A single data breach involving client records can cost an Australian business hundreds of thousands of dollars in penalties, legal fees, and lost trust. For regulated firms, accountants, lawyers, financial advisers, the stakes are even higher because you’re handling sensitive identity documents and personal details every day. Knowing how to protect PII data isn’t optional; it’s a core compliance obligation under frameworks like the Australian Privacy Act and upcoming AUSTRAC AML/CTF requirements.
The problem is that most businesses don’t fail at policy. They fail at execution. PII ends up scattered across spreadsheets, CRM fields, email threads, and shared drives with no access controls. Staff copy passport scans into systems that were never designed to store them. Verification outcomes sit alongside raw personal data, and nobody has a clear audit trail. The gap between "we have a privacy policy" and "our systems actually enforce it" is where breaches happen.
At StackGo, we built our integration platform, and specifically our Privacy Layer within IdentityCheck, to address exactly this. Our tools let you verify client identities directly inside your existing CRM (like HubSpot or Salesforce) without storing PII in that CRM. Only MFA-authenticated admins can access sensitive information, and verification outcomes write back cleanly without exposing raw personal data to your broader team.
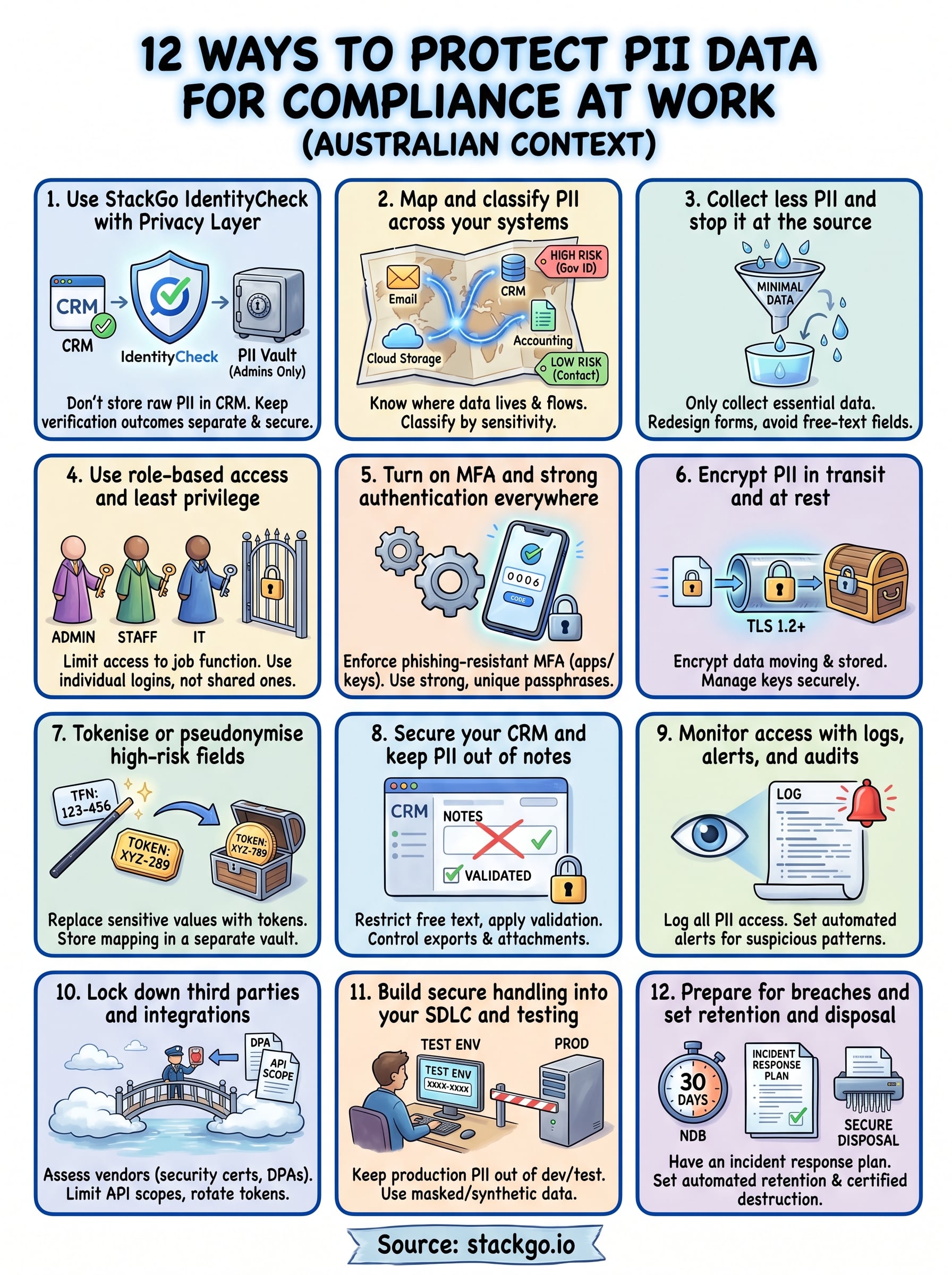
This article walks through 12 practical ways to protect PII data at work, covering everything from encryption and access controls to compliance-ready workflows. Whether you’re preparing for an audit or tightening up day-to-day processes, each method is something you can act on, not just read about. Let’s get into it.
1. Use StackGo IdentityCheck with Privacy Layer
The most direct answer to how to protect PII data in a client-facing business is to stop storing that data where it doesn’t need to live. Most compliance failures aren’t caused by hackers. They happen because sensitive personal information sits in systems that were never designed to protect it, like your CRM’s contact notes or deal records.
What this solves in day-to-day onboarding
When staff onboard a new client, the default habit is to copy passport details, tax file numbers, or driver’s licence scans into whatever system is open in front of them. That means raw PII ends up in CRM fields, email threads, and shared folders with no controls, no audit trail, and no expiry. IdentityCheck plugs directly into your existing CRM so your team can trigger a verification check from the contact record without ever manually handling or transcribing the raw documents themselves.
Your team’s workflow stays the same. They work inside the CRM they already use, and the compliance step happens in the background without requiring a separate platform or manual data entry.
How IdentityCheck keeps PII out of your CRM
IdentityCheck reads the relevant contact information, runs it through a compliant verification process, and then writes the outcome back to the CRM record, not the underlying personal data. The raw identity documents and personal details never touch your CRM. This means your CRM holds a compliance result (verified, failed, or pending) rather than a copy of someone’s passport or proof of address.
The verification outcome is what your business needs for compliance. The raw document is a liability if stored in the wrong place.
How to set permissions so only admins can view PII
StackGo’s Privacy Layer controls who can access sensitive information at all. You configure access at the admin level, requiring multi-factor authentication (MFA) before any PII becomes visible. Regular users see only what they need to complete their work, typically the verification status, while admins who need to review identity details must authenticate separately.
This structure keeps your broader team away from data they have no reason to access, which reduces both internal breach risk and your compliance audit footprint without adding friction to normal daily tasks.
Where this fits in KYC, AML, and background checks
IdentityCheck supports Know Your Customer (KYC) and Anti-Money Laundering (AML) workflows directly, with coverage across more than 200 countries and 10,000 document types. For Australian accounting firms preparing for AUSTRAC AML/CTF obligations, this means you can run compliant identity checks from inside your existing software rather than switching between multiple platforms or building custom integrations.
The same logic applies to background screening. The check result flows back to the relevant record without exposing unnecessary personal detail to staff outside the compliance function.
2. Map and classify PII across your systems
Before you can protect PII data, you need to know where it actually sits. Most businesses discover during an audit that personal information lives in far more places than anyone expected, from old email threads to custom CRM fields that were set up years ago and never reviewed.
What counts as PII in your business context
PII covers any information that can identify a specific individual, either on its own or in combination with other data. In a professional services firm, that typically includes full names, dates of birth, tax file numbers, passport details, residential addresses, and financial account information. Combinations matter too. A first name paired with a postcode and employer can be enough to identify someone, even if none of those fields seem sensitive in isolation.
How to find where PII lives and how it flows
Start by listing every system your business uses, your CRM, accounting software, email platform, cloud storage, and any third-party integrations. Then trace where client data enters each system, how it moves between them, and who touches it at each step. Interview the people who run onboarding and compliance workflows directly, because they know the shortcuts and workarounds that don’t appear in any documentation.

A data flow diagram doesn’t need to be complex. It just needs to reflect what actually happens, not what your process documents say should happen.
How to classify by sensitivity and risk
Group your PII into tiers based on the harm its exposure could cause. Government-issued identity documents and financial records sit at the top, while general contact details carry lower but still real risk. Use your classification tiers to decide which fields need encryption, which require restricted access, and which should not be stored at all.
How to keep the map current as systems change
Your PII map becomes outdated the moment you add a new tool or change a workflow. Assign a named owner for data mapping and build a review into your annual compliance calendar. Treat any new SaaS integration or form change as a trigger to update the map before it goes live, not after.
3. Collect less PII and stop it at the source
The simplest way to protect PII data is to never collect it in the first place. Every piece of personal information you gather becomes a liability you need to secure, manage, and eventually dispose of. Understanding how to protect PII data starts well before any security tool gets involved; it starts at your intake forms and client-facing processes.
How data minimisation reduces breach impact
When a breach occurs, the damage scales directly with how much data was exposed. If your systems hold three data points per client instead of fifteen, a breach affecting those records carries far less regulatory and reputational weight. The Australian Privacy Act’s principle of data minimisation exists for exactly this reason: collect only what your business genuinely needs to deliver its service and meet its legal obligations.
Collecting more than you need doesn’t make your compliance stronger. It makes your exposure larger.
How to redesign forms and intake steps
Review every form, questionnaire, and intake step your business uses to gather client information. For each field, ask whether removing it would prevent you from delivering the service or meeting a compliance requirement. If the answer is no, cut it. Pay particular attention to fields that were added informally over time, as these tend to capture data nobody actually uses.
How to avoid free-text fields that capture PII
Free-text fields are one of the most common sources of accidental PII storage. When staff can type anything into a notes field, they will, including passport numbers, health information, and financial details that were mentioned in passing. Replace open-ended fields with structured dropdowns and checkboxes wherever possible, and add guidance notes that explicitly tell staff what not to record there.
How to validate you still meet compliance needs
After trimming what you collect, confirm that your reduced dataset still satisfies your obligations under relevant frameworks like AML/CTF or the Privacy Act. Map each remaining field to a specific legal or operational requirement. If a field has no clear justification, remove it. This exercise also gives you documented evidence of intentional data minimisation, which strengthens your position during an audit.
4. Use role-based access and least privilege
Most PII breaches trace back not to external attackers but to internal staff accessing data they had no reason to see. Role-based access control (RBAC) limits what each person can view or edit based on their job function, which directly cuts your exposure when something goes wrong.
How least privilege prevents internal leaks
The principle of least privilege means every user gets only the access they need to do their job, nothing more. When a client onboarding coordinator can see verification outcomes but not the raw identity documents behind them, a compromised account or a curious employee causes far less damage. Knowing how to protect PII data inside your own systems starts with this principle, applied consistently across every tool your team uses.
The most common source of internal data exposure is access that was granted broadly and never reviewed.
How to design roles for operations, compliance, and IT
Map your teams to distinct access tiers before you configure anything. Operations staff typically need client status and workflow data. Compliance officers need verification results and audit logs. IT administrators need system configuration access but rarely need client PII. Define these tiers in writing, then build them directly into your platform settings so the structure is enforced automatically, not just documented.
How to remove shared accounts and generic logins
Shared credentials are a compliance liability because you cannot trace an action back to a specific person. Replace every shared account with individual named logins, and audit your systems for generic usernames like "admin" or "team@company". Individual accountability is a requirement under the Australian Privacy Act, which means your audit logs need to show exactly who accessed what and when.
How to run access reviews without slowing work
Schedule quarterly access reviews and assign a named owner to run them. Keep the process simple: export the user list from each system, compare it against your current staff roster, and remove or downgrade any access that no longer matches the person’s role. Build this task into your compliance calendar so it runs on a fixed schedule without waiting for a trigger event.
5. Turn on MFA and strong authentication everywhere
Authentication is your first line of defence before anyone touches PII. Weak or reused passwords remain one of the most common ways attackers gain access to business systems, and a single compromised account can expose every client record that account can reach. If you’re working out how to protect PII data at the system level, mandatory multi-factor authentication (MFA) across your entire stack is non-negotiable.
What to protect first across your stack
Start with the systems that hold the most sensitive client data: your CRM, identity verification platform, email, cloud storage, and accounting software. These are the highest-value targets, so enforce MFA there before anywhere else. Work outward from those priorities and document which systems have MFA enabled so nothing slips through during an audit.
How to choose MFA methods that resist phishing
Not all MFA is equal. SMS-based codes are the weakest option because they can be intercepted through SIM-swapping attacks. Authenticator apps like Google Authenticator offer a stronger alternative, and hardware security keys provide the highest level of protection for administrators who access particularly sensitive records.
Phishing-resistant MFA methods stop credential theft even when a staff member clicks a malicious link.
How to enforce strong passphrases and password managers
Require a minimum passphrase length of 14 characters and block the reuse of previous passwords. Provide your team with a shared or individual password manager so strong credentials become the path of least resistance, not a burden. Every account should have a unique passphrase generated and stored by the manager, never written on a sticky note or reused from a personal account.
How to handle break-glass access safely
Break-glass accounts give emergency access when normal authentication fails. Store these credentials in a physically secured location or a dedicated privileged access vault, and log every time they are used. Review break-glass usage after each incident and rotate the credentials immediately afterward to ensure access remains auditable and time-limited.
6. Encrypt PII in transit and at rest
Encryption converts readable personal data into unreadable ciphertext that only authorised parties can decode. It is one of the most reliable technical controls available for protecting PII data, and it needs to cover both data moving across networks and data sitting in storage. If your organisation is working through how to protect PII data comprehensively, encryption is not optional.
What encryption actually protects and what it does not
Encryption protects data from being read by anyone who intercepts or steals it without the correct key. It does not protect data from authorised insiders who misuse their access, and it does not prevent an application from leaking PII through poorly designed outputs. Treat encryption as one layer in a broader set of controls, not as a complete solution.
Encryption protects your data at rest and in transit, but it cannot replace strong access controls over who holds the keys.
How to cover web apps, APIs, and internal traffic
Enforce TLS 1.2 or higher across all web applications, APIs, and internal service connections. Disable older protocols like TLS 1.0 and SSL entirely, as these are vulnerable to known attacks. Your API gateway and any webhooks that carry personal data must also run over encrypted channels, including internal microservices that developers sometimes overlook.
How to cover databases, backups, and file storage
Apply encryption at the database level for any table or collection that holds PII, and extend that requirement to backups and file exports. Cloud providers like Microsoft Azure and AWS offer transparent data encryption for managed databases, which removes much of the operational complexity. Unencrypted backup files sitting in cloud storage buckets or on-premises drives are a common breach source that encryption directly addresses.
How to manage keys and access to keys
Store encryption keys in a dedicated key management service separate from the data they protect. Rotate keys on a scheduled basis and limit access to key management functions to a small number of named administrators. Logging every key access event gives you an auditable trail that supports both internal reviews and regulatory inquiries.
7. Tokenise or pseudonymise high-risk fields
Tokenisation replaces a real PII value with a surrogate token that carries no intrinsic meaning. A tax file number becomes a random string, and that string is what lives in your business systems. Pseudonymisation works similarly by replacing direct identifiers with coded references that can only be reversed using a separate key. Both techniques reduce the exposure surface significantly, and both are worth understanding when you’re working out how to protect PII data beyond basic encryption.
When tokenisation beats encryption for PII exposure
Encryption still leaves ciphertext in the same field where PII would otherwise sit. Tokenisation removes the sensitive value from your business system entirely, leaving only a reference. This means a breach of your CRM or accounting software reveals nothing useful to an attacker because the original values never existed there in the first place.
Tokenisation removes the target rather than hiding it; an attacker who breaches your CRM finds tokens, not personal data.
What to tokenise first in client records
Focus on government-issued identifier fields first, including tax file numbers, passport numbers, and driver’s licence numbers. Financial account details and biometric references follow closely behind. These fields carry the highest re-identification risk and the most serious consequences under Australian privacy and AML/CTF frameworks if they are exposed.
How to separate the token vault from business systems
Store the mapping between tokens and real values in a dedicated vault that sits on a separate network segment with its own access controls and logging. Your CRM should never be able to query the vault directly. Only authorised compliance processes with specific authenticated calls should reach it.
How to avoid re-identification through dataset joins
Even anonymised datasets can expose individuals when multiple fields are combined. A token paired with a postcode, employer, and date of birth can re-identify someone in a small population. Audit any reporting or analytics exports that combine tokenised records with other attributes, and remove fields that create unnecessary re-identification risk before those exports leave your controlled environment.
8. Secure your CRM and keep PII out of notes
Your CRM was built to manage relationships, not to store passport scans, tax file numbers, or copies of identity documents. When staff use it as a filing system for sensitive client data, you end up with PII scattered across notes fields, attachments, and deal records with no controls and no clear audit trail. Locking down your CRM is one of the most practical steps in learning how to protect PII data across a professional services business.
Why CRMs become accidental PII warehouses
Staff default to whatever is fastest, and in most firms, the CRM notes field is always open. Over time, it fills with dates of birth, account numbers, and verification details added during a call and never removed. These records accumulate without any retention schedule or access restriction, creating a growing liability that your privacy policy does nothing to address.
How to set field-level controls and redaction rules
Configure your CRM to restrict which fields can accept free text and apply validation rules that flag or block entries matching patterns like tax file numbers or passport formats. Where your platform supports it, enable field-level security so sensitive fields are visible only to users with explicit permission. Remove notes fields from any record type that does not require them.
How to control attachments, exports, and mobile access
Disable bulk data exports for standard user roles and require admin approval for any export that includes personal data fields. Restrict mobile app access to read-only views for roles that do not need full client records on the go, and prevent document attachments from syncing to personal devices through mobile device management policies.
How to keep audit trails without storing raw PII
Log who accessed each record, when, and what action they took, without those logs containing the raw personal data themselves.
Your CRM should record access events and field changes in a structured log that compliance teams can review. Store verification outcomes rather than source documents, and configure your system to automatically remove or archive records that have passed their retention period.
9. Monitor access with logs, alerts, and audits
Understanding how to protect PII data doesn’t stop at access controls and encryption. You need ongoing visibility into what happens after those controls are in place, because misconfigured permissions and insider misuse both leave traces that only logs can reveal.
What to log for PII access and processing
Log every event where a user reads, modifies, exports, or deletes a record containing personal information. Capture the user ID, timestamp, action type, and the record affected. Your logging should cover CRM activity, identity verification requests, bulk exports, and admin privilege use as a minimum baseline.
Logs are only useful if they capture enough context to reconstruct exactly what happened during an incident.
How to detect suspicious access patterns early
Configure automated alerts for patterns that deviate from normal behaviour, such as a single account accessing hundreds of client records in a short window, or a user downloading bulk exports outside business hours. Most cloud platforms and SaaS tools offer built-in alerting rules; use them rather than relying on manual log reviews to catch problems.
How to review logs without drowning in noise
Set a fixed weekly review schedule and focus on high-priority alert categories rather than reading raw logs line by line. Assign a named person to own the review process and build a short checklist covering failed logins, privilege escalations, and bulk data events. Reducing alert volume through well-tuned thresholds makes the review sustainable without creating gaps.
How to document evidence for compliance and incidents
Retain log files for a minimum of 12 months, or longer if your regulatory obligations require it. Store logs in a separate, write-protected location so they cannot be tampered with after an incident. During an audit or a breach investigation, structured and intact logs are the clearest evidence that your controls were operating as intended.
10. Lock down third parties and integrations
Every SaaS tool you connect to your core systems creates a new path for PII to leave your control. Third-party integrations are one of the most overlooked areas when businesses work through how to protect PII data, because the risk sits outside your direct visibility and grows with every new connection you add.
Where PII leaks in SaaS connections and workflows
Data leaks through integrations in ways that are easy to miss. Automation workflows that pass contact records between platforms often carry more fields than the receiving system needs, dropping full names, addresses, and identity details into environments with weaker controls. Common leak points include:
- Sync tools that export full contact records when only a status field is needed
- Email marketing integrations that pull raw client data into platforms with minimal access controls
- Reporting connectors that carry PII into business intelligence tools without field restrictions
How to assess vendors for security and privacy controls
Before connecting any third-party tool that touches client records, ask the vendor for security certifications and privacy documentation, such as ISO 27001 or SOC 2 reports. Confirm they store data in Australia or a jurisdiction with equivalent protections, and verify they hold a current privacy policy that covers how they handle PII on your behalf.
A vendor’s popularity is not a substitute for documented evidence of their security and privacy practices.
How to set contracts, DPAs, and cross-border safeguards
Require a Data Processing Agreement (DPA) from every vendor that handles personal data on your behalf. Under Australian Privacy Act obligations, this becomes a legal requirement when you share client PII with overseas entities. The DPA must specify what data is processed, for what purpose, and how it is deleted when the relationship ends.
How to control API scopes, tokens, and webhooks
Limit each API connection to the minimum permission scope it needs to function, and rotate tokens on a fixed schedule. Revoke access immediately when an integration is decommissioned, and audit active webhook endpoints quarterly to confirm they point to current, secured destinations and carry no more data than the receiving system requires.

11. Build secure handling into your SDLC and testing
Most development and testing environments sit outside the controls you apply to production, yet they regularly contain real client data that engineers copied across to debug a problem. This is one of the quieter ways that PII ends up unprotected, and it is entirely avoidable with the right practices built into your software development lifecycle from the start.
How to prevent PII from entering dev and test
Establish a hard rule that production PII never moves into development or test environments, and enforce it through access controls rather than policy documents alone. Restrict which roles can export data from production, and configure your data pipelines to block transfers to non-production destinations by default. When developers need realistic data volumes to test against, synthetic data generation tools provide representative datasets without pulling real client records.
How to mask data and create safe test datasets
Data masking replaces real values with realistic but fictitious substitutes that preserve the format and structure your application expects. A masked tax file number still looks like a valid tax file number, so your tests run accurately without exposing anyone’s actual details. Build masked dataset generation into your release process so every environment refresh uses clean data automatically.
Masked data lets your team test thoroughly without turning every developer workstation into a PII risk.
How to catch leaks in code reviews and CI checks
Add automated secret scanning and PII pattern detection to your continuous integration pipeline. Tools integrated at the repository level flag commits that contain values matching identity document formats, financial account numbers, or authentication credentials before they merge. Make PII leak detection a blocking check in the same way you treat failed unit tests.
How to reduce risk from misconfigurations and secrets
Misconfigurations are a primary cause of cloud storage buckets and databases becoming publicly accessible without anyone realising. Run infrastructure-as-code scans before deployment to catch overly permissive settings, and store all credentials in a dedicated secrets manager rather than environment variables or configuration files checked into version control. Understanding how to protect PII data at this layer means treating misconfiguration as a compliance risk, not just a technical inconvenience.
12. Prepare for breaches and set retention and disposal
No set of controls eliminates breach risk entirely. The final piece of how to protect PII data at work is knowing exactly what you will do when something goes wrong, and making sure personal data does not linger longer than your legal obligations require.
How to build a PII-focused incident response plan
Your incident response plan should name a specific person responsible for leading the response and document the first steps your team takes within the first hour of a suspected breach. Cover how you contain the exposure, preserve evidence, and notify affected individuals and regulators if required. Test this plan with a tabletop exercise at least once a year so staff know their roles before a real incident forces them to act.
How to meet Notifiable Data Breaches expectations
Australia’s Notifiable Data Breaches scheme requires eligible organisations to notify the Office of the Australian Information Commissioner and affected individuals when a breach is likely to cause serious harm. Your plan must include a clear assessment process to determine whether a breach meets that threshold, and you need to move quickly, because the scheme sets a 30-day limit from when you become aware of an eligible breach to complete that assessment and notify where required.
Delay in assessing a breach is treated as a compliance failure in its own right, separate from the breach itself.
How to set retention schedules that match obligations
Define a specific retention period for each category of PII your business holds, tied directly to the legal or operational requirement that justified collecting it. Build automated archiving or deletion triggers into your systems where possible so records do not survive past their scheduled expiry through simple inaction or oversight.
How to destroy or de-identify data with confidence
Deleting a file or database record does not always remove the underlying data. Use certified data destruction methods for physical media and configure your cloud platforms to purge records from backups within a defined window after deletion. For records you need to retain in aggregate, apply de-identification that removes all direct and indirect identifiers, and document the method used so you can demonstrate compliance during an audit.
Next Steps
Knowing how to protect PII data is one thing; putting it into practice across your systems is another. The 12 methods in this article cover every layer of that problem, from data minimisation and access controls through to breach response and secure disposal. No single control is enough on its own, but working through these steps systematically gives you a defensible, auditable position under the Australian Privacy Act and AUSTRAC’s AML/CTF requirements.
The fastest place to start is your client onboarding workflow, because that is where raw personal data enters your business and where the most common controls failures happen. If your team runs identity checks manually or stores verification documents inside your CRM, StackGo’s IdentityCheck removes that risk directly. You can run compliant KYC and AML checks inside your existing software with AUSTRAC Tranche 2 support without changing your workflow or adopting a separate platform. Test it with a free account at identity.stackgo.io/signup.









