If your business collects client data, names, addresses, ID documents, you’re handling personal information under Australian law. The personal information definition Australia relies on comes from the Privacy Act 1988, and it’s broader than most people expect. Getting it wrong can mean regulatory penalties, reputational damage, and a serious erosion of client trust.
For regulated businesses like accounting firms, financial service providers, and legal practices, understanding this definition isn’t optional. It directly shapes how you collect, store, verify, and share client data during onboarding, KYC/AML checks, and ongoing compliance workflows. Every identity verification you run, every document you collect, it all falls under the Privacy Act’s reach.
At StackGo, we build integration tools like IdentityCheck that handle identity verification directly within your existing CRM, with a built-in privacy layer that keeps personally identifiable information out of systems where it doesn’t belong. That work starts with understanding exactly what the law considers personal information.
This article breaks down the official legal definition, walks through the types of data it covers, and explains how it applies to identifying individuals in practice.
The legal definition under the Privacy Act 1988
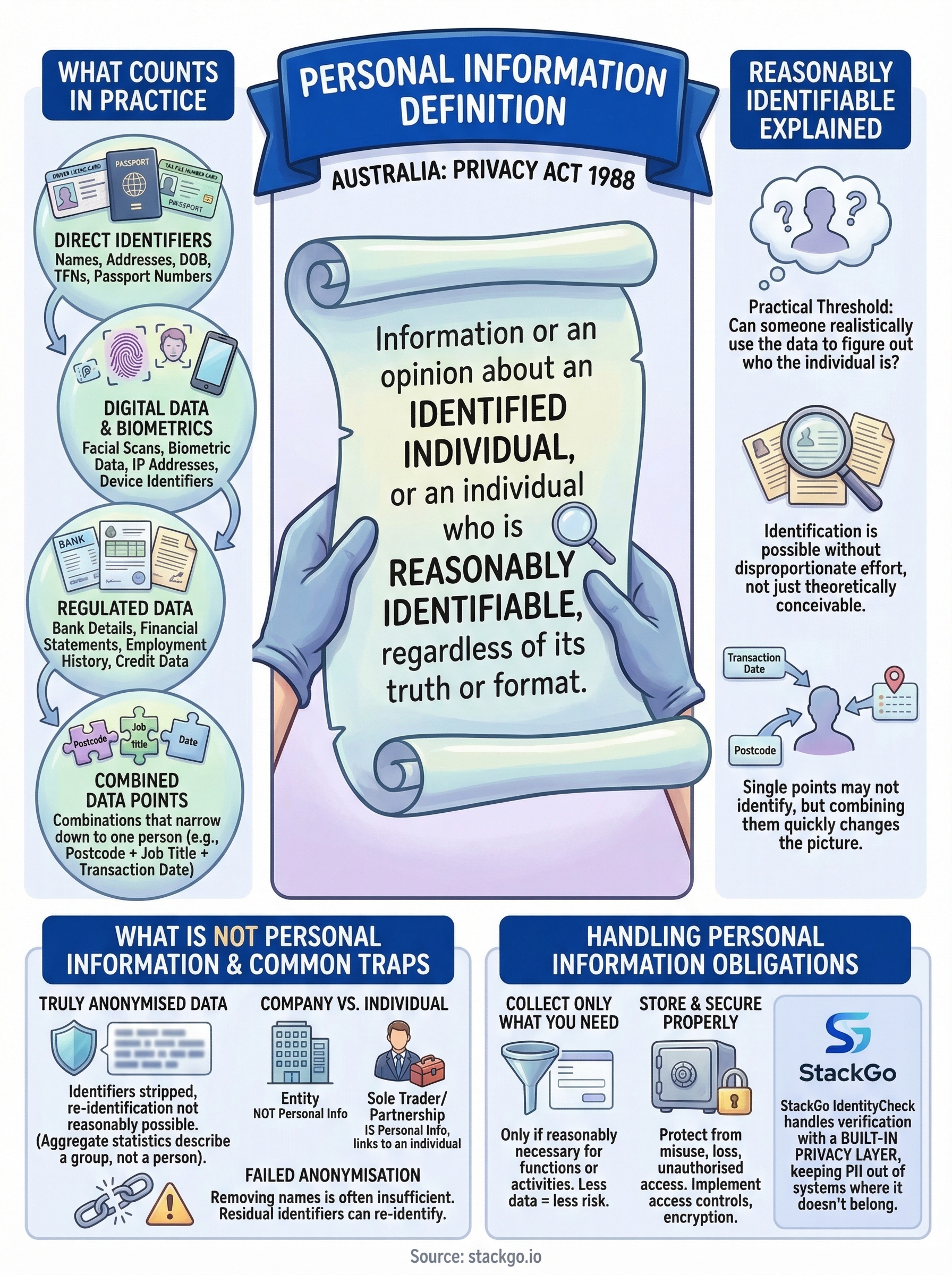
Under section 6 of the Privacy Act 1988, the Australian Government defines personal information as: information or an opinion about an identified individual, or an individual who is reasonably identifiable, whether the information is true or not, and whether it is recorded in a material form or not. That single sentence carries significant weight, and every part of it affects how your business handles client data.
The definition applies whether the information is true or not, and whether it exists in written, digital, or verbal form.
What the statutory wording actually covers
The personal information definition Australia relies on deliberately avoids a fixed list. Parliament wrote it this way so the law keeps pace with new technologies and data types, rather than becoming outdated the moment a new format appears. You cannot rule out a piece of data simply because it doesn’t appear on a checklist.
Any format qualifies under this definition, including digital records, handwritten notes, photographs, and audio recordings. If your staff discuss a client’s financial situation in a meeting, that conversation technically falls within scope even though nothing was written down.
The ‘about an individual’ requirement
For data to qualify, it must be about a specific person, not just related to a business or property. A company’s ABN sits outside the definition. However, a sole trader’s ABN links directly to an individual, which pulls it straight back into scope.
This distinction matters during client onboarding. When you collect data on a business contact, assess whether that data identifies the person behind the business, not just the entity itself. Getting this wrong during KYC or AML workflows is a compliance risk, not merely a technical oversight.
What counts as personal information in practice
The personal information definition Australia relies on under the Privacy Act covers a wide range of data types. Names, email addresses, phone numbers, and physical addresses all qualify. So do tax file numbers, dates of birth, passport numbers, and driver’s licence details. If you run identity verification checks as part of your client onboarding process, virtually every field you collect falls within scope.

Common examples in regulated industries
Accounting firms, financial services providers, and legal practices regularly collect bank account details, financial statements, and certified proof of identity documents during onboarding. All of that is personal information. You also need to consider employment history, income figures, and credit-related data if your KYC or AML workflows draw on that type of information during client screening.
The Privacy Act covers information regardless of whether it is accurate, so even an incorrect address on file for a client is still treated as personal information.
Data types that catch businesses off guard
Beyond the obvious identifiers, photographs and biometric data such as facial scans used in digital identity verification are personal information. So are IP addresses and device identifiers when they can be linked back to a specific individual. If your client portal or verification platform logs these as part of an authentication step, your privacy obligations apply to that data in exactly the same way they apply to a name or address.
What does ‘reasonably identifiable’ mean
The phrase "reasonably identifiable" is the part of the personal information definition Australia relies on that trips up most businesses. It means you do not need to know exactly who someone is right now. If there is a reasonable chance that someone could work out who the individual is by using the data you hold, combined with other information they could access, then that individual is reasonably identifiable. The test is not whether you intend to identify them, but whether identification is realistically possible.
"Reasonably" sets a practical threshold: identification must be possible without disproportionate effort, not merely theoretically conceivable.
When combined data tips the balance
A single data point might not identify anyone on its own. A postcode, a job title, or a transaction date in isolation tells you very little. But when you combine several of these fields, the picture changes quickly. Two or three data points together can narrow a dataset down to one person, which means the whole collection becomes personal information the moment that link is achievable.
This is especially relevant when your business integrates data across platforms, such as pulling CRM contact records into a verification workflow. Each platform might hold partial data, but once your integration connects those fields, the combined output likely qualifies as personal information and your Privacy Act obligations apply immediately.
What is not personal information and common traps
Not every piece of data your business holds qualifies as personal information under the Privacy Act. Truly anonymised data, where all identifiers have been stripped and re-identification is not reasonably possible, falls outside the definition. Aggregate statistics such as the total number of clients in a postcode also sit outside scope because they describe a group rather than an identifiable person. Understanding these boundaries helps you apply the personal information definition Australia relies on correctly, without over-managing data that carries no genuine privacy risk.
Anonymisation only works when re-identification is not reasonably achievable, not just unlikely in your own hands.
When anonymisation genuinely fails
Many businesses assume that removing a name makes data anonymous. It rarely does. Residual identifiers such as account numbers, transaction timestamps, and location data often remain in the dataset. When combined with external sources, these fields can re-identify an individual, pulling the data back within scope of the Privacy Act’s personal information definition. Common examples of data that appears anonymous but often is not:
- Transaction records with unique timestamps
- Location data tied to a specific address
- Account numbers linked to an external system
The company versus individual trap
Company names, business addresses, and corporate ABNs do not qualify as personal information on their own. The Privacy Act targets individuals, not entities.
However, this changes immediately when you deal with a sole trader or a partnership, because those structures link directly to named individuals. Review your onboarding templates and flag any fields that capture the person behind the business.
How to handle personal information in your business
Once you understand the personal information definition Australia relies on, you need to translate that understanding into practical steps across your operations. The Privacy Act 1988 does not just define what personal information is; it also sets out obligations for how you collect, store, use, and disclose it. Failing to build these obligations into your daily workflows creates real compliance exposure, particularly for regulated industries like accounting, legal services, and financial advice.
Collect only what you need
The Australian Privacy Principles (APPs) within the Privacy Act require you to collect personal information only if it is reasonably necessary for your functions or activities. Before you add a field to your onboarding form, ask whether you actually need that data to complete the client relationship. Collecting less data means less risk, fewer storage obligations, and a simpler compliance position overall.
Common fields to question during onboarding include:
- Copies of identity documents beyond what your KYC obligations actually require
- Financial details outside the scope of the specific service you provide
- Date of birth where age verification is not part of your process
Store and secure it properly
After you collect personal information, you are responsible for protecting it from misuse, loss, and unauthorised access. That means access controls, encryption where appropriate, and clear retention policies that specify when data gets deleted.
If you run identity verification within your CRM, make sure personally identifiable information does not persist in fields where it has no business being stored.
StackGo’s IdentityCheck keeps verification data out of your CRM entirely, with a privacy layer that limits access to MFA-authenticated admins only.
Final takeaway
The personal information definition Australia relies on under the Privacy Act 1988 is deliberately broad. It covers any information about an identified or reasonably identifiable individual, regardless of format, accuracy, or whether you intended to identify anyone. Names, tax file numbers, biometric data, and even combinations of seemingly innocuous fields can all fall within scope, and your obligations apply the moment you collect that data.
For regulated businesses handling client onboarding, KYC checks, or AML compliance, this is not abstract theory. Every verification you run and every document you collect carries legal weight. That means your workflows, your storage practices, and your integrations all need to reflect these obligations in practice, not just in policy.
If you want to run identity verification without accumulating personal information in places it should not be, see how IdentityCheck handles AUSTRAC compliance inside your existing software.









