If your organisation handles identity verification or digital authentication, you’ve likely come across references to the NIST digital identity guidelines, formally known as SP 800-63. Published by the U.S. National Institute of Standards and Technology, these guidelines define how organisations should proof, authenticate, and manage digital identities at varying levels of assurance. While they originate from the U.S. federal government, their influence stretches well beyond American borders and into frameworks that Australian regulated businesses encounter regularly.
Understanding SP 800-63 matters because it gives you a structured, risk-based approach to identity assurance, something directly relevant if you’re managing KYC, AML, or client onboarding obligations. At StackGo, we build identity verification tooling like IdentityCheck into the software you already use, so grasping these standards helps you make better decisions about how verification fits into your workflows.
This article breaks down the full SP 800-63 suite in plain terms: what each volume covers, the assurance levels it defines, how identity proofing and authentication requirements are structured, and where these guidelines sit relative to Australian compliance obligations. Whether you’re a compliance officer, practice manager, or operations lead, you’ll walk away with a solid working understanding of the framework, no prior reading of 200-page NIST documents required.
Why NIST digital identity guidelines matter
The NIST digital identity guidelines were written for U.S. federal agencies, but their influence has spread well beyond that original scope. Standards bodies, regulators, and private sector frameworks worldwide have adopted or directly referenced SP 800-63 when building their own identity assurance requirements. If you work in a regulated industry in Australia, such as accounting, financial services, or legal services, you are operating in an environment shaped partly by these principles, whether you realise it or not.
The global reach of a U.S. standard
When the U.S. National Institute of Standards and Technology publishes a framework this detailed, other countries pay attention. Australia’s own identity verification guidance, including the Trusted Digital Identity Framework (TDIF) and AUSTRAC’s guidance on customer identification programs, draws on the same risk-based assurance thinking that NIST formalised. The core logic, which is to match the rigour of your verification approach to the risk of getting it wrong, is now the baseline expectation across most developed regulatory environments.
The question is no longer whether your identity processes meet some vague standard of "good enough" – it is whether they meet a defined assurance level appropriate to the risk your organisation actually carries.
This matters practically for your organisation. If you handle KYC or AML obligations, the frameworks your regulator uses to assess compliance were shaped by or benchmarked against the same foundational thinking as SP 800-63. Understanding the source framework helps you interpret what your regulator expects, rather than trying to decode guidance that is already one step removed from its origin.
What weak identity assurance costs you
Getting identity verification wrong has consequences that go beyond a regulatory fine. Weak identity proofing lets fraudulent actors into your systems, creating liability exposure, downstream compliance failures, and potential harm to the clients whose data you hold. On the other side, overly burdensome verification processes drive legitimate clients away before they complete onboarding, which hits your revenue and reputation directly.
The NIST framework solves this tension by introducing tiered assurance levels that let you match verification rigour to actual risk, rather than applying one blunt approach to every situation regardless of context. A low-risk interaction does not need the same level of scrutiny as one that involves significant financial or legal consequences.
For Australian accounting firms now facing AUSTRAC AML/CTF obligations, this calibration is especially relevant. Your onboarding processes need to be robust enough to satisfy regulatory requirements but streamlined enough that clients actually complete them without dropping off. That balance is precisely what the assurance level model in SP 800-63 is designed to help you find.
Getting this right also protects you commercially. Clients who trust your verification process are more likely to complete onboarding, refer others, and remain long-term. Identity assurance is not a compliance checkbox bolted onto the end of a process; it directly shapes the client experience from the first interaction your business has with them.
What is in the SP 800-63 suite
SP 800-63 is not a single document. It is a suite of four related publications, each covering a distinct part of the digital identity lifecycle. NIST structured it this way because identity proofing, authentication, and federation each carry separate technical and policy requirements. Knowing what each volume addresses helps you identify which parts of the NIST digital identity guidelines apply directly to your organisation.
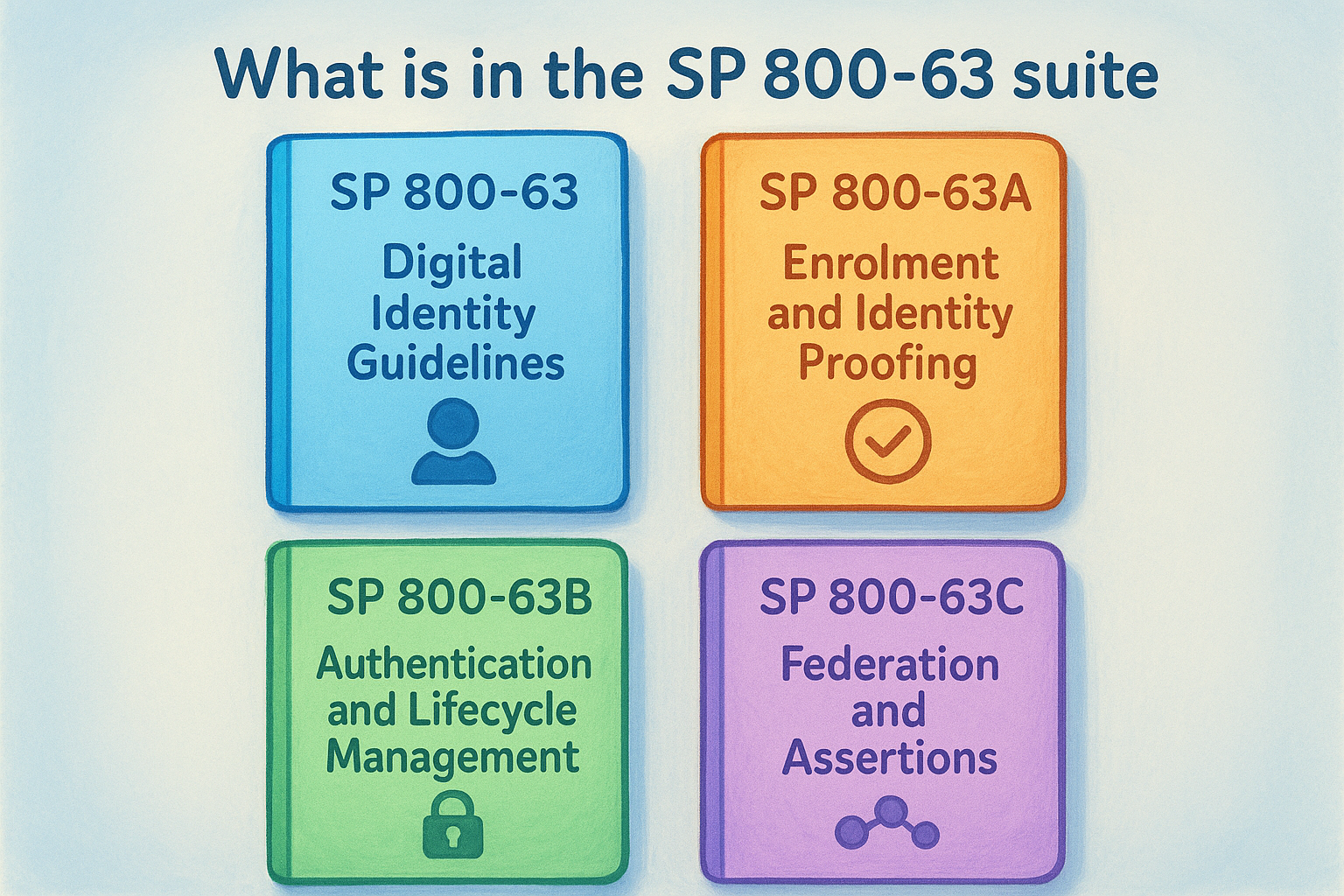
| Volume | Full title | Focus area |
|---|---|---|
| SP 800-63 | Digital Identity Guidelines | Risk framework and overall structure |
| SP 800-63A | Enrolment and Identity Proofing | Verifying who someone is |
| SP 800-63B | Authentication and Lifecycle Management | Verifying ongoing credential control |
| SP 800-63C | Federation and Assertions | Sharing verified identity across systems |
Identity proofing: what SP 800-63A covers
SP 800-63A defines how rigorously your organisation must verify an applicant’s identity before enrolling them or granting access. It introduces Identity Assurance Levels (IAL 1 through 3), which set the bar for what counts as acceptable identity evidence and how thoroughly that evidence must be validated. This is the volume most directly relevant to KYC and client onboarding obligations in regulated industries such as accounting and financial services.
For Australian accounting firms preparing for AUSTRAC AML/CTF compliance, SP 800-63A is the reference point for understanding what adequate verification actually requires in practice. The scrutiny it demands at IAL 2 and IAL 3, including document verification and biometric matching, aligns closely with what a sound customer identification program needs to demonstrate.
SP 800-63A is where abstract compliance obligations become concrete verification requirements.
Authentication and federation: SP 800-63B and SP 800-63C
SP 800-63B shifts focus to what happens after identity has been established. It defines Authentication Assurance Levels (AAL 1 through 3), governing how strongly someone must prove they control a credential on each subsequent login. It covers passwords, multi-factor authentication, and authenticator lifecycle management in detail.
SP 800-63C addresses scenarios where one system shares identity assertions with another, covering federation protocols like OpenID Connect and SAML. For most Australian professional services firms, this volume becomes relevant when you integrate identity verification across multiple platforms or pass verified identity data between systems in your existing tech stack.
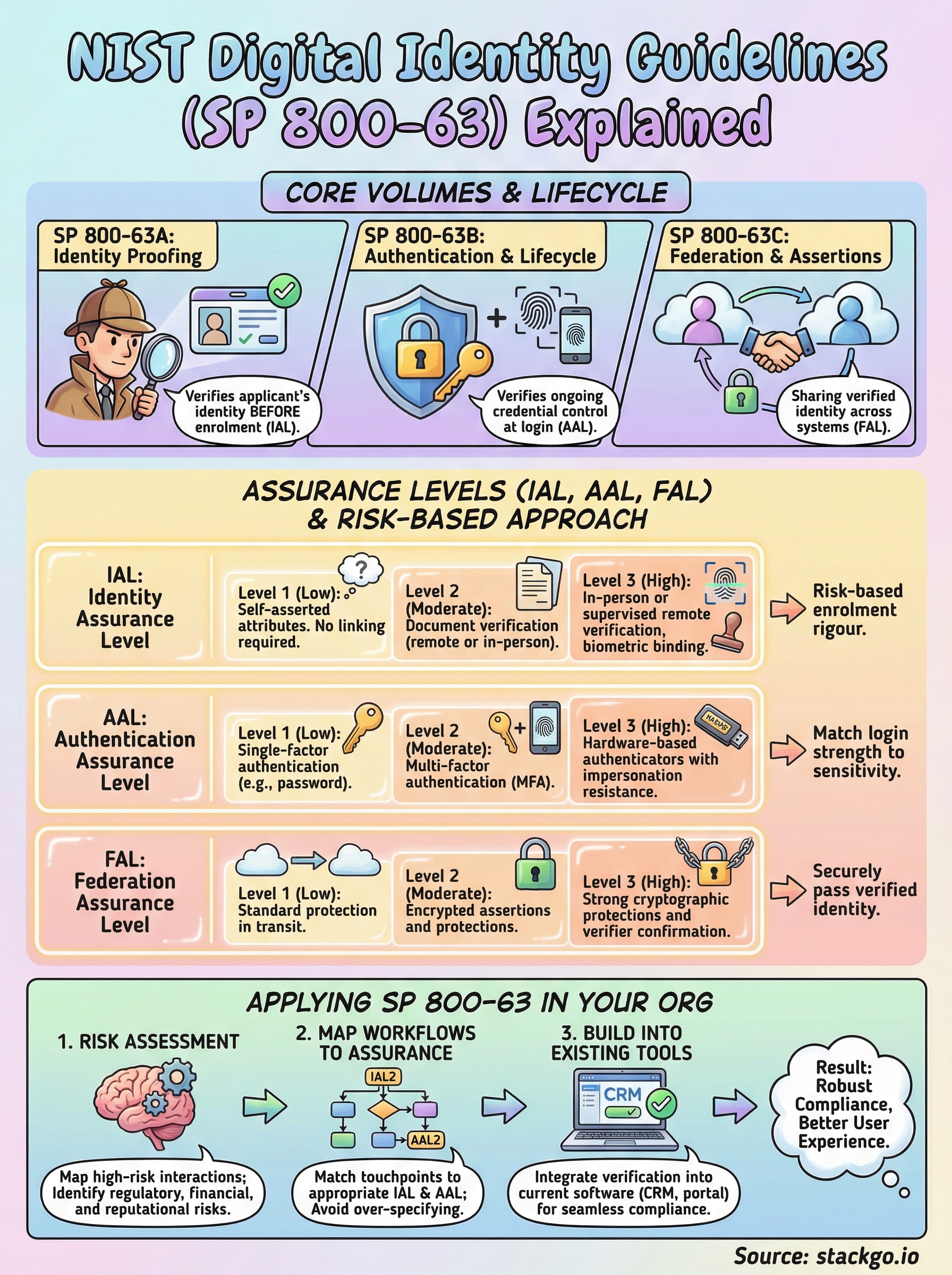
How assurance levels work: IAL, AAL and FAL
The nist digital identity guidelines organise identity risk into three separate assurance scales, each covering a different stage of the identity lifecycle. IAL governs how thoroughly you verified someone’s identity at enrolment, AAL governs how strongly they prove ongoing credential control, and FAL governs how reliably assertions pass between systems. These three scales operate independently, meaning your choices for one do not automatically determine the others.
Identity Assurance Level (IAL)
IAL sets the bar for how rigorously you must verify an applicant’s real-world identity before enrolment. The three levels work as follows:
- IAL 1: No requirement to link the applicant to a real-world identity. Self-asserted attributes are acceptable.
- IAL 2: Evidence of a real-world identity is required, with remote or in-person verification of supporting documents.
- IAL 3: In-person or supervised remote verification is required, with biometric binding to the applicant.
For most regulated professional services firms, IAL 2 is the relevant benchmark for client onboarding, since it requires document verification without mandating physical attendance.
Choosing an IAL too low for your risk profile creates compliance exposure; choosing one too high adds friction that pushes legitimate clients away before they complete onboarding.
Authentication Assurance Level (AAL)
AAL determines how strongly a user must prove they still control their credential on each login after initial enrolment. AAL 1 permits single-factor authentication. AAL 2 requires multi-factor authentication, combining something the user has, knows, or is. AAL 3 requires hardware-based authenticators with verifier impersonation resistance, reserving it for high-risk access scenarios.
Your organisation does not need to apply the same AAL across every system. Matching AAL to the sensitivity of what the credential unlocks is the correct approach, rather than defaulting to the highest level across the board regardless of context.
Federation Assurance Level (FAL)
FAL applies specifically to scenarios where one system passes verified identity assertions to another, such as a single sign-on provider sharing a verified token with a downstream application. FAL 1 through FAL 3 define progressively stronger protections for how those assertions are secured in transit and verified on receipt.
For Australian professional services firms, FAL becomes directly relevant when you connect identity verification tooling to the CRM or practice management platform your team already uses day-to-day.
What changed in SP 800-63 revision 4
NIST released the fourth revision of the nist digital identity guidelines in 2024, making it the most significant update to the suite since revision 3 published in 2017. The changes reflect a decade of real-world implementation experience, shifts in how identity fraud actually occurs, and the expanded role of remote and digital-first onboarding across every regulated sector. If your organisation’s identity verification approach is still calibrated to revision 3 assumptions, several of those assumptions are now outdated.
Dropped requirements that were creating false security
Revision 4 removes several controls that research and practice showed were counterproductive rather than protective. Mandatory password complexity rules and forced periodic password rotation are gone from AAL guidance, because evidence consistently showed these requirements pushed users toward predictable, weaker passwords rather than stronger ones. Knowledge-based authentication, which relied on personal questions like a mother’s maiden name, is no longer an acceptable verification method at any assurance level due to its well-documented susceptibility to data breach exploitation.
Removing a control that creates the appearance of security without delivering it is not weakening a standard; it is fixing one.
Stronger support for remote identity proofing
One of the most practically significant additions in revision 4 is expanded guidance on supervised remote identity proofing, which allows organisations to meet IAL 3 requirements without requiring applicants to attend in person. This is directly relevant if your firm operates across multiple locations or onboards clients remotely as standard practice rather than as an exception. The revised guidance specifies the technical and procedural controls needed to make remote supervised sessions equivalent to in-person verification.
Revision 4 also introduces more structured guidance around continuous evaluation, shifting the model from point-in-time verification toward ongoing risk assessment throughout the identity lifecycle. For compliance-focused businesses, this means your verification processes need to account for identity risk beyond the initial onboarding event, including monitoring for signals that a verified credential may have been compromised after enrolment.
How to apply SP 800-63 in your org
Applying the nist digital identity guidelines in your organisation does not require implementing every control across every system at once. The framework is risk-based by design, which means your first job is to understand where your highest-risk identity interactions actually occur, then prioritise those before expanding to lower-risk touchpoints.
Start with a risk assessment
Before you touch any tooling or documentation, map the interactions in your business where identity matters most. For an accounting firm preparing for AUSTRAC obligations, that typically means client onboarding, access to financial data, and any workflow involving sensitive personal information. Assign a preliminary risk rating to each interaction based on the harm that would result from an identity failure at that point, whether that harm is regulatory, financial, or reputational.
The risk assessment is not a one-time exercise; revisit it whenever you add a new service, system, or client type to your business.
Map your workflows to assurance levels
Once you have a risk picture, match each interaction to an appropriate IAL and AAL. Most client-facing onboarding in regulated professional services lands at IAL 2, requiring document verification without mandating physical attendance. Internal administrative access may only need AAL 2 multi-factor authentication rather than anything more demanding.
Avoid the temptation to apply the highest assurance level everywhere. Over-specifying your requirements increases friction and operational cost without improving your actual risk posture. The goal is a calibrated approach where each touchpoint carries exactly the verification weight it needs, nothing more.
Build verification into your existing tools
Implementing identity assurance does not require adopting a separate compliance platform that your team has to learn alongside everything else. Integrating verification directly into the software your staff already uses, whether that is your CRM, practice management system, or client portal, removes the friction that causes compliance steps to get skipped under pressure. Look for solutions that write verification outcomes back into your existing records automatically, so your team never has to switch context or manually update data after completing a check.
Next steps
The nist digital identity guidelines give you a structured way to think about identity risk, not just a list of controls to tick off. Whether you are an accounting firm preparing for AUSTRAC obligations or a financial services business tightening your onboarding processes, the framework gives you a clear language for matching verification rigour to actual risk at each touchpoint.
Start with your risk assessment, map your workflows to the right assurance levels, and identify where verification currently creates friction or gets skipped. Building checks directly into the tools your team already uses removes the main reason compliance steps fail in practice: context switching and manual data entry under time pressure.
When you are ready to put this into practice, test IdentityCheck for your business to see how identity verification runs inside your existing software without adding a separate platform your team has to learn alongside everything else.









