be clear and given at or before the point of collection, not buried in fine print that nobody reads.
For accounting firms running KYC or AML checks, this means your onboarding workflow must build these steps in from the start.
What the use and security principles mean day to day
Once you hold personal information, APPs 6 to 11 control every subsequent action you take with it. You cannot repurpose a client’s contact details for marketing if you originally collected them for identity verification purposes. You must also actively protect stored data with appropriate technical controls, and scrutinise any transfers to overseas software providers or servers.
APPs 12 and 13 add a further layer: your clients have enforceable rights to see and correct the information you hold about them, and you must have a clear process to handle those requests within a reasonable timeframe.
Practical steps to comply with the APPs
Understanding the Australian Privacy Principles explained as a framework is one thing; building operational habits around them is another. Compliance is not a one-time project you complete and file away. It requires documented processes, regular reviews, and clear accountability across your team for how personal information is handled at every stage of your business operations.
Write and publish a current privacy policy
APP 1 requires your business to maintain a privacy policy that is clearly written, up to date, and freely accessible to anyone who asks for it. Publish it on your website, link to it in your client onboarding materials, and review it whenever your data practices change. A policy that has not been updated since you first drafted it is unlikely to reflect how your business actually collects and uses personal information today, which creates direct regulatory exposure.
Your privacy policy is the first document a regulator or complainant will request when something goes wrong, so treat it as a live operating document, not a formality.
Your policy should name the types of personal information you collect, the purposes for which you collect it, and how individuals can contact you to access or correct their data. These details are not optional inclusions; they are the minimum standard set under APP 1.
Map your data and tighten your collection
Before you collect any personal information, document exactly what you are gathering, why you need it, and where it will be stored. A straightforward data mapping exercise, even a maintained spreadsheet, helps you confirm that each piece of information you hold is genuinely necessary under APP 3, and that you are not retaining data you have no lawful reason to keep. Repeat this exercise when you add new software, expand your services, or change your client onboarding workflow.

Your data map also directly informs APP 11, your security obligations. Once you know where personal information lives across your systems, you can apply access controls, encryption, and retention schedules to it. Information you no longer need should be destroyed or de-identified promptly rather than left dormant in shared drives or old email threads.
Train your team and assign clear ownership
Privacy compliance breaks down most often at the human level rather than the technical one. Your staff need to know what personal information they handle, who they can lawfully share it with, and how to respond when a client requests access under APP 12. Assigning a named owner for privacy obligations within your business, whether a compliance officer, practice manager, or operations lead, ensures accountability sits with a specific person rather than being assumed by everyone and actioned by no one.
Penalties, complaints and individual rights
When a breach of the Australian Privacy Principles occurs, the consequences are real and can escalate quickly depending on how your business responds. The Office of the Australian Information Commissioner (OAIC) is the primary body responsible for handling complaints, conducting investigations, and enforcing the Privacy Act 1988. Understanding this process matters whether you are on the receiving end of a complaint or actively building systems to prevent one.
How the complaints process works
When an individual believes their personal information has been mishandled, they can lodge a complaint directly with the OAIC. Before doing so, they are generally expected to raise the issue with your organisation first, giving you a reasonable opportunity to respond and resolve it internally. If you handle the complaint fairly and promptly, many matters end there. If you fail to engage or the complainant remains unsatisfied, the OAIC steps in to assess, mediate, or investigate further.
Responding quickly and transparently to a privacy complaint is always your best first move, because the OAIC considers how you handled it when deciding whether further action is warranted.
What penalties apply for APP breaches
Serious or repeated interference with privacy can result in significant financial penalties. For bodies corporate, civil penalty orders can now reach up to $50 million following the 2022 amendments to the Privacy Act, which were introduced in direct response to high-profile data breaches affecting millions of Australians. The OAIC can also issue determinations that require your business to change its practices, apologise to affected individuals, or pay compensation for non-economic loss such as distress or reputational harm. These are not theoretical outcomes; the OAIC has used its enforcement powers and continues to increase its investigative activity.
Individual rights you must respect
Having the Australian privacy principles explained fully means recognising that real people sit behind every record you hold. Individuals have the right to request access to their personal information under APP 12, and the right to ask you to correct inaccurate records under APP 13. Your business must respond within a reasonable timeframe and cannot charge a fee for access itself. Refusing or ignoring a valid access request is a direct breach of the APPs and gives the individual clear grounds to lodge a formal complaint with the OAIC.
Key takeaways for Australian businesses
Having the australian privacy principles explained in full gives you a clear picture of what is required and where most businesses fall short. The 13 APPs cover every stage of how you handle personal information, from the first collection through to destruction, and compliance depends on building genuine operational habits rather than ticking boxes on a checklist. Your privacy policy must be current, your data collection must be necessary and documented, and your team must know how to respond when clients exercise their rights.
For accounting firms and regulated businesses running identity verification and AML checks, the stakes are higher because you handle sensitive client data constantly. The good news is that the right tools make compliance significantly easier. StackGo’s IdentityCheck runs KYC and AML screening directly inside your existing software, with a dedicated privacy layer that keeps PII out of your CRM. See how IdentityCheck supports AUSTRAC Tranche 2 compliance or create a free account to test it for your business.









