Passwords get stolen. Documents get forged. But your fingerprint, your face, your iris, these remain uniquely yours. Biometric identity verification uses these physical characteristics to confirm someone is who they claim to be, and it’s rapidly becoming the standard for secure digital identification across Australia’s regulated industries.
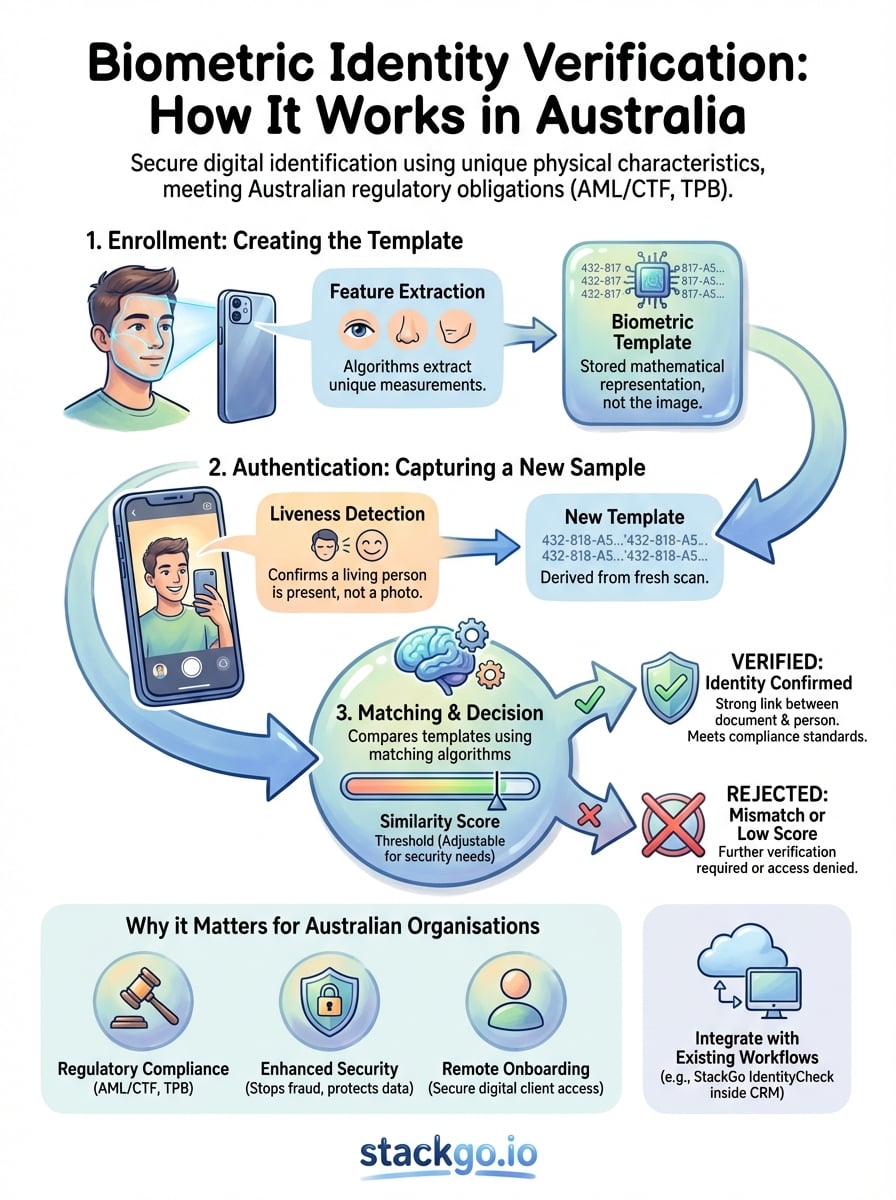
For accounting firms navigating TPB requirements, financial services managing AML/CTF obligations, and professional services onboarding new clients, the question isn’t whether to adopt biometric verification, it’s how to implement it without disrupting existing workflows. The technology itself is sophisticated, involving everything from facial recognition algorithms to liveness detection that spots presentation attacks. Understanding these mechanisms helps you evaluate solutions and meet your compliance obligations with confidence.
This guide breaks down how biometric identity verification actually works, from the technical processes behind document and facial matching to the regulatory framework governing its use in Australia. Whether you’re exploring verification options or looking to integrate identity checks directly into your CRM through platforms like StackGo’s IdentityCheck, you’ll find the practical knowledge needed to make informed decisions about protecting your business and your clients.
What biometric identity verification means
Biometric identity verification compares your physical characteristics against a known reference to confirm your identity. The process captures a measurable biological trait, such as your facial features or fingerprint pattern, converts it into digital data, and matches it against a previously verified sample. Unlike knowledge-based authentication (passwords, PINs) or possession-based methods (ID cards, tokens), biometrics verify something inherent to you that cannot be transferred, shared, or easily replicated.
The technology relies on two distinct processes working together. First, enrollment captures your biometric data and creates a mathematical template, a numerical representation of your unique characteristics. Later, authentication captures a fresh biometric sample and compares it against the stored template to determine whether you are the same person. When you submit a selfie to verify your identity online, the system isn’t storing your photo itself but rather specific measurements derived from that image, such as the distance between your eyes or the shape of your jawline.
The strength of biometric verification lies in its ability to link a digital identity to a specific physical person, creating an audit trail that’s far more reliable than usernames and passwords alone.
The three components that power verification
Your biometric verification system processes identity through three interconnected stages. Biometric capture records your physical trait using specialised hardware or standard devices like smartphone cameras. This stage determines data quality, and poor lighting or low-resolution cameras can compromise the entire verification process. Modern systems use liveness detection during capture to ensure they’re reading from a living person rather than a photograph or video replay.
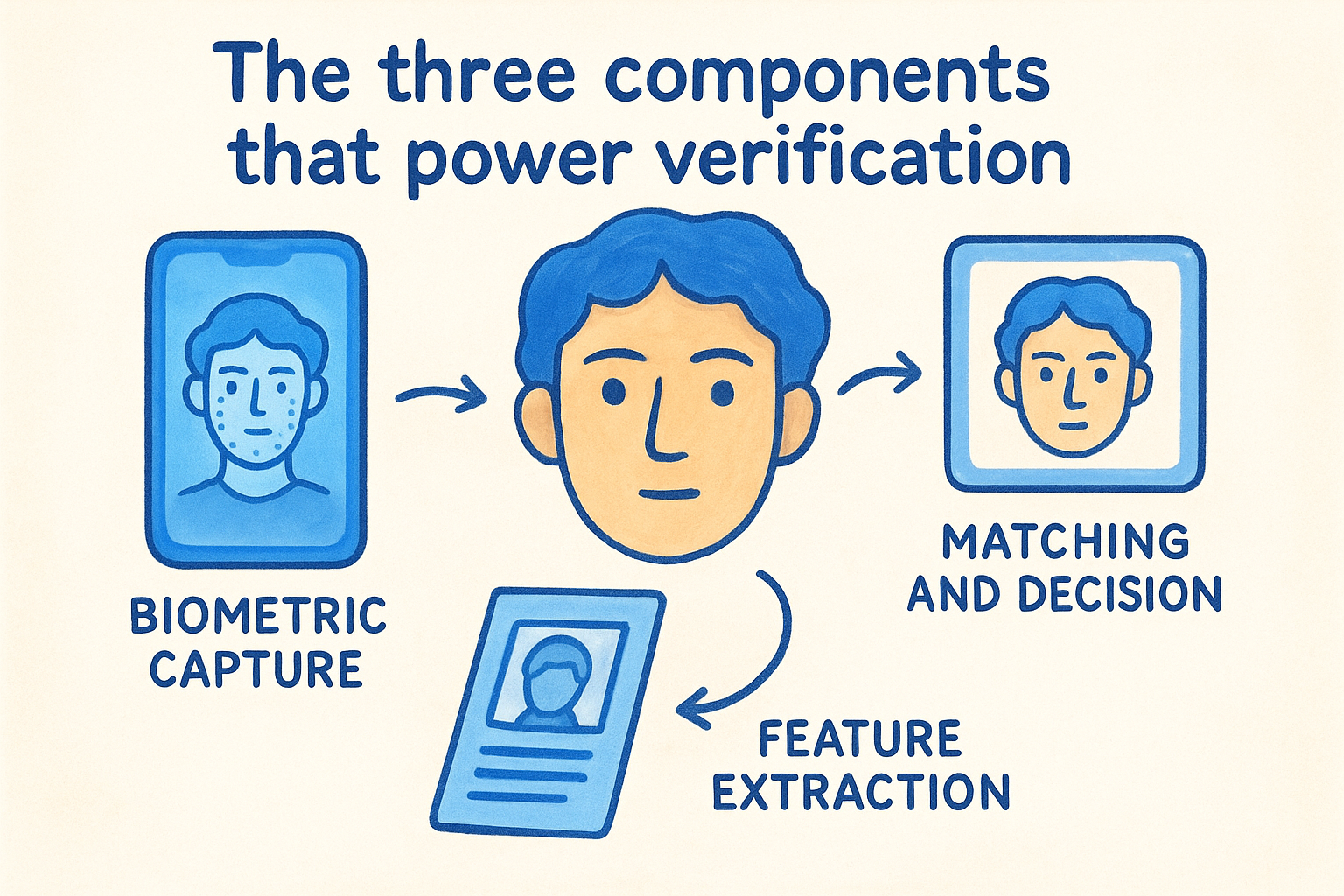
Feature extraction follows capture, where algorithms identify and measure distinctive characteristics from the biometric sample. For facial recognition, this might include the geometry of your facial structure, the position of your eyes relative to your nose, and the contours of your cheeks. The system converts these measurements into a mathematical template, typically a string of numbers that represents your unique biometric signature. This template is what gets stored and compared, not your actual image.
Matching and decision completes the process by comparing the newly captured template against reference templates in the database. The system calculates a similarity score and determines whether it exceeds the threshold required for a positive match. You can adjust this threshold based on your security requirements: stricter thresholds reduce false acceptances but increase false rejections, while lenient thresholds do the opposite.
How it differs from document verification
Document verification examines government-issued credentials like passports or driver’s licences to confirm identity details. You check security features, validate formatting, and cross-reference information against official databases. Biometric identity verification adds a critical layer by confirming the person presenting the document is the same person to whom it was issued. Someone might possess a genuine passport obtained through identity fraud, but they cannot replicate the biometric traits of the legitimate document holder.
This combination creates what’s known as identity binding. When you verify both the document and the person’s biometrics simultaneously, you establish a much stronger link between the physical individual and their claimed identity. Australian regulators increasingly expect this layered approach, particularly for remote onboarding where you cannot physically inspect documents or meet the person face-to-face. The biometric component transforms document verification from a check of credentials into a verification of the person themselves.
Biometric methods also offer operational advantages over traditional verification approaches. Passwords can be guessed or phished, security questions can be researched on social media, and physical tokens can be stolen. Your fingerprint or facial structure remains with you, cannot be forgotten at home, and requires your physical presence to verify. This inherent connection between identity and individual makes biometric verification particularly valuable for organisations managing sensitive transactions or restricted access.
Why it matters for Australian organisations
Australian organisations face mounting pressure to verify identities reliably and efficiently. Regulatory requirements continue to tighten across financial services, accounting, legal, and professional sectors, with penalties for non-compliance reaching hundreds of thousands of dollars. Your ability to implement robust identity verification directly affects your legal standing, operational costs, and reputation. The shift toward digital-first service delivery means you can no longer rely on face-to-face document checks to establish client identity, creating both risk and opportunity in how you structure your onboarding processes.
Regulatory pressure is intensifying
AML/CTF obligations under the Anti-Money Laundering and Counter-Terrorism Financing Act 2006 require reporting entities to verify customer identities using reliable and independent documentation. AUSTRAC expects you to implement verification processes that detect fraudulent documents and stolen identities, and biometric identity verification meets these standards by confirming the person presenting documents is their legitimate holder. The Tax Practitioners Board similarly mandates identity verification protocols for accountants and tax agents, with compliance obligations extending to client onboarding and ongoing due diligence.
When your verification process can demonstrate both document authenticity and biometric matching, you create an audit trail that satisfies regulatory scrutiny and protects your business from enforcement action.
Financial institutions face additional layers of oversight through APRA’s prudential standards, which emphasise operational resilience and fraud prevention. Your verification framework forms part of this broader risk management structure, and inadequate identity checks expose you to regulatory censure, financial penalties, and potential licence restrictions. Privacy regulations under the Privacy Act 1988 add complexity by requiring you to handle biometric data as sensitive information, demanding explicit consent and stronger security controls.
Cost of identity fraud keeps climbing
Identity fraud cost Australian businesses and individuals $3.1 billion in 2021, with synthetic identities and document forgery representing the fastest-growing attack vectors. You absorb these losses through fraudulent transactions, remediation costs, and increased insurance premiums. Manual verification processes leave gaps that fraudsters exploit, particularly when your staff lack specialised training in document security features or cannot detect sophisticated forgeries. Biometric verification closes these gaps by adding a layer of authentication that’s exponentially harder to fake.
Remote operations demand stronger verification
Hybrid service delivery requires you to onboard clients without in-person meetings, creating new vulnerabilities in your identity assurance processes. Video calls and emailed document scans offer convenience but introduce uncertainty about whether you’re dealing with the genuine client or an impersonator. Biometric identity verification provides the technical controls needed to establish identity remotely with confidence comparable to face-to-face verification, enabling you to expand service offerings without compromising security or compliance standards.
How biometric verification works step by step
Biometric identity verification follows a predictable sequence of technical operations, each designed to capture, process, and compare your physical characteristics against stored data. You implement this process through three distinct phases that work together to establish identity with precision. Understanding these stages helps you evaluate vendor capabilities, identify potential failure points, and design verification workflows that balance security with user experience. The technology operates consistently whether you’re onboarding a new client or authenticating an existing one, though the specific biometric methods and thresholds may vary based on your risk appetite.
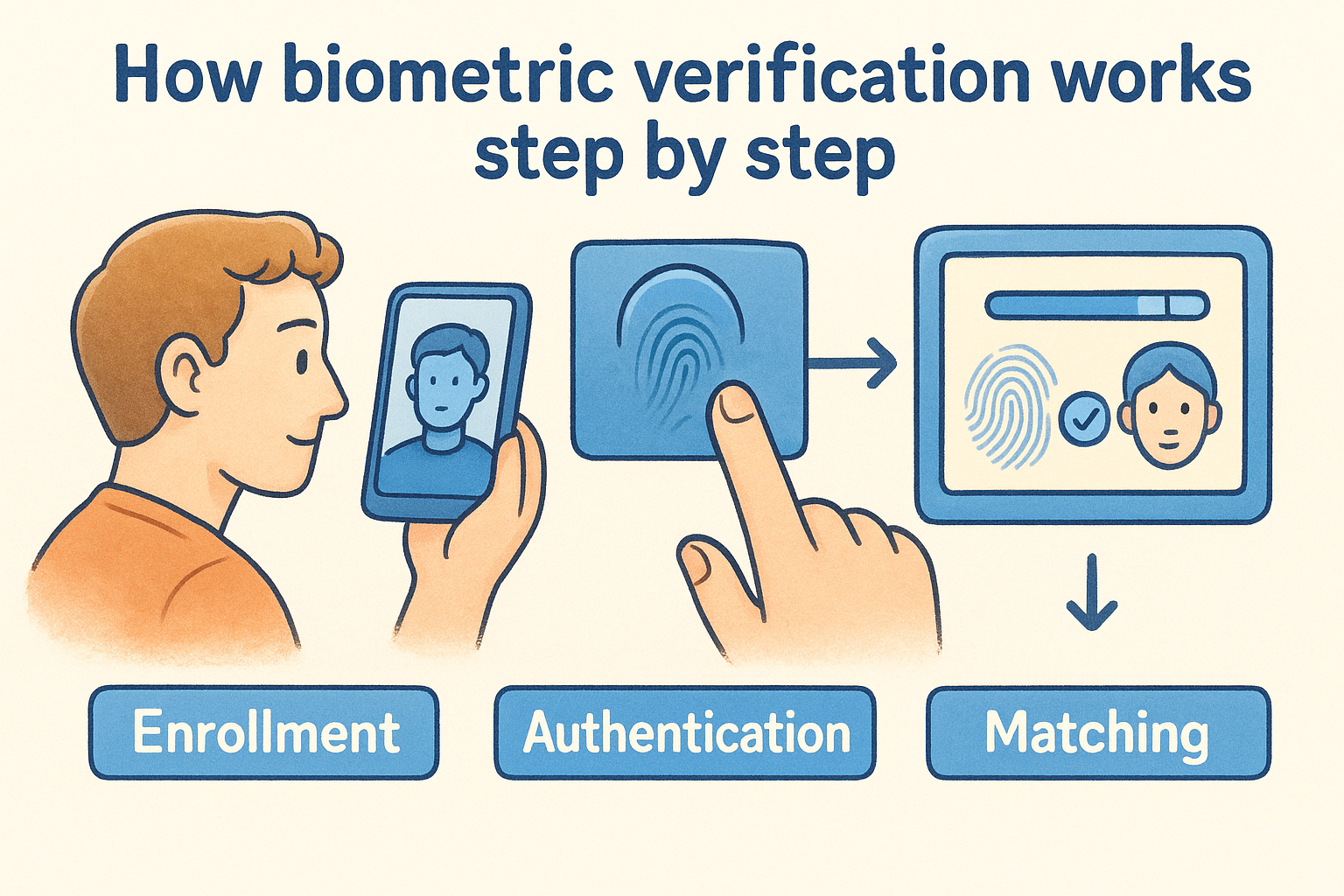
Enrollment captures and stores your biometric template
Your verification system begins by capturing a high-quality sample of the biometric trait during enrollment. You or your client present the required biometric, whether that’s looking into a camera for facial recognition or placing a finger on a scanner. The system records this data and immediately processes it to extract distinctive features, converting your physical characteristics into a mathematical template. This template becomes the reference point for all future verification attempts.
During enrollment, the system also collects supporting identity documents to bind the biometric template to a specific person. You verify the document’s authenticity, extract identity details like name and date of birth, and link these to the biometric template in your database. This creates an identity record that combines both who you claim to be (document data) and proof of your physical presence (biometric template). The system never stores your raw biometric image, only the numerical representation derived from it, which protects privacy while maintaining verification capability.
Authentication compares new samples against stored templates
When you return for verification, the system captures a fresh biometric sample using the same method employed during enrollment. Your smartphone camera records your face, or a fingerprint scanner reads your print. The system extracts features from this new sample and converts them into a comparable template using identical algorithms to ensure consistency. This authentication template must match the mathematical structure of your enrollment template despite minor variations in lighting, angle, or environmental conditions.
Quality controls during both enrollment and authentication determine whether your verification system delivers reliable results or generates frustrating false rejections.
The matching engine calculates similarity and makes decisions
Your verification system compares the authentication template against the stored enrollment template using pattern-matching algorithms that calculate a similarity score. This score represents how closely the two templates align, typically expressed as a percentage or numerical value. You configure a threshold that determines when a match is accepted, rejected, or requires manual review. Setting this threshold too high creates friction through false rejections, while setting it too low allows potential impostors through.
The system applies liveness detection throughout this process to confirm you’re capturing biometric data from a living person rather than a photograph, video, or synthetic replica. Modern platforms use multiple liveness checks, including detecting natural eye movement, requesting specific facial gestures, or analysing texture patterns that distinguish real skin from printed images. Your verification decision combines both the similarity score and these liveness results to produce a final accept or reject outcome.
Common biometric methods used in Australia
Australian organisations deploy several biometric modalities depending on their verification requirements, risk profiles, and service delivery channels. You select methods based on factors like accuracy needs, user convenience, hardware availability, and regulatory expectations. Facial recognition dominates remote identity verification due to widespread smartphone camera access, while fingerprint scanning remains prevalent in physical access control and point-of-service authentication. Understanding each method’s strengths and limitations helps you design verification processes that align with your operational context and client expectations.
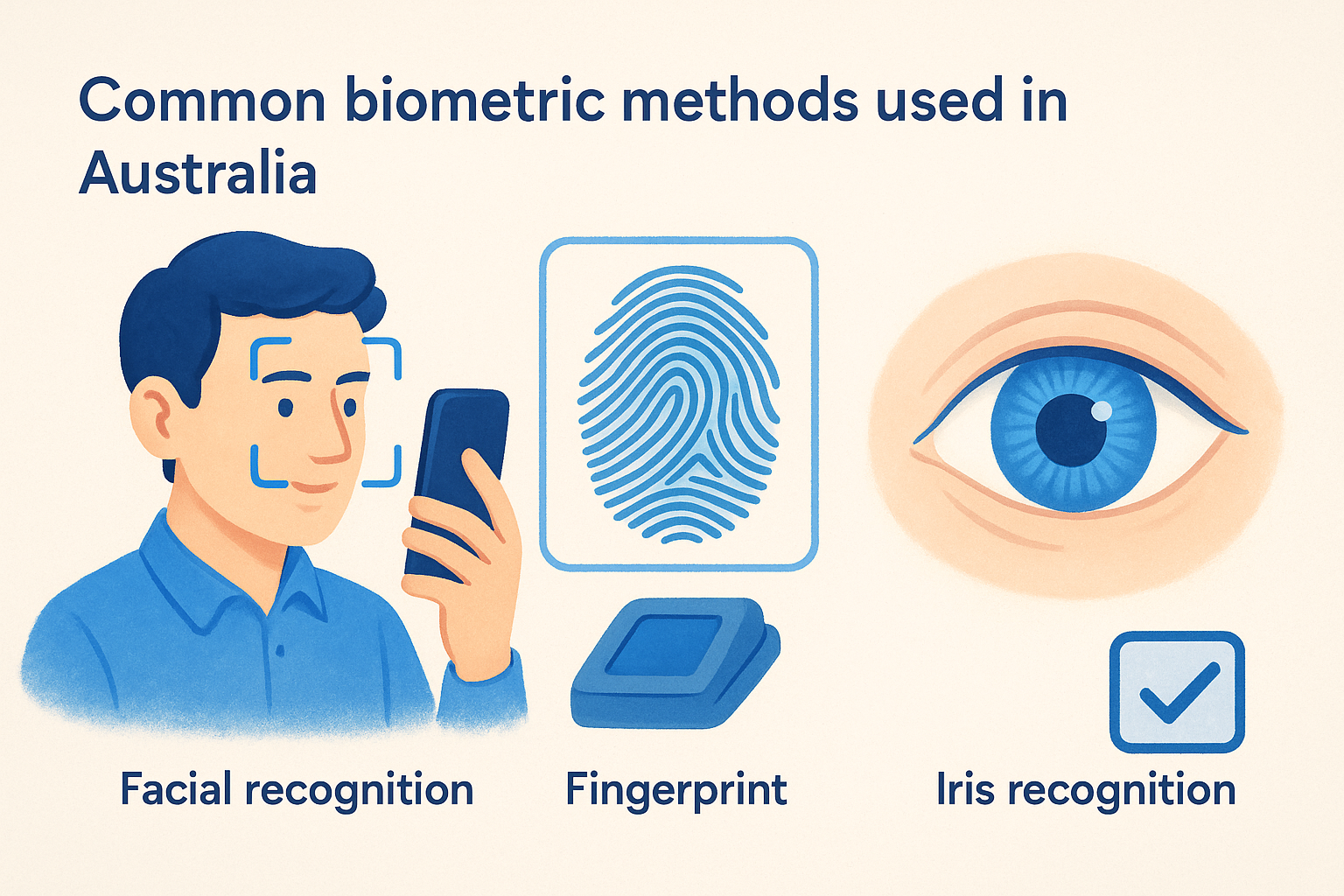
Facial recognition dominates digital onboarding
Facial recognition technology captures your face through a standard camera and compares it against government-issued photo identification. You present your passport or driver’s licence, then record a selfie or live video that the system matches against the document photo. This method works across mobile devices, tablets, and desktop computers without requiring specialised hardware, making it the most accessible option for remote client onboarding. Financial institutions, accounting firms, and professional services providers rely on facial recognition to meet AML/CTF obligations when you cannot verify clients in person.
The technology extracts facial landmarks like eye position, nose shape, and jawline contours to create your biometric template. Modern systems incorporate liveness detection that asks you to blink, turn your head, or follow on-screen prompts to confirm you’re a living person rather than a photograph or video replay. Your verification typically completes within seconds, and success rates exceed 95% when you provide good lighting and follow positioning instructions.
Facial recognition’s combination of convenience, accuracy, and compatibility with existing devices explains why it’s become the default biometric method for Australian digital identity verification.
Fingerprint scanning for physical access
Fingerprint recognition analyses the unique ridge patterns on your fingertips to verify identity. You place your finger on a specialised scanner that captures an image of your print, which the system converts into a template highlighting minutiae points where ridges end, fork, or form patterns. Banks use fingerprint scanners at branches for customer authentication, while corporate offices deploy them for physical access control and time attendance systems.
Fingerprint verification delivers exceptional accuracy with false acceptance rates below 0.001% when implemented correctly. You benefit from fast authentication times, typically under two seconds, and the technology works reliably across diverse populations. Hardware costs have dropped significantly, with quality scanners available for under $200, making fingerprint recognition economically viable for small and medium organisations.
Voice and iris verification in niche applications
Voice biometrics analyses your unique vocal characteristics, including pitch, tone, and speech patterns, to verify identity. Call centres deploy this technology for phone-based customer authentication, allowing you to verify identity through natural conversation rather than answering security questions. Iris recognition scans the distinctive patterns in your eye’s coloured ring, offering accuracy comparable to fingerprint scanning but requiring specialised cameras that limit deployment to high-security environments like data centres and government facilities.
What the law says in Australia
Australian law treats biometric data as sensitive information requiring stronger protections than standard personal data, and you face specific obligations when collecting, storing, and using biometric templates for verification purposes. The Privacy Act 1988 establishes the baseline framework through the Australian Privacy Principles (APPs), while sector-specific legislation adds layers of compliance requirements depending on your industry. Understanding these legal obligations helps you implement biometric identity verification systems that satisfy regulators while protecting your clients’ personal information.
The Privacy Act defines your obligations
You must obtain explicit consent before collecting biometric data under APP 3, which requires you to inform clients about what biometric information you’re collecting, why you need it, and how you’ll use it. Your privacy notice cannot hide these details in lengthy terms and conditions; you provide clear, prominent disclosure at the point of collection. APP 11 mandates security safeguards appropriate to the sensitivity of biometric data, meaning you implement encryption, access controls, and regular security assessments that exceed protections for standard personal information.
Biometric templates qualify as sensitive information under section 6 of the Privacy Act, triggering stricter handling requirements than ordinary identity data. You restrict access to biometric data on a need-to-know basis, maintain detailed logs of who accesses this information, and implement technical controls that prevent unauthorised disclosure. When you engage third-party verification providers, your organisation remains accountable for their handling of client biometric data under APP 1.
Your biometric verification system must demonstrate that you’ve implemented privacy by design principles from the outset, not retrofitted privacy protections after deployment.
AML/CTF requirements for verification
The Anti-Money Laundering and Counter-Terrorism Financing Act 2006 requires reporting entities to verify customer identity using reliable and independent sources, and biometric identity verification satisfies these requirements when combined with document checks. AUSTRAC expects you to implement customer identification procedures that detect fraudulent documents and confirm the person presenting identification is its rightful owner, which biometric matching achieves through facial comparison against government-issued photo identification.
You design verification processes that create audit trails demonstrating compliance with AML/CTF obligations, including records of verification methods used, results obtained, and decisions made. These records support your reporting obligations and provide evidence during AUSTRAC audits or investigations.
Industry-specific regulations add compliance layers
Tax practitioners operating under TPB registration face identity verification requirements when establishing client relationships, with the Tax Practitioners Board expecting verification standards comparable to AML/CTF obligations. Financial services firms must satisfy APRA prudential standards that emphasise operational risk management and fraud prevention, where inadequate identity verification constitutes a material operational weakness. State-based licensing regimes for legal practitioners, real estate agents, and other professionals incorporate identity verification requirements that biometric systems help you satisfy efficiently.
Privacy, security and fairness risks to plan for
Biometric identity verification introduces distinct risks that differ fundamentally from traditional authentication methods. You cannot reset your fingerprint or facial features if they’re compromised, making security failures with biometric data far more consequential than password breaches. Australian organisations implementing these systems face privacy obligations under the Privacy Act, potential discrimination claims if algorithms perform unevenly across demographics, and reputational damage if data handling practices fail to meet community expectations. Planning for these risks before deployment protects both your clients and your business from preventable harm.
Data breach exposure multiplies with biometric storage
Stolen biometric templates create permanent identity risks for affected individuals because they cannot change their physical characteristics like they would reset a password. You implement robust encryption for biometric data both at rest and in transit, restrict access to templates through role-based controls, and maintain detailed audit logs of who accesses this information. Your security architecture should prevent biometric templates from leaving secure storage environments, with matching operations performed within protected systems rather than transmitting templates across networks.
Regular penetration testing identifies vulnerabilities in your biometric storage and processing infrastructure before attackers exploit them. You engage qualified security professionals to assess your systems quarterly, remediate identified weaknesses within defined timeframes, and document all security measures for regulatory review. Third-party verification providers must demonstrate equivalent security standards through certifications like ISO 27001 or SOC 2 Type II before you entrust them with client biometric data.
Your obligation to protect biometric data extends beyond preventing breaches to ensuring you can detect and respond to security incidents within hours rather than weeks.
Algorithmic bias affects accuracy across demographics
Facial recognition algorithms historically demonstrate higher error rates for women, people with darker skin tones, and certain ethnic groups compared to white males. You test your biometric systems across representative demographic samples during procurement, monitor false rejection and false acceptance rates by demographic category during operations, and switch providers if accuracy disparities emerge. These performance gaps create discrimination risks under the Racial Discrimination Act 1975 and Sex Discrimination Act 1984 if your verification process systematically disadvantages protected groups.
Quality standards for biometric capture help mitigate algorithmic bias by ensuring consistent lighting, positioning, and image resolution across all users. You provide clear instructions during capture, offer multiple attempts when verification fails, and maintain human review processes for borderline cases where automated matching produces uncertain results.
Consent and transparency requirements create legal exposure
You obtain explicit informed consent before collecting biometric data, explaining what you’re collecting, how you’ll use it, and when you’ll delete it. Your consent mechanism cannot bundle biometric permissions with other service terms; you present them separately and allow clients to proceed only after acknowledging the specific biometric collection. Withdrawal rights must remain accessible, enabling clients to revoke consent and request deletion of their biometric templates without losing access to your services entirely.
How to implement biometric verification in your stack
Successful biometric identity verification implementation requires more than selecting a vendor and flipping a switch. You integrate verification directly into your existing workflows, configure security parameters that match your risk appetite, and test thoroughly before exposing clients to a new identity process. The difference between smooth adoption and frustrated abandonment lies in how well you align technical capabilities with your operational reality and client expectations.
Choose integration over standalone systems
Your verification platform should operate within your CRM or practice management software rather than forcing you to switch between multiple applications. Staff adoption collapses when they must log into separate portals to verify client identities, copy data between systems, or manually update records across platforms. Native integrations eliminate these friction points by reading client information from your existing database, triggering verification workflows automatically, and writing results back without manual intervention.
You evaluate vendors based on their integration depth with your technology stack. Surface-level connections that require you to export CSVs or manually enter data fail to deliver meaningful efficiency gains. Look for platforms like StackGo’s IdentityCheck that embed verification capabilities directly into software you already use, maintaining your existing workflows while adding biometric security layers. Your implementation timeline shortens dramatically when you avoid building custom integrations or training staff on new interfaces.
Integration architecture determines whether biometric verification becomes a seamless security enhancement or an operational burden that staff circumvent through workarounds.
Match verification strength to your risk profile
Different clients present different risk levels, and your verification requirements should adjust accordingly. You implement risk-based authentication that applies stricter biometric checks for high-value transactions or sensitive services while using streamlined verification for routine interactions. AML/CTF obligations demand enhanced due diligence for certain client categories, which you satisfy through additional biometric checks beyond standard facial recognition.
Configuration options let you set matching thresholds that balance security against user experience. Tighter thresholds reduce false acceptances but increase legitimate rejections, while looser settings improve convenience at the expense of security. You test different threshold configurations during implementation to find the optimal balance for your client demographics and risk tolerance.
Test with real users before full deployment
Your verification system performs differently in production than in controlled testing environments. You conduct pilot programmes with select staff members and cooperative clients who provide feedback on the experience before rolling out biometrically verified onboarding organisation-wide. These trials identify usability issues like confusing instructions, inadequate lighting guidance, or technical problems with specific device types that you address before broader deployment.
Monitor completion rates and abandonment points during testing to understand where clients struggle. You refine capture instructions, adjust lighting requirements, or simplify the verification flow based on observed behaviour rather than assumptions about user capability.
Where to go next
You now understand how biometric identity verification operates technically, legally, and practically within Australian organisations. The technology delivers stronger identity assurance than document checks alone, and regulatory expectations continue pushing toward biometric-enhanced verification across professional services, financial institutions, and accounting practices.
Implementation success depends on integration architecture rather than verification accuracy alone. Your staff need verification capabilities embedded directly into existing systems like your CRM or practice management platform, not standalone portals that add complexity. StackGo’s IdentityCheck operates inside software you already use, reading client details, verifying identities through facial biometrics and document checks, then writing results back without manual data entry or context switching.
Australian accounting firms face upcoming AUSTRAC Tranche 2 obligations requiring enhanced client verification for AML/CTF compliance. Learn how IdentityCheck handles Tranche 2 requirements within your existing stack or create a free account to test the solution with your current client data before full deployment.









