Jumio is one of the more recognisable names in identity verification, and if you’ve been researching compliance solutions, there’s a good chance Jumio KYC has appeared on your shortlist. The platform uses AI-powered document verification and biometric checks to help businesses confirm that their customers are who they claim to be, a critical step for meeting Know Your Customer (KYC) and Anti-Money Laundering (AML) obligations.
For regulated businesses, accountants, financial services firms, legal practices, choosing the right verification provider has real consequences. A clunky or disconnected tool slows down client onboarding, frustrates your team, and creates compliance gaps. Jumio aims to solve part of that problem with automated identity checks across thousands of document types and over 200 countries, but understanding exactly what it offers (and where it falls short) matters before you commit.
At StackGo, we build integration tools like IdentityCheck that bring identity verification directly into your existing software, your CRM, your workflows, no extra tabs or platforms required. This article breaks down how Jumio’s KYC solution works, what it covers, and how platforms like ours help you actually operationalise verification without bolting on disconnected software.
What Jumio KYC is and what it covers
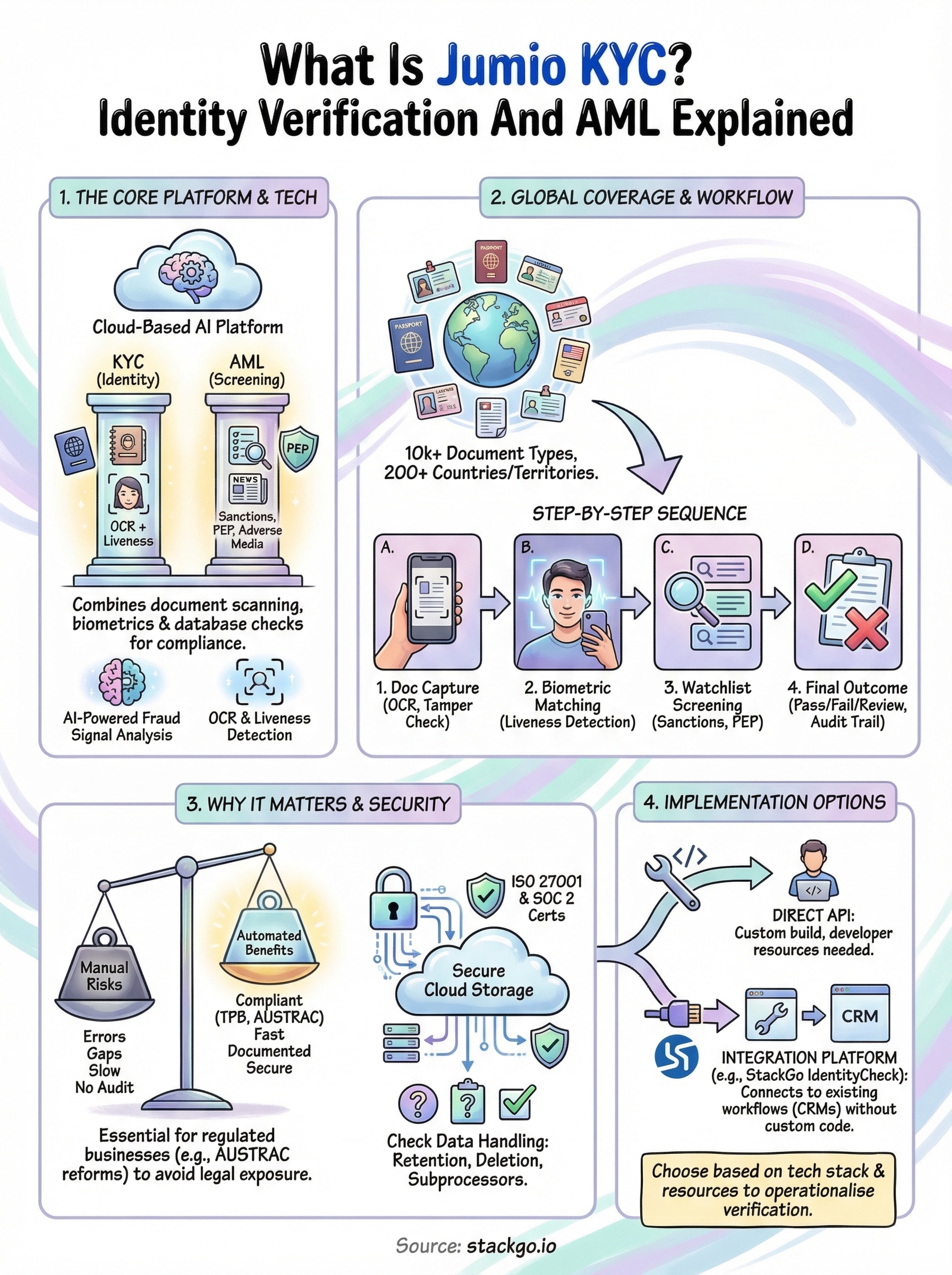
Jumio is a cloud-based identity verification platform built for businesses that need to confirm customer identities at scale. Jumio KYC combines AI-powered document scanning, biometric facial matching, and database checks into a single verification workflow. The result is a platform designed to reduce manual review time while helping businesses meet regulatory requirements across multiple jurisdictions.
The core technology Jumio uses
The verification engine relies on two primary technologies: optical character recognition (OCR) to extract data from identity documents, and liveness detection to confirm that the person submitting the document is physically present rather than using a photo or pre-recorded video to spoof the check. These two components work together to create a layered process that is significantly harder to deceive than traditional manual document review.
Getting both document authenticity and biometric matching right is what separates a compliant KYC process from one that creates regulatory exposure.
Beyond those two layers, the platform runs fraud signal analysis in the background, checking for signs of document tampering, expired credentials, or data inconsistencies extracted during the scan. This automated layer means your compliance team spends less time on routine checks and more time on edge cases that genuinely need human judgement.
What documents and regions Jumio covers
One practical strength of the platform is its breadth of coverage. It supports over 10,000 identity document types across more than 200 countries and territories, which makes it viable for businesses that onboard clients internationally. For Australian accounting firms or financial services providers dealing with overseas clients, this range reduces the need to manage multiple verification tools for different markets.

Supported document types include passports, national identity cards, driver licences, and residence permits, among others. Jumio also offers database verification and watchlist screening as part of its broader compliance suite, which extends beyond simple document checks into the AML territory that many regulated businesses are required to address.
KYC versus AML within Jumio’s offering
Jumio positions itself as a full-spectrum compliance tool rather than a document scanner with a narrow focus. On the KYC side, it verifies identity through document and biometric checks. On the AML side, it screens verified individuals against sanctions lists, politically exposed persons (PEP) databases, and adverse media sources. For businesses carrying both KYC and AML obligations, having these functions under one platform reduces the number of vendor relationships your team needs to maintain and review.
Why Jumio KYC matters for AML and onboarding
For regulated businesses in Australia, identity verification is not an optional extra. The Tax Practitioners Board (TPB) already requires accountants to verify client identities, and incoming AUSTRAC reforms under the AML/CTF regime are expanding those obligations further across accounting, legal, and financial services. Using a solution like Jumio KYC means you have a documented, automated process behind every check, which matters directly when regulators ask how you identify and screen clients.
The cost of getting onboarding wrong
Manual onboarding processes create two problems: they slow down your team and introduce gaps that compliance frameworks specifically target. When staff manually inspect documents, inconsistencies slip through, records stay incomplete, and the audit trail is thin. A structured verification platform gives you documented outcomes for every single check, which protects your practice if a client relationship is ever scrutinised by a regulator or auditor.
A poor onboarding process does not just frustrate clients; it creates legal exposure that no amount of internal review can fix after the fact.
Common risks in manual processes include:
- Incomplete identity records that cannot demonstrate compliance
- Inconsistent outcomes across different staff members reviewing documents
- No audit trail to defend decisions during a regulatory review
How AML obligations raise the bar further
AML screening goes beyond confirming someone’s identity to asking whether that person poses a financial crime risk. Sanctions lists, politically exposed persons (PEP) databases, and adverse media checks all add layers that a simple document scan cannot cover on its own. For businesses carrying AUSTRAC obligations, running both identity verification and AML watchlist screening through a single workflow reduces the chance of missing a required check and produces a cleaner, more defensible compliance record.
How Jumio KYC works step by step
Understanding the verification sequence helps you assess whether the process fits your client onboarding workflow. The Jumio KYC process runs in a fixed order: document capture comes first, biometric matching follows, and then the compliance screening layer completes the check. Each stage feeds into the next, which is what keeps the overall workflow coherent and auditable.

The initial document capture stage
Your client starts by submitting a photo or scan of their identity document through a web or mobile interface. The platform’s OCR engine reads the document fields automatically, extracting name, date of birth, document number, and expiry date. Jumio then cross-checks the extracted data against the document’s security features to detect signs of tampering or forgery before the process moves forward.
Biometric matching and liveness detection
Once the document passes the initial scan, your client completes a short biometric selfie check. The platform compares the selfie to the photograph on the submitted document and runs a liveness test to confirm the person is physically present during the session. This step is what separates a compliant modern verification flow from a basic document upload.
Liveness detection is a direct response to spoofing attempts that use printed photos or replayed video to pass identity checks.
Watchlist screening and final decision
After the document and biometric checks clear, Jumio runs the verified identity against sanctions lists, PEP databases, and adverse media sources. The platform then produces a single structured outcome, either a pass, a fail, or a manual review flag, along with a complete audit record of each check performed. Your team gets a defensible, documented result without running three separate tools to reach the same conclusion.
Security, privacy, and data handling to check
Before you deploy any identity verification platform, you need to understand exactly where client data goes and who controls it. This matters even more when you’re verifying clients under KYC and AML obligations, because a data breach involving identity documents carries both regulatory and reputational consequences your practice cannot afford.
Where your client data actually lives
When a client submits their identity document through Jumio KYC, that data travels to Jumio’s cloud infrastructure for processing and storage. Jumio holds certifications including ISO 27001 and SOC 2 Type II, which cover information security management and operational controls respectively. These certifications give you a baseline level of assurance that the platform follows documented security practices, but they are not a substitute for reviewing the specific data processing terms in your contract.
Your obligation to protect client data does not transfer to a vendor just because they hold a security certification.
You also need to confirm where Jumio stores data geographically, particularly if your clients are Australian residents covered by the Privacy Act 1988. Cross-border data flows involving personal information carry specific obligations, and your data processing agreement with any vendor needs to address those explicitly.
What to check before you sign
Several practical questions should guide your due diligence on any verification platform. Work through these before committing:
- Data retention periods: How long does Jumio store identity documents and biometric data after a check completes?
- Deletion rights: Can you request deletion of a specific client’s data, and what is the process?
- Subprocessor disclosure: Which third parties does Jumio share data with during the verification workflow?
- Breach notification timelines: What are the contractual commitments around notifying you if a data incident occurs?
Confirming these points protects both your clients and your compliance position if a regulator or auditor reviews your onboarding records.
How to implement Jumio KYC in your stack
Connecting Jumio KYC to your existing workflows depends on what your current tech stack looks like. Jumio provides API and SDK options for developers to embed verification directly into web or mobile applications, but most businesses in accounting or professional services are not running custom-built platforms. Your implementation path typically falls into one of two categories: direct API integration or a pre-built connector through an integration platform.
Direct API integration
Jumio’s REST API lets your development team build a custom verification flow inside your own application or client portal, giving you full control over the user experience and letting you retrieve structured results programmatically. This route requires dedicated developer resources and ongoing maintenance, including keeping your integration current each time Jumio updates its API. If your firm does not have in-house development capability, this path adds cost and complexity that most practices prefer to avoid.
Before committing to a direct API build, work through these three points:
- Available internal development resources and capacity
- Ongoing version maintenance and testing budget
- Timeline to go live against your compliance deadlines
Building a direct API connection gives you flexibility, but the maintenance burden sits entirely with your team from day one.
Using an integration platform instead
For businesses already running a CRM like HubSpot or Salesforce, an integration platform is a more practical path. Rather than building from scratch, you connect verification directly into your existing onboarding workflows without writing custom code.
StackGo’s IdentityCheck takes this approach: it reads contact data from your CRM, runs the identity check, and writes the verified outcome back into the contact record automatically. Your compliance data stays where your team already works, and you eliminate the need to manage a separate verification dashboard or manually transfer results between platforms.
Wrapping up and next steps
Jumio KYC gives you a structured, automated path through identity verification and AML screening, covering document checks, biometric matching, and watchlist screening in a single workflow. For regulated businesses in Australia, that kind of documented, auditable process is no longer optional. Whether you face TPB requirements now or AUSTRAC obligations under the incoming Tranche 2 reforms, how you verify clients matters as much as whether you verify them at all.
Picking the right platform is one step. Getting it to work inside your existing systems is the other. If your team runs on HubSpot, Salesforce, or a similar CRM, adding a standalone verification tool creates extra friction rather than removing it. StackGo’s IdentityCheck handles verification directly inside your current stack, so your compliance data stays connected to your client records from day one. See how IdentityCheck supports AUSTRAC Tranche 2 AML/CTF compliance or create a free account to test it against your own workflows.









