Every year, businesses across Australia and globally lose billions to fraud, from falsified identities during client onboarding to sophisticated synthetic identity schemes that slip past outdated checks. The stakes are especially high for regulated industries like accounting, legal, and financial services, where a single compliance failure can trigger penalties, reputational damage, and lost client trust. Understanding fraud detection methods is no longer optional; it’s a core part of running a compliant and operationally sound business.
The challenge is that fraud doesn’t stand still. Techniques evolve constantly, and the methods used to catch them need to keep pace. That means going beyond gut instinct and manual review to adopt structured detection strategies, spanning statistical analysis, rule-based systems, machine learning, and real-time identity verification. For businesses already juggling multiple platforms and compliance obligations, knowing which tools and techniques actually work (and how they fit together) is critical to reducing risk without adding operational complexity.
At StackGo, we build integration tools like IdentityCheck that bring identity verification and KYC/AML checks directly into your existing software stack, no tab-switching, no standalone portals, no duct-taped automations. Fraud prevention starts at the point of onboarding, and that’s where our platform sits. This article breaks down the major fraud detection techniques, tools, and practices used across industries, so you can evaluate what applies to your business and where the gaps in your current processes might be.
Why fraud detection matters for Australian businesses
Australian businesses face a fraud environment that is growing in both volume and sophistication every year. The Australian Competition and Consumer Commission reported that Australians lost over $2.7 billion to scams in 2023 alone, and that figure doesn’t capture the full picture. Fraud occurring within business operations, such as identity fraud during client onboarding, invoice manipulation, and insider threats, adds significantly to that cost. For regulated industries like accounting, financial services, and legal services, the risk is compounded by strict compliance obligations that carry real financial and reputational consequences when fraud goes undetected.
The regulatory pressure on Australian firms
The regulatory landscape in Australia has shifted considerably, and if you operate in a professional services firm, you need to understand the obligations now sitting on your practice. The Tax Practitioners Board (TPB) already requires registered tax agents to implement robust client verification procedures. AUSTRAC’s expanded Anti-Money Laundering and Counter-Terrorism Financing reforms are pulling more professional service providers into the compliance net, and from 2026, accountants, lawyers, and real estate agents will be subject to mandatory AML/CTF obligations for the first time. That turns fraud detection methods from a best practice into a legal requirement with enforcement consequences attached.
If your firm falls within the scope of the new AML/CTF reforms, the question is not whether to implement fraud detection, it’s how to do it without disrupting your existing workflows.
Failing to meet these obligations puts you at direct risk of AUSTRAC enforcement action, which can include substantial civil penalties and public naming. Beyond the immediate financial hit, a regulatory breach signals to clients, referral partners, and insurers that your internal controls are insufficient. That kind of reputational damage can affect client retention and new business for years.
The operational cost of getting it wrong
Fraud doesn’t only cost money at the point it occurs. When your onboarding process lacks thorough identity verification, you risk accepting clients who are using false identities, or who appear on international sanctions lists or Politically Exposed Person registers. The downstream consequences include involvement in money laundering activity, exposure to civil litigation, and the cost of unwinding client relationships, all of which consume significant staff time and legal resources.
Manual review compounds the problem further. If your team is checking identity documents by hand, chasing clients for paperwork over email, and logging outcomes in spreadsheets, errors build up over time. A single missed check or an expired document can create a compliance gap that fraudsters exploit. Embedding structured detection directly into your existing systems reduces these errors at the source and makes your compliance position far easier to defend and demonstrate to regulators.
How fraud detection works end to end
Effective fraud detection methods don’t operate as a single checkpoint. They run as a continuous pipeline spanning multiple stages, from the moment a new client contacts your business through to ongoing monitoring after onboarding is complete. Understanding each stage helps you identify where your current process has gaps and where targeted automation can do the heavy lifting.
Stage 1: Identification, data collection, and risk scoring
The process starts by collecting reliable identity data about the person or entity you are dealing with. This means capturing government-issued documents, verifying them against authoritative databases, and screening the individual against sanctions lists, Politically Exposed Person registers, and adverse media sources. You are establishing, at the earliest point possible, that the person is who they claim to be.
Once the data is in, your systems need to evaluate and score the risk. This involves comparing incoming information against known fraud indicators, flagging anomalies like address mismatches or document inconsistencies, and applying rule-based logic or machine learning models to generate a risk rating. Low-risk results move forward automatically. High-risk results trigger manual review or additional verification steps.
Building risk scoring into your onboarding workflow means your team only spends time on cases that genuinely need human attention.
Stage 2: Investigation, decision, and ongoing monitoring
When a flagged case reaches your team, a structured investigation workflow takes over. That means reviewing the evidence, documenting your reasoning, and recording the outcome in a way that creates a clear audit trail for regulators if they ever ask.
Fraud detection also continues well past onboarding. Periodic re-verification and transaction monitoring ensure that clients who passed initial checks are not engaging in suspicious activity over time, and that your compliance position reflects the current risk, not just the risk at the point of client sign-up.
Core fraud detection methods and when to use them
No single fraud detection method suits every situation. The right approach depends on your risk profile, industry obligations, and client volume. Most effective programmes combine several methods across the client lifecycle rather than relying on any one technique in isolation.
Rule-based detection
Rule-based systems apply predefined logic to flag activity matching known fraud patterns, such as address mismatches or duplicate identity submissions. These systems are fast to deploy and easy to audit, which suits firms that need a transparent, defensible compliance record.
The limitation is that rules are static by design. They catch what you have already anticipated, not new fraud patterns that emerge over time, which makes them most effective when combined with a second, adaptive detection layer.
Pairing rule-based systems with a second detection layer gives you both speed and adaptability.
Machine learning and behavioural analysis
Machine learning models detect anomalies that no predefined rule would catch. They learn what normal looks like for your client base and flag deviations such as atypical document submission patterns or unusual transaction sequences. These models improve over time, making them effective when manual review at scale is impractical.
For smaller firms, simpler statistical threshold monitoring can deliver similar benefits without the infrastructure overhead of a full machine learning deployment.
Identity verification and document screening
Identity verification sits at the front of your fraud defence. It confirms that the person onboarding is who they claim to be by checking documents against authoritative databases and screening against sanctions lists and Politically Exposed Person registers.
Australian accounting and financial services firms need this step to satisfy both a practical fraud control requirement and their obligations under TPB and forthcoming AUSTRAC reforms. Running checks through your existing CRM removes the friction of standalone portals and ensures nothing slips through.
Building a layered fraud programme that holds up
A single fraud detection method, no matter how sophisticated, creates a single point of failure. Effective programmes stack multiple detection controls at different points in the client lifecycle so that if one layer misses something, the next one catches it. The goal is not to make your process more complex but to make it harder for fraud to slip through undetected while keeping your operational burden manageable.
Layer your controls across the client lifecycle
Your first layer sits at onboarding, where identity verification and document screening confirm that a new client is who they claim to be. The second layer applies rule-based checks against known fraud patterns immediately after, flagging anomalies like mismatched details or high-risk geographies. A third layer, whether that is statistical monitoring or a machine learning model, watches for behavioural anomalies over the life of the client relationship.
Combining these layers means your team only escalates cases that genuinely warrant review. Automating the routine checks removes the manual burden while creating a cleaner audit trail for regulators, which matters considerably under the AUSTRAC reforms now applying to Australian professional service firms.
The firms that hold up best under regulatory scrutiny are those who can show exactly what was checked, when, and why a decision was made.
Keep your programme current and documented
Fraud patterns shift, so your fraud detection methods need regular review. Schedule a periodic audit of your rules and risk thresholds, and update them when new fraud typologies emerge or when your client mix changes. Document every update and its rationale so that your compliance position reflects current practice, not just the controls you set up at launch. A programme you cannot demonstrate is a programme that will not protect you.
Common challenges and how to handle them
Even a well-designed fraud programme runs into practical problems. The two most common issues are false positives that overwhelm your team and controls that stop keeping pace with how fraud evolves. Knowing how to handle both keeps your programme functional without creating new operational bottlenecks.
False positives and alert fatigue
When your detection rules or risk thresholds are set too broadly, legitimate clients get flagged alongside genuine fraud attempts. Over time, your team starts skimming alerts rather than reviewing them properly, which is exactly when real threats slip through. The fix is to calibrate your thresholds based on your actual client base rather than generic industry defaults, and to review false positive rates regularly as part of your periodic programme audit.
Tracking your false positive rate over time gives you a concrete measure of whether your detection rules are working or simply creating noise.
Segmenting your alerts by risk category and client type also helps your team prioritise where to spend their attention. Automating the routine, low-risk checks clears the queue so that human review is reserved for cases that genuinely require it.
Keeping pace with evolving fraud tactics
Fraud detection methods need updating on a consistent schedule because the tactics they are designed to catch change constantly. A rule that worked eighteen months ago may no longer reflect how fraudsters operate today. Scheduling quarterly reviews of your fraud typologies and updating your rules and monitoring thresholds accordingly keeps your controls relevant.
Connecting with industry bodies like AUSTRAC and monitoring their published guidance gives you early visibility into emerging threats before they reach your client base. That lead time lets you adjust your controls proactively rather than reacting after fraud has already occurred.
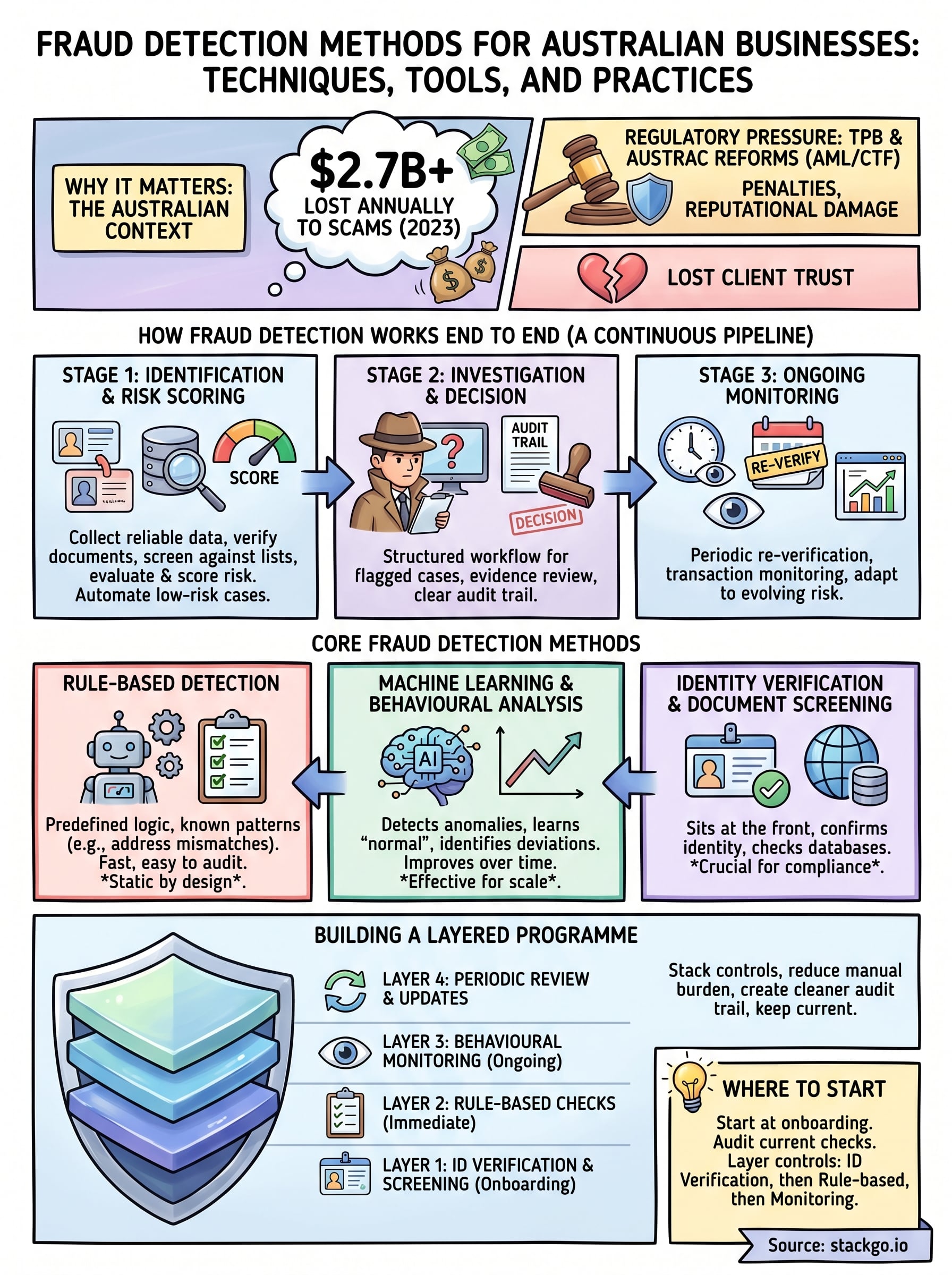
Where to start
Most firms benefit from starting at the onboarding stage, because that is where identity risk is highest and where structured fraud detection methods have the most immediate impact. Audit what your current process actually checks, where the outputs get recorded, and whether any step relies on a manual action that could be skipped under pressure. Those gaps are where fraud enters.
Once you have mapped your onboarding process, layer your controls deliberately. Start with identity verification and document screening, then add rule-based checks for known risk indicators, and build towards ongoing monitoring as your client base grows. You do not need to solve everything at once; you need a defensible, documented process that improves over time.
If your firm falls within the scope of Australia’s AML/CTF reforms, IdentityCheck runs those checks directly inside your existing software. See how IdentityCheck handles AUSTRAC Tranche 2 compliance or create a free account to test it against your current workflow.









