Regulatory obligations in Australia are shifting. Between the TPB’s existing compliance requirements for accountants and the upcoming AUSTRAC AML/CTF reforms, businesses across professional services, finance, and other regulated sectors face a growing list of rules to follow. Understanding how to mitigate regulatory risk isn’t optional anymore, it’s a core operational concern that directly affects your ability to serve clients and protect your business.
The real challenge isn’t awareness. Most business owners and compliance officers know the rules exist. The problem is execution: identity verification done manually, client onboarding scattered across disconnected tools, and compliance data sitting in places it shouldn’t be. These gaps are where regulatory risk thrives, and where penalties, reputational damage, and lost clients follow.
This guide lays out a practical framework you can apply to your own operations. We’ll walk through how to identify where your exposure sits, build processes that hold up under scrutiny, and use tools like StackGo’s IdentityCheck to embed compliance directly into the software you already use. No new tabs, no disconnected workflows, just a structured approach to reducing risk at every stage of client onboarding.
What regulatory risk looks like in practice
Regulatory risk isn’t abstract. It shows up in specific failures within your day-to-day processes: an identity check that was never completed before a client engagement started, a document that expired without being flagged, or verification results stored in a spreadsheet instead of a secure, auditable system. For accounting firms navigating TPB requirements, or financial services businesses preparing for AUSTRAC’s expanded AML/CTF obligations, these aren’t edge cases. They’re common patterns that regulators notice and that audits will surface.
The compliance gaps that cost you most
Most businesses don’t lose control of their regulatory obligations all at once. The breakdown happens gradually, often driven by manual processes that worked fine at lower volumes but can’t scale. A team member verifies a client’s identity by checking a document, but no record is created that an auditor can later review. Another team member onboards a client through a separate system that doesn’t connect to your CRM, so the verification result lives in a silo and never gets properly documented.
The gap between knowing your obligations and consistently meeting them is where regulatory penalties are born.
Closing that gap is precisely why understanding how to mitigate regulatory risk requires more than policy documents. It demands workflows that make the compliant path the default path, not the extra step.
Where the exposure shows up in onboarding
Client onboarding is the most common flashpoint. It’s the stage at which KYC and AML checks need to happen, identity documents need to be verified, and outcomes need to be recorded against the client record. When this process runs across disconnected tools, email threads, and manual data entry, the risk compounds at every step. A single missed verification on one client file can expose your business to a formal breach finding.
The table below shows the most common onboarding failure points and their regulatory consequences:
| Failure Point | Regulatory Consequence |
|---|---|
| No identity check before engagement starts | Breach of TPB or AML/CTF obligations |
| Verification result not recorded | No audit trail available for regulators |
| PII stored in CRM without access controls | Privacy Act and data security exposure |
| Manual re-entry of verification data | High error rate, inconsistent records |
| Expired documents not flagged after onboarding | Ongoing compliance gap post-engagement |
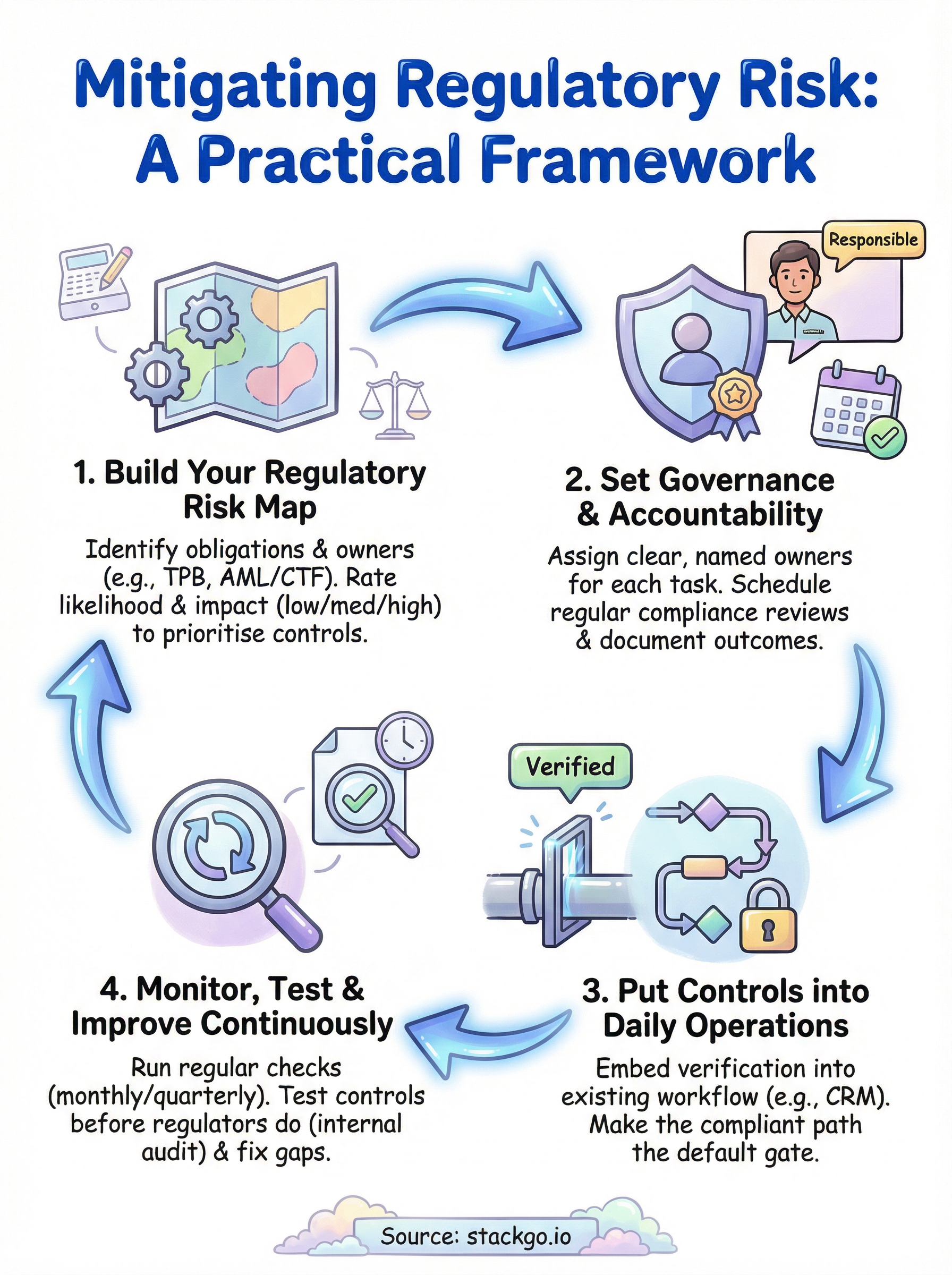
Build your regulatory risk map
A regulatory risk map gives you a structured view of where your obligations sit and where your current processes fall short. Before you can understand how to mitigate regulatory risk effectively, you need to see it clearly. Start by listing every regulation that applies to your business, then map each one to the specific workflow or team responsible for meeting it.

Identify your obligations and owners
Your first step is to produce a simple register. For each regulation, record what the obligation requires, which team or role is responsible, and how compliance is currently demonstrated. Australian accounting firms should include TPB Code of Professional Conduct requirements and, if applicable, the upcoming AUSTRAC AML/CTF obligations. Financial services businesses should add ASIC licensing conditions and relevant privacy obligations under the Privacy Act 1988.
| Obligation | Responsible Role | Current Control | Evidence of Compliance |
|---|---|---|---|
| KYC check before client engagement | Practice Manager | Manual document review | Email record |
| AML/CTF customer due diligence | Compliance Officer | Standalone tool | PDF report |
| PII access controls | IT Manager | CRM permissions | Access log |
Rate likelihood and impact
Once you have your register, score each obligation against two dimensions: how likely a failure is and how significant the impact would be if one occurred. A simple low/medium/high scale works for most firms. This scoring tells you where to invest in stronger controls first, so you are not spending equal effort on a minor procedural gap and a breach that could result in licence suspension.
Your risk map is only useful if you update it whenever regulations change or your business processes shift.
Set governance and accountability
A risk map tells you where the problems are. Governance tells you who is responsible for fixing them and keeping them fixed. Without clear ownership, compliance tasks fall through the gaps, and nobody is accountable when something goes wrong. Assigning roles is not bureaucracy; it is the foundation of a system that holds up when regulators come asking.
Assign clear ownership for each obligation
Each compliance obligation in your register needs a named owner, not a team or a department. When a TPB or AUSTRAC requirement is breached, regulators do not ask which team failed; they ask who was responsible. Make the ownership explicit: the Practice Manager owns the KYC check process, the Compliance Officer owns AML/CTF customer due diligence, and so on.
A single named owner for each obligation creates accountability that a shared responsibility never can.
Use a simple accountability template to document this alongside your risk register:
| Obligation | Owner | Reviewer | Review Frequency |
|---|---|---|---|
| KYC check before client engagement | Practice Manager | Director | Monthly |
| AML/CTF customer due diligence | Compliance Officer | Director | Quarterly |
| PII access controls | IT Manager | Compliance Officer | Quarterly |
| Document expiry monitoring | Practice Manager | Compliance Officer | Monthly |
Schedule regular compliance reviews
Ownership only works if there are scheduled checkpoints where owners report on the status of their obligations. Build a quarterly review into your calendar where each owner confirms their controls are operating, flags any upcoming regulatory changes, and identifies gaps before they become breaches. This cadence is central to understanding how to mitigate regulatory risk on an ongoing basis, not just at initial setup. A short written summary from each owner, reviewed by a director or principal, creates the documentation trail that regulators expect to see during an audit.
Put controls into daily operations
A governance structure only works if your daily processes enforce it automatically. The most common reason compliance breaks down is that the correct action requires extra effort, so staff skip it under pressure. Understanding how to mitigate regulatory risk at an operational level means removing that friction by building controls directly into the tools your team already uses every day.
Embed verification into your existing workflow
Requiring a separate login, a new platform, or a manual export to complete a compliance task guarantees that the task will be skipped or deferred. The better approach is to trigger identity verification from inside your CRM, such as HubSpot or Salesforce, so that the check happens as part of creating or updating a contact record.
Controls embedded at the point of action are far harder to bypass than controls that require a separate step.
StackGo’s IdentityCheck works exactly this way: it reads the contact’s information directly from your CRM, runs the verification, and writes the result back to the same record, with no separate platform to manage and no PII stored in the CRM itself.
Make the compliant path the default
Structure your onboarding process so that a client file cannot progress to the engagement stage without a verified identity check on record. Use your CRM’s pipeline stages or deal properties to enforce this as a gate, not a reminder.

The template below gives you a starting point for a gated onboarding checklist:
| Stage | Required Control | Gate Condition |
|---|---|---|
| New contact created | Identity check triggered | Check must return a result |
| Engagement accepted | Verification outcome recorded | Status must be "Verified" |
| Ongoing engagement | Document expiry monitored | Alert if document expires within 30 days |
Monitor, test, and improve continuously
Setting up your risk map and governance structure is not a one-time task. Regulations change, your client base grows, and the processes that worked last year may leave gaps today. Continuous monitoring means you catch those gaps yourself before an auditor or regulator finds them first. This is the part of understanding how to mitigate regulatory risk that most businesses underinvest in.
Run regular compliance checks
Schedule a monthly review of your active client files to confirm that every engagement has a verified identity check on record and that no documents have expired. For firms subject to AUSTRAC obligations, this review should also confirm that customer due diligence records reflect any material changes to client risk profiles. A brief review, assigned to a named owner, takes less than an hour and produces the documentation trail regulators expect.
The businesses that avoid regulatory penalties are not those with perfect processes from day one; they are the ones that catch and fix gaps before those gaps compound.
| Review Item | Frequency | Owner | Pass Condition |
|---|---|---|---|
| Identity check on all active files | Monthly | Practice Manager | 100% verified |
| Expired document alerts | Monthly | Practice Manager | Zero outstanding |
| AML/CTF risk profile updates | Quarterly | Compliance Officer | All changes recorded |
Test your controls before regulators do
Run a structured internal audit once a year where you select a sample of client files and confirm every required control was applied. Document the results, note any failures, and assign a remediation owner with a clear deadline for each gap. Use this checklist as a starting point:
- Select 10 to 15 client files opened in the past 12 months
- Confirm each file has a verified identity check recorded
- Confirm no verification documents have expired
- Confirm AML/CTF risk classification is documented where applicable
- Record failures and assign remediation owners with deadlines
Next steps to keep risk under control
The framework in this guide gives you a clear path for how to mitigate regulatory risk across your onboarding and compliance operations. Your next move is to start with the highest-impact item: mapping your current obligations against your existing processes and identifying the first gap you can close this week.
Avoid trying to fix everything at once. Pick one control to embed first, whether that is gating your onboarding pipeline on a verified identity check or assigning named owners to each compliance obligation. Build from there, and schedule your first quarterly review within 90 days of implementing your changes.
If identity verification is your most pressing exposure, StackGo’s IdentityCheck lets you run AUSTRAC-compliant AML/CTF checks directly inside your existing CRM, with results written back automatically and no PII stored in the platform. See how IdentityCheck handles AUSTRAC Tranche 2 obligations and create a free account to test if it fits your business.









