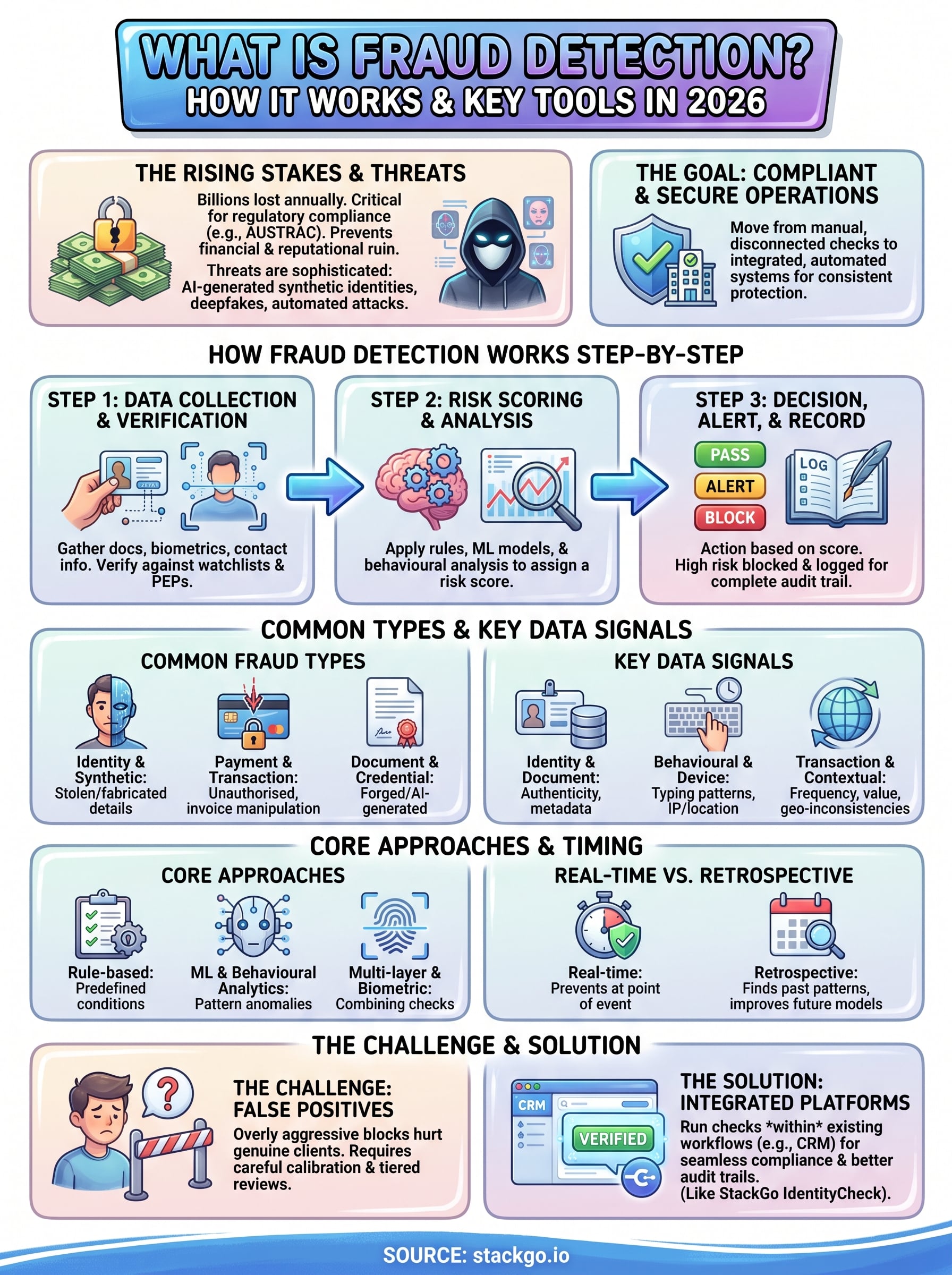
Every year, Australian businesses lose billions to fraudulent activity, from falsified identities during client onboarding to synthetic documents slipping through manual checks. Understanding what is fraud detection goes beyond a textbook definition. For regulated firms in accounting, financial services, and professional services, it’s the difference between a compliant operation and a costly breach.
Fraud detection refers to the systems, processes, and tools used to identify dishonest or illegal activity before it causes financial or reputational damage. It covers everything from verifying a client’s identity at the point of onboarding to flagging suspicious patterns across transactions. For businesses bound by KYC/AML obligations, especially with AUSTRAC’s expanding regulatory reach, getting this right isn’t optional. It’s a core operational requirement.
This article breaks down how fraud detection actually works, the key techniques behind it, and the tools businesses are using in 2026 to stay ahead of bad actors. We’ll also look at where identity verification fits into the fraud prevention chain, an area where platforms like StackGo help regulated businesses run compliance checks directly from their existing CRM, removing the friction of disconnected systems and reducing the manual errors that fraudsters rely on.
Whether you’re tightening up your firm’s onboarding process or evaluating new compliance tooling, this guide gives you a clear, practical foundation to work from.
Why fraud detection matters in 2026
Fraud has become more sophisticated, more automated, and more costly than at any point in recent history. Australian businesses lost an estimated $2.74 billion to scams and fraud in 2023 alone, according to ACCC Scamwatch data, and that figure continues to climb year on year. Understanding what is fraud detection and acting on it has shifted from a nice-to-have to a business-critical function, particularly for firms operating under regulatory scrutiny.
The financial stakes keep rising
The numbers are stark. Identity fraud now accounts for a significant and growing share of total fraud losses, with criminals using stolen or fabricated credentials to open accounts, access services, and extract value before detection occurs. For accounting firms, legal practices, and financial services providers, a single fraudulent onboarding can trigger direct financial losses, regulatory fines, and lasting reputational damage that takes years to repair.
Fraud losses are not just a line item on a balance sheet. They cascade into compliance penalties, legal costs, and eroded client trust that compounds over time.
Small and mid-sized firms are particularly exposed because they often rely on manual verification processes that are no match for modern fraud tactics. The assumption that sophisticated fraud only targets large corporations is outdated and costly. Criminals actively seek out businesses where verification steps are inconsistent, under-resourced, or easy to bypass with a convincing document.
Regulatory obligations are tightening in Australia
The landscape has shifted significantly for Australian businesses, especially those in accounting, financial advice, and professional services. AUSTRAC’s AML/CTF reforms have expanded the scope of regulated entities, pulling in businesses that previously operated outside formal compliance frameworks. If your firm now falls under these obligations, the requirement to verify client identities and screen for suspicious activity is no longer discretionary.
The Tax Practitioners Board has also tightened its expectations around client verification under its Code of Professional Conduct updates. Firms that fail to implement adequate fraud detection and identity verification processes risk sanctions, loss of registration, and civil penalties. Running these checks manually creates its own risks, including inconsistent documentation, missed red flags, and human error compounding under time pressure during busy periods.
Technology has changed what fraudsters can do
Fraudsters in 2026 are not just using stolen documents. They are using AI-generated synthetic identities, deepfake video during live verification checks, and increasingly convincing forgeries that pass basic visual inspection with ease. The tools available to bad actors have become far more accessible, meaning a small operation can now execute attacks that once required significant technical resources and expertise.
Your existing processes need to account for this new threat environment, not the one from five years ago. If your onboarding workflow relies on manual document checks or disconnected systems, it creates gaps that modern fraud techniques exploit directly. Businesses that have embedded automated, integrated verification into their core workflows are not just more efficient; they are structurally harder targets because fraud attempts encounter consistent, layered checks at every entry point rather than a single manual review.
How fraud detection works step by step
Understanding what is fraud detection becomes clearer when you see it as a process rather than a single check. Fraud detection moves through a series of deliberate steps, each designed to catch problems earlier and with more accuracy than the one before it. Businesses that understand these steps can identify where their current processes are weakest and make targeted improvements without overhauling everything at once.

Step 1: Data collection and identity verification
The process starts the moment a new client, user, or transaction enters your system. Data collection gathers identity documents, biometric information, contact details, and behavioural signals from the point of entry. In client onboarding, this means capturing government-issued ID, matching it to the person presenting it, and cross-referencing details against watchlists, PEP databases, and sanctions lists.
Manual document checks introduce inconsistency and delay, giving fraudsters an opening. Automated verification tools read document data, run liveness checks, and return a verified outcome in seconds rather than days, which removes the human error that fraudulent actors actively look for.
Step 2: Risk scoring and pattern analysis
Once data is collected, the system applies a risk score based on rules, statistical models, or machine learning. High-risk signals include mismatched identity details, unusual transaction volumes, and device fingerprints appearing across multiple accounts. That score determines whether the system approves the activity, flags it for manual review, or blocks it outright.
The difference between a useful fraud system and a disruptive one comes down to how well its risk thresholds are calibrated to your specific business context.
Pattern analysis improves over time as the system accumulates more data. A score that works well at onboarding may need adjustment as you learn which signals are most predictive for your client base and industry.
Step 3: Decision, alert, and record
The final step translates the risk score into a concrete action. Low-risk interactions proceed without friction. Medium-risk cases trigger an alert for a compliance officer to review. High-risk events are blocked and logged with a full audit trail, which matters when you need to demonstrate compliance during a regulatory review.
That audit trail is not optional for regulated Australian businesses. AUSTRAC’s AML/CTF frameworks require firms to document verification outcomes and flag suspicious activity, making accurate record-keeping a direct legal obligation rather than just good practice.
Common fraud types businesses should watch
Part of understanding what is fraud detection is knowing exactly what you’re detecting. Fraud does not look the same across every industry or business model, but several types appear consistently across regulated sectors in Australia. Recognising the specific fraud types that apply to your operations helps you target your detection efforts where they will have the most impact, rather than spreading resources across every conceivable risk.
Identity fraud and synthetic identities
Identity fraud remains the most common threat for businesses running client onboarding processes. In a straightforward case, a bad actor uses stolen personal details to impersonate a real person, passing verification checks with legitimate-looking credentials. The more difficult variant is synthetic identity fraud, where criminals combine real and fabricated data to create an identity that does not match any existing individual, making it harder for traditional checks to catch.
Synthetic identity fraud is particularly damaging because it can pass basic document verification while still being entirely fictitious, meaning manual review alone is rarely enough.
Australian professional services firms, particularly those onboarding new clients under AML/CTF obligations, are a direct target for this type of fraud. Criminals understand that firms with manual or inconsistent verification steps are easier to penetrate than those using automated, layered checks.
Payment and transaction fraud
Payment fraud covers a wide range of activity, including unauthorised transactions, invoice manipulation, and business email compromise where attackers intercept legitimate payment instructions and redirect funds. For accounting and financial services firms, invoice fraud is a persistent problem, often involving altered bank account details or duplicate billing designed to slip through under time pressure.
Your exposure increases when payment approvals rely on a single point of human review without automated cross-checks. Firms that implement dual-approval workflows alongside transaction monitoring close off the most common entry points for this type of fraud.
Document and credential fraud
Fraudulent documents have become harder to spot with the naked eye. AI-generated identity documents, manipulated PDFs, and forged certificates now circulate at a scale that manual review cannot consistently catch. Credential fraud also extends to fabricated professional qualifications, fake business registrations, and falsified financial records submitted during onboarding or tender processes.
For businesses in regulated industries, accepting a fraudulent document during onboarding carries direct compliance consequences, not just financial ones. Automated document verification tools that check for tampering, font inconsistencies, and metadata anomalies provide a layer of protection that manual review simply cannot replicate at scale.
Core detection approaches used today
When businesses ask what is fraud detection in practical terms, the answer comes down to the methods running underneath the surface. Modern fraud detection does not rely on a single technique. It layers multiple approaches together so that when one method misses something, another catches it. Understanding the core approaches helps you assess how well your current setup actually covers your exposure.
Rule-based detection
Rule-based systems are the foundation of most fraud detection setups. They work by applying predefined conditions to incoming data, flagging or blocking activity whenever a specific threshold is crossed. Examples include blocking transactions above a set value, rejecting documents from high-risk jurisdictions, or flagging accounts created with disposable email addresses.
These rules are fast and transparent, which makes them easy to audit and adjust. Their weakness is rigidity. Fraudsters who understand your rules can craft attempts that stay just below the detection threshold. Rule-based systems work best when they run alongside more adaptive methods rather than as a standalone defence.
Machine learning and behavioural analytics
Machine learning models move beyond fixed rules by finding patterns across large volumes of data that no human reviewer could spot manually. They build a baseline understanding of normal behaviour for your client base, then surface anomalies, a login from an unusual location, a verification attempt with inconsistent biometric data, or a transaction volume that spikes outside established norms.
Behavioural analytics adds a layer that static checks cannot replicate, because it identifies fraud through deviation from normal patterns rather than matching known bad signals.
Supervised models learn from labelled examples of confirmed fraud, while unsupervised models detect outliers without needing prior examples. In practice, most mature fraud systems combine both. The trade-off is that machine learning models require quality training data and ongoing tuning to stay accurate as fraud tactics evolve, so they need active management rather than a set-and-forget approach.
Multi-layer and biometric verification
Layering multiple verification methods at the point of onboarding closes the gaps that any single check leaves open. Biometric verification, including facial recognition and liveness detection, confirms that the person presenting an identity document is physically present and matches the document holder. Combined with document authenticity checks and database cross-referencing, this multi-layer approach significantly raises the effort required to defeat your controls.
Firms integrating these checks into their existing CRM or case management software gain the most practical benefit, because every client interaction passes through consistent verification without creating parallel workflows.
Key data signals fraud systems rely on
No fraud detection system is better than the data feeding it. When you dig into what is fraud detection at an operational level, you quickly see that detection accuracy depends entirely on which signals the system captures and how those signals are weighted. Knowing what data matters most helps you evaluate whether your current tooling is actually covering your exposure or leaving blind spots.
Identity and document signals
Identity signals form the first line of defence during onboarding. These include the authenticity of submitted documents, the consistency between document data and the information a client provides directly, and whether the identity matches records held in government or credit databases. Discrepancies between a name, date of birth, or address across these sources are strong early indicators of fraudulent intent.
Document metadata checks add another layer, looking at file creation dates, editing software traces, and font consistency across identity documents. A legitimate passport scanned and uploaded will carry specific metadata patterns. A manipulated or AI-generated document often does not, and those anomalies surface when your verification system is built to look for them rather than just confirm a visual match.
Behavioural and device signals
Behavioural signals capture how a person interacts with your system, not just what they submit. Unusual typing rhythms, copy-pasted form entries, and hesitation patterns during an identity verification flow are all deviations from normal user behaviour that fraud detection engines flag for further review. These signals are difficult to fake consistently across an entire session.
Device fingerprinting cross-references hardware identifiers, browser settings, and IP geolocation to detect when multiple accounts or applications originate from the same device or network.
Velocity signals sit within this category too, covering how quickly a user completes steps that typically take time, like reading terms or filling in address fields. Fraudsters using automated tools often complete these steps at speeds that are statistically impossible for a real person.
Transaction and contextual signals
Transaction signals apply most directly to financial services and payment workflows. These include transaction frequency, value anomalies, and geographic inconsistencies between where a client claims to be located and where their activity is actually originating. A client onboarded as a sole trader in Melbourne who initiates transactions consistent with a high-volume commercial operation triggers a contextual mismatch that warrants investigation.
External watchlist data, including AUSTRAC sanction lists, PEP registries, and adverse media feeds, rounds out the contextual layer by cross-referencing client identities against known bad actors and politically exposed individuals at both onboarding and ongoing review stages.
Essential fraud detection tools and platforms
When you look at what is fraud detection in practice, the tools you deploy determine how much protection that process actually delivers. The market offers a broad range of platforms, from standalone identity verification tools to full compliance suites, and choosing the right combination depends on your industry, your regulatory obligations, and how your existing systems are set up.
Identity verification platforms
Identity verification platforms sit at the entry point of your fraud defence. They automate the document capture, liveness detection, and database cross-referencing that manual onboarding processes handle inconsistently. Products like Jumio, Onfido, and AU10TIX process identity documents across hundreds of countries, check biometric matches, and return a verified outcome in seconds rather than requiring staff to review files manually.
The practical value of an identity verification platform is not just speed. It is the consistency of applying the same rigorous checks to every single onboarding, regardless of workload or time pressure.
Australian businesses with AUSTRAC obligations benefit most when these tools connect directly to their CRM or case management software, so verification outcomes are recorded automatically rather than manually transferred between systems.
Transaction monitoring and analytics tools
Transaction monitoring tools focus on ongoing activity rather than one-time onboarding checks. Platforms like NICE Actimize and Oracle Financial Services Anti Money Laundering analyse transaction patterns in real time, scoring each event against behavioural baselines and known fraud typologies. They flag anomalies such as sudden volume spikes, unusual counterparty patterns, and geographic inconsistencies for compliance teams to review.
These tools are most effective when they receive clean, structured data from upstream verification steps. Gaps in your onboarding data degrade the accuracy of downstream transaction monitoring, so both layers need to work in sequence rather than independently.
Integrated compliance platforms
Integrated platforms combine identity verification, watchlist screening, and audit trail management into a single workflow that sits inside your existing software rather than beside it. For accounting and professional services firms, this model removes the need to switch between a CRM, a verification portal, and a separate reporting tool every time a compliance check runs.
StackGo’s IdentityCheck is built precisely for this use case, running KYC and AML checks directly within HubSpot or Salesforce so your team works inside the tools they already use. Verification results write back to the contact record automatically, creating a complete audit trail without manual data entry or disconnected systems.
Real-time vs retrospective fraud detection
One of the most practical distinctions in understanding what is fraud detection is the difference between catching fraud as it happens versus discovering it after the fact. Both approaches serve a purpose, and the most resilient fraud detection setups use them together rather than treating them as alternatives. Knowing where each one fits helps you prioritise where to invest your detection resources first.
Real-time detection
Real-time detection evaluates every event at the moment it occurs, whether that is a client submitting an identity document during onboarding, a payment being initiated, or a login attempt from a new device. Automated verification engines and risk scoring models run instantly, returning a pass, flag, or block decision before the transaction or interaction completes. This approach prevents fraud from entering your system rather than cleaning up the damage afterward.
The core advantage of real-time detection is that it stops bad actors before they extract value, which matters far more than identifying fraud after the fact.
The trade-off is computational speed and accurate calibration. If your risk thresholds are set too aggressively, real-time systems block or delay legitimate clients during onboarding, which creates friction that damages your client experience and conversion rates. Calibrating your real-time controls to match your actual client base takes deliberate tuning and ongoing adjustment as client behaviour evolves.
Retrospective detection
Retrospective detection reviews historical data to find fraud patterns that were not visible at the time of the original event. Compliance teams use it to identify suspicious behaviour that built slowly across multiple interactions, such as a client whose transaction volume escalated gradually over several months in a way that no single real-time check would have flagged.
Retrospective analysis also plays a critical role in improving your real-time models. When you identify confirmed fraud cases in historical data, you use those examples to retrain your detection rules and machine learning models so future real-time checks become more accurate. Without a structured retrospective review process, your real-time controls gradually drift out of alignment with how fraud actually presents in your client base.
| Detection type | When it acts | Primary benefit |
|---|---|---|
| Real-time | At point of event | Prevents fraud before damage occurs |
| Retrospective | After the fact | Surfaces patterns and improves future controls |
Running both layers in parallel gives your compliance function the widest possible coverage, with real-time controls catching known threats immediately and retrospective analysis catching what slips through and feeding those learnings back into the system.
Cutting false positives without hurting customers
One of the most underappreciated challenges in understanding what is fraud detection is that the system needs to catch bad actors without blocking legitimate clients in the process. False positives, where genuine customers are flagged, rejected, or delayed by an overly cautious detection model, create real operational damage. Your compliance team spends time reviewing cases that turn out to be clean, and your clients experience friction that undermines their confidence in your firm at exactly the moment you are trying to establish trust.
Why false positives are a real business problem
False positives are not just an inconvenience. For professional services firms, a rejected identity check during onboarding delays revenue, disrupts the client relationship, and often requires manual intervention to resolve, which adds cost and time to a process you automated specifically to avoid those outcomes. Clients who encounter repeated verification failures are far more likely to abandon the onboarding process entirely, even when their credentials are completely legitimate.
A false positive rate that looks small in percentage terms becomes a significant operational burden when your firm processes hundreds of verifications each month.
The reputational cost compounds over time, particularly in markets like accounting and financial services where client referrals and professional reputation drive growth. A client who was incorrectly flagged during onboarding will remember that experience and may share it.
Calibrating your risk thresholds
Your fraud detection system applies risk scores based on signals, and the thresholds you set determine where the line between approve, review, and reject sits. Setting that line too low generates excessive false positives. Setting it too high lets fraud through. Neither extreme serves your business, so calibration is an ongoing process, not a one-time configuration.
Review your false positive rate regularly against confirmed fraud outcomes to identify whether your thresholds are drifting out of alignment with your actual client base. Seasonal patterns, new client segments, and changes in the fraud landscape all shift what normal behaviour looks like, and your thresholds need to reflect those shifts.
Using tiered review rather than binary decisions
A binary approve-or-reject system pushes borderline cases toward rejection when they should go to a structured manual review queue. Tiered review creates a middle layer where a compliance officer can assess flagged cases quickly using the full context the system has already gathered, rather than starting the check from scratch.
Building that review layer into your workflow reduces false rejections while keeping your compliance function in control of edge cases that automated rules cannot resolve cleanly.
How to implement fraud detection in your business
Putting theory into practice on what is fraud detection requires a structured rollout rather than trying to fix every vulnerability at once. Start by mapping where fraud can enter your business, which for most regulated Australian firms means client onboarding, payment approval, and document submission. Prioritise those entry points first, then expand your controls outward as your detection capability matures.
Start with your highest-risk entry points
Your onboarding workflow carries the highest concentration of fraud risk because it is where unverified individuals first gain access to your services. Assess your current process honestly: are verification steps consistent across every client, or do they vary depending on who handles the intake? Gaps in consistency are where fraud enters, and closing those gaps with automated, integrated verification delivers the most immediate reduction in your exposure.
Focus your first implementation on the checks that matter most for your regulatory obligations:
- Identity document verification with liveness detection at onboarding
- Watchlist and sanctions screening against AUSTRAC and PEP databases
- Automated record-keeping that logs verification outcomes against client records without manual data entry
Connect verification to your existing systems
The biggest practical mistake firms make during implementation is deploying verification tools that operate outside their core CRM or practice management software. When verification runs in a separate portal, staff switch between systems, outcomes get manually transcribed, and the audit trail becomes inconsistent. That inconsistency is a compliance liability in its own right.
Integrating verification directly into the software your team already uses removes the friction that causes staff to skip or rush checks under time pressure.
Platforms that write verification outcomes back to the client record automatically give your compliance function a clean, searchable audit trail that satisfies regulatory requirements without adding administrative overhead to every onboarding interaction.
Build in a review and improvement cycle
Implementation is not a one-time event. Your fraud detection controls need regular review to stay aligned with how your client base and the threat landscape actually behave. Set a quarterly review cadence that examines your false positive rate, your confirmed fraud catches, and any new fraud typologies your industry is experiencing.
Use confirmed fraud cases as training inputs to sharpen your detection rules and thresholds over time. A fraud detection setup that improves continuously is structurally more resilient than one configured once and left to run untouched.
A simple way to get started
Understanding what is fraud detection is the first step. Turning that understanding into a working compliance process is where most firms stall, usually because the tools they evaluate require new software, new workflows, and new training for staff who are already stretched.
StackGo’s IdentityCheck removes that barrier by running identity verification and AML/CTF checks directly inside HubSpot or Salesforce, the platforms your team already uses every day. Verification outcomes write back to the client record automatically, so your audit trail is clean and your team never needs to leave their existing workflow to stay compliant.
For Australian accounting firms preparing for AUSTRAC’s Tranche 2 obligations, this matters practically right now. You can run AUSTRAC-compliant AML/CTF checks inside your existing software without rebuilding your onboarding process from scratch. If you want to see whether it fits your setup, create a free account and run a test check before committing to anything.









